Malicious Extensions Copies Legitimate Apps; Chrome Under Spotlight
Chrome under spotlight
Continue ReadingSummary : Several high severity vulnerabilities were recently identified in Google Chrome, impacting core components such as the V8 JavaScript engine, Chrome Updater, DevTools and Digital Credentials module.
The primary high-severity vulnerability, a Type Confusion bug in the V8 engine (CVE-2025-13630), could allow attackers to achieve memory corruption that may lead to remote code execution via malicious web content. Google says that that it handed out $11,000 for the V8 vulnerability and $3,000 for the Google Updater bug.
| Severity | High |
| CVSS Score | Not Published |
| CVEs | CVE-2025-13630, CVE-2025-13631, CVE-2025-13632, CVE-2025-13633 & 9 other CVEs. |
| POC Available | No public PoC at release time |
| Actively Exploited | No confirmed exploitation |
| Exploited in Wild | Not confirmed for Chrome 143 |
| Advisory Version | 1.0 |
Overview
Other vulnerabilities like privilege escalation, unauthorized actions or browser misuse have been patched in the latest Chrome update. Administrator and users are strongly urged to update to the chrome 143 release immediately.
| Vulnerability Name | CVE ID | Product Affected | Severity | Fixed Version |
| Type-Confusion Vulnerability in V8 JavaScript Engine | CVE-2025-13630 | Chrome | High | v143.0.7499.40/41 |
| Inappropriate Implementation in Google Updater | CVE-2025-13631 | Chrome | High | v143.0.7499.40/41 |
| Inappropriate Implementation in DevTools | CVE-2025-13632 | Chrome | High | v143.0.7499.40/41 |
| Use-After-Free Vulnerability in Digital Credentials | CVE-2025-13633 | Chrome | High | v143.0.7499.40/41 |
Technical Summary
Several high-severity vulnerabilities were addressed in Google Chrome versions prior to 143.0.7499.40/41. The most critical involves a type of confusion flaw in the V8 JavaScript engine, which permits remote attackers to exploit improper object type handling, causing heap corruption when a user accesses a specially crafted webpage and potentially leading to remote code execution under certain conditions.
Other significant issues include a flawed update mechanism that may trigger unintended actions during updates, a logic error within DevTools that could result in tool misuse or unintended execution paths, and a use-after-free vulnerability in the digital credential processing components that may cause memory corruption and browser instability.
Together, these flaws can be exploited to bypass update protections, escalate privileges, disrupt developer tools, or compromise sensitive credential operations.
| CVE ID | System Affected | Vulnerability Details | Impact |
| CVE-2025-13630 | Chrome 142 and prior | Type Confusion in V8 engine allows crafted JavaScript to trigger memory corruption leading to possible arbitrary code execution | Remote Code Execution |
| CVE-2025-13631 | Chrome 142 and prior | Inappropriate implementation in Chrome Updater may allow unauthorized update-related actions | Privilege Escalation |
| CVE-2025-13632 | Chrome 142 and prior | Inappropriate implementation in DevTools may allow unintended function execution | Unauthorized Code Paths / Sandbox Interaction |
| CVE-2025-13633 | Chrome 142 and prior | Use-after-free in Digital Credentials processing leads to memory corruption | Memory Corruption / Crash |
Remediation:
Here are some recommendations below
Conclusion:
Chrome 143 patches critical flaws in the JavaScript engine, updater, DevTools, and credentials, preventing remote code execution and memory corruption.
Users and administrators are strongly advised to promptly upgrade to the latest Chrome version and implement security best practices such as enforcing automatic updates, enabling endpoint exploit protections and monitoring for any signs of exploitation to maintain a strong defense against potential attacks.
Additionally, Google announced that the browser’s Extended Stable channel has been updated to version 142.0.7499.226 for Windows and macOS.
References:
Summary : Security Advisory: Google recently rolled out an update for Chrome to address two high & and one medium severity vulnerabilities.
| OEM | |
| Severity | High |
| CVSS Score | 8.0 |
| CVEs | CVE-2025-11458, CVE-2025-11460, CVE-2025-11211 |
| POC Available | No |
| Actively Exploited | No |
| Exploited in Wild | No |
| Advisory Version | 1.0 |
Overview
A heap buffer overflow in the Sync component and a use-after-free (UAF) vulnerability in the Storage component have been fixed, along with other security issues.
Users and administrators are advised to apply the latest patch as soon as possible to ensure their systems remain secure.
| Vulnerability Name | CVE ID | Product Affected | Severity | Fixed Version |
| Heap Buffer Overflow in Sync | CVE-2025-11458 | Chrome (Windows, Mac, Linux) | High | 141.0.7390.65/66 |
| Use-After-Free in Storage | CVE-2025-11460 | Chrome (Windows, Mac, Linux) | High | 141.0.7390.65/66 |
| Out-of-Bounds Read in WebCodecs | CVE-2025-11211 | Chrome (Windows, Mac, Linux) | Medium | 141.0.7390.65/66 |
Technical Summary
Google released an update for the Chrome Stable channel, addresses three significant security vulnerabilities related to memory safety. The update addresses multiple critical memory-related vulnerabilities within Chrome’s core components.
These include a flaw that could allow attackers to corrupt memory during browser data synchronization, potentially enabling arbitrary code execution, and another vulnerability in the storage system that involves improper memory handling after an object is freed, which could also lead to exploitation through crafted web content.
Additionally, a medium-severity issue was fixed in the media processing API that could cause exposure of sensitive memory or impact browser stability when handling certain media files. These fixes are part of ongoing efforts to improve browser security by mitigating risks of remote code execution, data exposure, and crashes.
| CVE ID | Component Affected | Vulnerability Details | Impact |
| CVE-2025-11458 | Chrome Sync component | Heap buffer overflow in the Sync component could allow memory corruption and potentially enable arbitrary code execution when handling synchronization data. | Remote Code Execution / Data Leakage |
| CVE-2025-11460 | Chrome Storage component | Use-after-free in the Storage component could allow attackers to access freed memory, potentially leading to code execution or information disclosure. | Remote Code Execution / Browser Instability |
| CVE-2025-11211 | Chrome WebCodecs API | Out-of-bounds read in the WebCodecs API could expose memory contents or crash the browser when processing malformed media inputs. | Memory Disclosure / Browser Crash |
Recommendations
Update Chrome immediately to the following versions:
Here are bellow recommended actions
Conclusion:
This update reflects Chrome’s continued commitment to robust browser security by addressing multiple critical memory vulnerabilities that could otherwise be exploited for remote code execution, data exposure, or browser instability.
Promptly applying updates is essential to reduce potential attack surfaces, maintain browser stability, and safeguard user data against emerging threats.
References:
Summary
A newly-patched zero-day vulnerability in Google Chrome CVE-2025-2783 which was exploited in the wild by a threat actor TaxOff, leading to the deployment of Trinper which an advanced backdoor.
The CVE-2025-2783 exploited a sandbox escape vulnerability within Google Chrome’s Mojo IPC (Inter-Process Communication) framework, which allowed attackers to bypass the browser’s security sandbox and lead to RCE.
TaxOff Threat Actor
TaxOff is a highly sophisticated Advanced Persistent Threat (APT) group primarily targeting government organizations which is known for its use of advanced social engineering tactics, often involving phishing campaigns that exploit themed around financial reporting and regulatory compliance.
The CVE-2025-2783 vulnerability was first detected in March 2025 after Kaspersky reported real-world exploitation.
TaxOff used a phishing-based delivery method, which involved embedding a malicious link in emails masquerading as invitations to legitimate events like the Primakov Readings forum.
Once the link was clicked, the CVE-2025-2783 exploit was triggered, leading to the deployment of the Trinper backdoor. It was a one-click compromise that delivered a highly tailored payload with surgical precision.
Trinper Backdoor
This is a multi-threaded C++ backdoor that collected host data, logged keystrokes, exfiltrated targeted documents like document, excel or pdf files and maintained remote access.
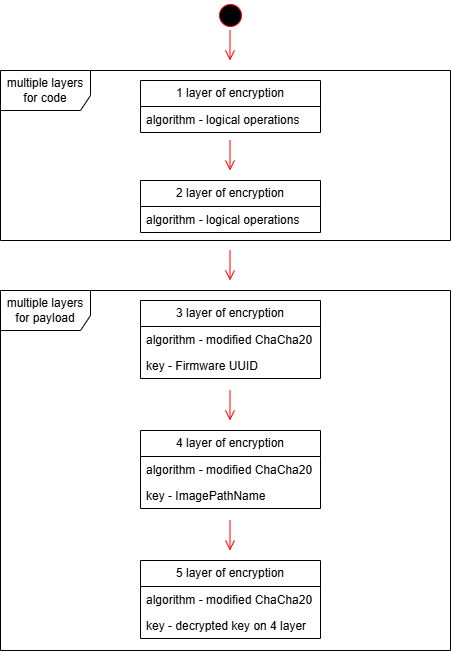
But this wasn’t just a “plug-and-play” backdoor. Trinper’s loader employed five layers of encryption, utilizing ChaCha20, modified BLAKE2b hashes, and even machine-specific environmental checks. It was decrypted only on intended systems, using unique hardware identifiers like firmware UUIDs and PEB structures.
Source: global.ptsecurity.com
Interestingly, researchers found that Team46, a different APT group shares many similarities with TaxOff in terms of TTPs. This overlap raises the possibility that TaxOff and Team46 are the same group operating under different aliases.
Both groups have used PowerShell-based loaders and Cobalt Strike as their primary exploitation vectors.
This flaw allows threat actors to:
Recommendation
The rapid exploitation of CVE-2025-2783 highlights the critical importance of timely patch management. Google released a fix for this vulnerability in March 2025, and all users are strongly advised to update their Chrome browsers to the latest version immediately.
In addition to patching, organizations should implement the following defensive measures
References:
Summary : Security Advisory
Google has released a critical out-of-band security update for its Chrome browser to address CVE-2025-5419.
Rated as high-severity zero-day vulnerability in the V8 JavaScript engine that is currently being actively exploited in the wild.
| OEM | |
| Severity | HIGH |
| CVSS Score | 8.8 |
| CVEs | CVE-2025-5419 |
| Actively Exploited | Yes |
| Exploited in Wild | Yes |
| Advisory Version | 1.0 |
Overview
This vulnerability allows attackers to execute arbitrary code on users’ systems through specially crafted web content, making it a serious threat requiring immediate attention.
In addition to the zero-day fix, this update also includes a patch for CVE-2025-5068, a medium severity use-after-free vulnerability in Blink, chrome’s rendering engine.
While less critical, such flaws can still result in memory corruption and possible code execution.
| Vulnerability Name | CVE ID | Product Affected | Severity | Fixed Version |
| Out-of-bounds memory access vulnerability | CVE-2025-5419 | Google Chrome | High | 137.0.7151.68/.69 (Win/Mac), 137.0.7151.68 (Linux) |
Technical Summary
This high-severity vulnerability is caused by an out-of-bounds read and write weakness in Chrome’s V8 JavaScript engine, reported one week ago by Clement Lecigne and Benoît Sevens of Google’s Threat Analysis Group.
This flaw affects the V8 JavaScript engine and allows attackers to execute arbitrary code via crafted web content.
| CVE ID | System Affected | Vulnerability Details | Impact |
| CVE-2025-5419 | Chrome (all platforms) | Out-of-bounds read and write in the V8 JavaScript engine; triggered via malicious HTML | Arbitrary code execution, memory compromise, remote attack |
Remediation:
Apply Patches Promptly: Upgrade to Chrome version 137.0.7151.68/.69 or later for Windows and macOS, and 137.0.7151.68 or later for Linux to mitigate the vulnerabilities.
General Recommendation:
Conclusion:
CVE-2025-5419 poses a significant security risk with confirmed active exploitation in the wild.
Google’s swift action highlights the urgency of this threat. All users are strongly advised to update their Chrome browsers immediately. Delaying this update could expose systems to compromise through malicious web content exploiting this zero-day vulnerability.
While Chrome will automatically update when new security patches are available, users can speed up the process by going to the Chrome menu > Help > About Google Chrome, letting the update finish, and clicking the ‘Relaunch’ button to install it immediately.
References:
For the month of May 2025 here are the Top News including Security Advisory & Blogs
Tesla Model 3 VCSEC Vulnerability Allows Remote Code Execution via TPMS Exploit
A high-severity vulnerability (CVE-2025-2082) in Tesla Model 3’s Vehicle Controller Security (VCSEC) module allows attackers within wireless range to remotely execute arbitrary code by exploiting a flaw in the Tire Pressure Monitoring System (TPMS)
The FBI issued an alert warning of ongoing exploitation of 13 EOL Linksys/Cisco routers by cybercriminal groups operating the 5Socks and Anyproxy services.
Microsoft May 2025 Patch Tuesday Released; Fixed 83 Vulnerabilities, Including 5 Zero-Days
Microsoft addressed 83 vulnerabilities across its product suite. Among them are 5 zero-day vulnerabilities have been confirmed as actively exploited in the wild. The updates span Windows components, Office, Visual Studio, and other core services.
11 vulnerabilities were rated critical, emphasizing the importance of timely remediation especially for enterprise environments.
5 non-Microsoft CVEs included
78 Microsoft CVEs addressed
Critical SAP NetWeaver Vulnerabilities Addressed in May 2025 Patch – Immediate Action Required
SAP has released critical security updates for its May 2025 patch, including fixes for two actively exploited zero-day vulnerabilities in SAP NetWeaver Visual Composer.
SAP Visual Composer is not installed by default, however it is enabled because it was a core component used by business process specialists to develop business application components without coding.
CISA is officially changing the way it disseminates online security updates and guidance.
CISA says the enhanced information dissemination system will from now on use social media and email only to disperse cybersecurity alerts and advisories, saving its landing page for more critical warnings on May 12.
Updates on May 13
Just a day after announcing it was changing the way it sent out alerts, CISA has changed its mind and reverted back to its old system of putting everything on its website.
“We recognize this has caused some confusion in the cyber community,” the site now reads. “As such, we have paused immediate changes while we re-assess the best approach to sharing with our stakeholders.”
Zero-Day Threat in Chrome’s Loader Component (CVE-2025-4664) – CISA Flags Urgent Risk
A zero-day vulnerability (CVE-2025-4664) in Google Chrome’s Loader component has been actively exploited in the wild.This flaw allows attackers to bypass security policies, leak cross-origin data, and potentially execute unauthorized code. CISA has added this vulnerability to its Known Exploited Vulnerabilities (KEV) catalog, urging immediate patching.
Summary : A zero-day vulnerability (CVE-2025-4664) in Google Chrome’s Loader component has been actively exploited in the wild.
| OEM | |
| Severity | Medium |
| CVSS Score | 4.3 |
| CVEs | CVE-2025-4664 |
| Actively Exploited | Yes |
| Exploited in Wild | Yes |
| Advisory Version | 1.0 |
Overview
This flaw allows attackers to bypass security policies, leak cross-origin data, and potentially execute unauthorized code. CISA has added this vulnerability to its Known Exploited Vulnerabilities (KEV) catalog, urging immediate patching.
| Vulnerability Name | CVE ID | Product Affected | Severity | Fixed Version |
| Insufficient Policy Enforcement vulnerability | CVE-2025-4664 | Google Chrome | Medium | 136.0.7103.113/.114 (Win/Mac), 136.0.7103.113 (Linux) |
Technical Summary
CVE-2025-4664 is a zero-day vulnerability found in the Chrome Loader component due to insufficient policy enforcement.
It enables remote attackers to bypass browser security controls using crafted HTML content, possibly leaking cross-origin data or achieving sandbox escape. The bug has been actively exploited in the wild.
A second high-severity flaw, CVE-2025-4609, was also addressed in this update, involving an incorrect handle in the Mojo IPC layer, which can lead to memory corruption or privilege escalation.
| CVE ID | System Affected | Vulnerability Details | Impact |
| CVE-2025-4664 | Chrome (Windows, Mac, Linux) | Insufficient policy enforcement in Loader enables cross-origin data leaks via crafted HTML. | Data leakage, sandbox escape, potential code execution |
Remediation:
Conclusion:
The active exploitation of CVE-2025-4664 highlights the urgent need for rapid security response and patch management. With acknowledgment from CISA and public disclosure by @slonser_, this zero-day poses a real and present threat to users of Chrome and other Chromium-based browsers.
Organizations should take immediate action to patch affected systems and monitor for signs of compromise.
Regular browser updates and proactive vulnerability management are essential to mitigating such critical security risks.
References:
| OEM | Google Chrome |
| Severity | High |
| CVSS | 8.8 |
| CVEs | CVE-2025-2476 |
| Exploited in Wild | No |
| Patch/Remediation Available | Yes |
| Advisory Version | 1.0 |
Overview
Google Chrome’s Lens component has been found to have a critical use-after-free vulnerability (CVE-2025-2476) that impacts Linux, Mac, and Windows.
This vulnerability might compromise user systems by enabling remote attackers to run arbitrary code. To lessen the danger, Google has issued security patches.
| Vulnerability Name | CVE ID | Product Affected | Severity | Fixed Version |
| Use after free Vulnerability | CVE-2025-2476 | Google Chrome | High | 134.0.6998.117/.118 |
Technical Summary
The vulnerability exists due to a use-after-free (UAF) condition in Chrome’s Lens component. This occurs when a program continues to use memory after it has been freed, potentially leading to arbitrary code execution or system compromise. Attackers can exploit this flaw using specially crafted HTML pages that trigger heap corruption.
| CVE ID | System Affected | Vulnerability Details | Impact |
| CVE-2025-2476 | Windows, Mac, Linux | Use-after-free vulnerability in Chrome’s Lens component, leading to heap corruption and potential arbitrary code execution. | Remote code execution |
Remediation:
Google has restricted detailed vulnerability information until a majority of users have applied the fix to prevent potential exploitation.
A vulnerability has been discovered in Google Chrome, which could allow for arbitrary code execution. Successful exploitation of this vulnerability could allow for arbitrary code execution in the context of the logged-on user.
Depending on the privileges associated with the user an attacker could then install programs; view, change, or delete data; or create new accounts with full user rights.
Users whose accounts are configured to have fewer user rights on the system could be less impacted than those who operate with administrative user rights.
Manage default accounts on enterprise assets and software, such as root, administrator, and other pre-configured vendor accounts.
There are currently no reports of the vulnerability being exploited in the wild.
Conclusion:
The possibility of remote code execution makes CVE-2025-2476 a serious security risk. It is highly recommended that users upgrade their Chrome browsers ASAP.
This vulnerability emphasizes how crucial it is to keep up with security patches on time and to be vigilant about new online threats.
References:
Image
Recent Comments