Iran & Israel war shaping cyber warfare; Hacktivism a tool used widely for Proxy Warfare
Iran & Israel war shaping cyber warfare; Hacktivism a tool used widely for Proxy Warfare
The latest in geo -politics is Israeli air strikes on Iran that triggered Hacktivist to attack and they chose social media platform to announce their activities ‘The Telegram platform’. Now cyber war fare is taking a different path and has no borders and enemy is not visible. One shot of attack is enough to bring down and cripple and entire system starting from banking systems to power grids.
Hacktivist group often uses Telegram as first approach to share about their cyber-attacks and victims list. The hacktivist group DieNet claimed that they will attack Israeli radio stations and announced it in Telegram.
Israeli cyber officials expect more spear-phishing, malware and similar patterns of attack attempts in the days ahead. Iran is currently engaged in a cyber-conflict with Israel and uses major two hacktivist groups that helps conduct destructive cyber-attacks, linked to Iran’s Ministry of Intelligence and Security (MOIS).
According to NSFOCUS Fuying Lab, hacker groups targeting Israel and Iran have been active since 2025. Up to now, there are about 170 hacker groups attacking Israel, with about 1,345 cyber attacks on Israel, including about 447 cyber attacks launched against Israel after the conflict broke out. (The Hacktivist Cyber Attacks in the Iran-Israel Conflict – Security Boulevard)
In the past Russia has used “hacktivism” as a tool for proxy warfare for various forms of cyber activities to create fear and uncertainty on their opponent.
The Iranian Cyber Units or forces are mostly linked to MOIS and IRGC the hackers group who use fake identities or front groups to hide their state connections.
Surge in Disruptive Cyber Operations
According to Radware, a global cybersecurity provider, Israel has faced an average of 30 DDoS attacks per day since the conflict’s onset. These attacks primarily target government and public institutions (27%), manufacturing (20%), telecommunications (12%), and media platforms (9%).
DDoS operations overload online services, rendering them inaccessible and often accompany website defacements and data leaks to maximise disruption during crises.
The pro-Iranian hacker group’s attacks on Israel peaked on June 16, the day after the Israeli military’s “massive strike” against multiple Iranian weapons production sites, including surface-to-surface missile production sites, detection radar bases and surface-to-air missile launchers in Tehran.
The targets of attack were mainly concentrated on Israeli government and public sector, national defense, aerospace, education and other industries.
The War in disguise-fought with malicious coding
Now along with tanks and war machineries, another kind of war is being simultaneous wagged i.e. cyber warfare. Here it is unconventional warfare no border no clear enemy. Everything is in disguise to create more sensation and install fear. This is being conducted by either by various state sponsored espionage or individual groups who are posing challenge for nation security.
And sometimes this kind of cyber-attack is fatal as malicious code on any application software can damage the system. Imagine doctors not able to open the required files in their system to check patient history on time, due to swarm of malicious code being pushed in their system and is life threatening for the patient as there is a delay to start treatment.
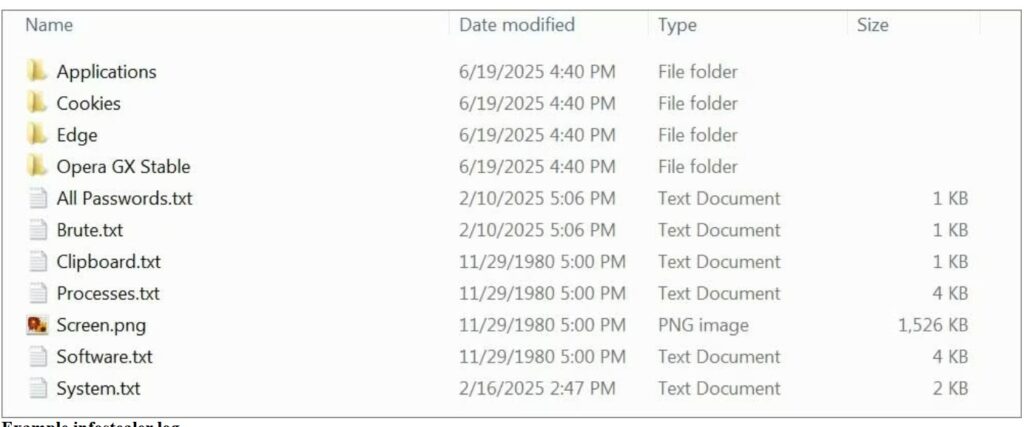
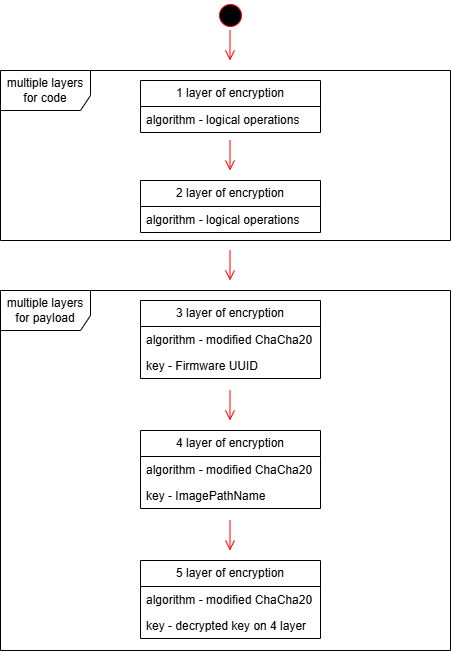
Again malicious code threats are hidden in software and mask their presence to evade detection by traditional security technologies.
Once any encrypted coding being pushed by threat actors inside organizations network, they can enter network and mail, overload with email messages, steal data like passwords and even reformat hard drives.
Hacktivist are now more empowered and Cyber warfare is now fought in disguise to exert influence and destabilize adversaries. Many methods used by Iran in destructive cyber attacks mirror those used by large ransomware groups, such as abusing vulnerabilities in VPN applications to gain entrance.
Emergence of New Axis in Cyber warfare
Those countries who lack in having a resilient cyber security infrastructure or organizations particularly fragile are soft targets becomes unintended battlegrounds in the global cyber war.
They make the easy victims either via hacking; data theft, cyber extortion and sometimes major cyber-attack that can sabotage their government systems.
If your capability suffers and able to provide effective defense then remaining vulnerable is an option slowly loosing creditability.
Either as a organization or country this growing disparity in cyber defense capacity has emerged as a new axis of global inequality and thriving grounds for threat actors.
The wave of cyber activity in this present state of Iran and Israel war, highlights how modern conflicts extend beyond physical battlegrounds. Attacks on infrastructure highlights the strategic importance of digital resilience.
Iranian state-sponsored hackers, particularly the APT35 group (also known as Charming Kitten), reportedly used AI to enhance their cyberattacks.
According to Check Point, these operations targeted Israeli cybersecurity experts, computer scientists, and tech executives with sophisticated phishing attempts. The attackers used fake messages and emails designed to trick people into sharing sensitive information, along with realistic decoys and fake login pages mimicking Google’s.
Here are recommendations to secure your networks against cyber-attacks, happening in disguise. How to improve organizational resilience.
- First have clear visibility across your network as traffic flows, without visibility it is not possible to stop attack. You can’t defend if your enemy is not visible. Once you have visibility, you can see across the threat landscape in your network and gather intelligence.
- Now with insights one gathers it’s time to turn insights into action and understand the tactics employed by threat actors. These insights are keys to set up proactive defense.
- Bring Intrucept as a part of your Security team. We are here to assist you as you need a deeper understanding of evolving threats and ways to mitigate them. Our next gen SIEM is a comprehensive solution for Security Information. It gathers information and then interprets, centralizing all security data for organizations.
For visibility Intru360 gives security analysts and SOC managers a clear view across the organization, helping them fully understand the extent and context of an attack.
- Simply your workflows with Intru360, which automatically handles alerts, allow faster detection of both known and unknown threats.
- When it is question of cyber security and threats most organizations face, one need’s to have confidence in the threat intelligence one uses
- Once you are able to identify latest threats and you will not have to purchase, implement and oversee several solutions and even manage a team security analyst, it is easier. You get to save time and reduce complexity while researching for threats.
At the end we can say its not only responsibility for Government to respond or remain alert to cyber attacks and hackers foul play.
The present decade will witness more cyber war that is parallel along side when two nations go at war with each other deploying different AI-driven tools in their attacks. It is high time to stay alert and practice safe cyber security measures at individual level and enterprise level.
Sources: Reflections of the Israel-Iran Conflict on the Cyber World – SOCRadar® Cyber Intelligence Inc.










Recent Comments