Qualcomm Chipset Vulnerability Allows RCE
Security updates from Qualcomm are of high importance as they are connected to the ecosystem of hardware powering Snapdragon processors .
The multiple severe vulnerabilities were lying in its private or proprietary and open source software allowing an unauthenticated attacker to achieve remote code execution via the SocketIO interface.
The flaw allow attackers to execute arbitrary code remotely
CVE-2026-25254, is the most severe flaw with a critical CVSS score of 9.8.
Qualcomm has addressed several high-severity issues that could lead to local privilege escalation or system instability.
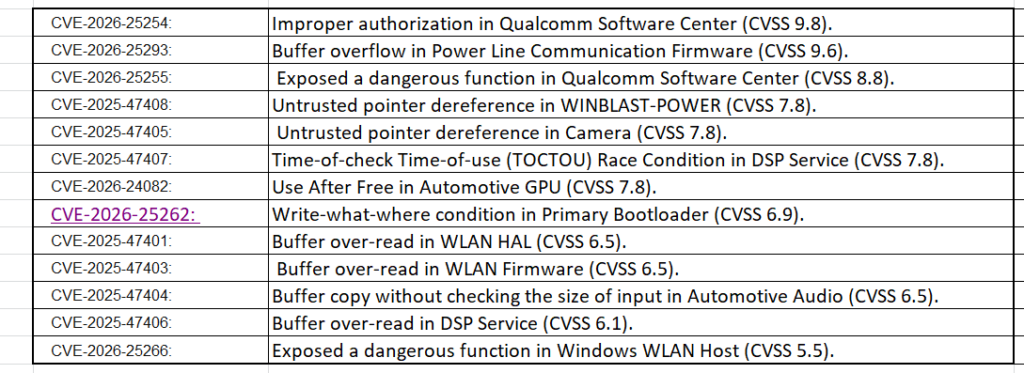
Key details of Multi-Component Qualcomm Vulnerabilities
- Along with CVE-2026-25254, the other vulnerabilities include CVE-2026-25293 with CVSS 9.6 score, affects PLC firmware or power line communication.
- CVE-2026-25262 vulnerability involves a write-what-where condition in the Primary Bootloader, leading to memory corruption when processing crafted ELF files.
- The other vulnerabilities found in the WLAN HAL and firmware (CVE-2025-47401 and CVE-2025-47403) allow remote attackers to trigger transient Denial-of-Service (DoS) conditions via buffer overruns during channel configuration or wireless roaming.
Qualcomm strongly advises manufacturers to prioritize patch deployment. Security teams and users should:
- Apply firmware and security updates as soon as they become available.
- Monitor vendor advisories for patch release timelines.
- Restrict network exposure of vulnerable systems where possible.
- Use mobile device management and endpoint protection tools to detect abnormal behavior.
Patching :
Android security updates have started integrating patches for various Qualcomm components, underscoring the urgency of these deployments.
Patches are being actively shared with OEMs, who have been notified and strongly recommended to deploy those patches on released devices as soon as possible. Please contact the device manufacturer for information on the patching status of released devices.
As per Qualcomm security Bulletin, end users should immediately apply the latest firmware and security updates from their device manufacturers.
Sources: https://docs.qualcomm.com/securitybulletin/may-2026-bulletin.html
Sources: https://cybersecuritynews.com/qualcomm-chipset-vulnerabilities/
