Vulnerabilities in IP-KVMs from 4 Vendors; Risk for Unauthenticated Root Access
Severe vulnerabilities found in IP KVM may allow unauthenticated hackers to gain root access or run malicious code on them. These vulnerabilities have CVSS scores ranging from 3.1 to 9.8.
There are great risks associated as a low-cost device have the ability to provide insiders and hackers unusually broad powers in networks that are often not so secured or vulnerable. Recently researchers from security firm Eclypsium disclosed a total of nine vulnerabilities in IP KVMs from four manufacturers.
IP-KVMs
When a device sell for $30 to $100, are known as IP KVMs. Administrators often use them to remotely access machines on networks. The devices, not much bigger than a deck of cards, allow the machines to be accessed at the BIOS/UEFI level, the firmware that runs before the loading of the operating system.
Risk Associated with IP KVM
If hackers get hands of they might misuse capabilities even in a secured network. Risks are posed when the devices are exposed to the web or internet—are deployed with weak security configurations or surreptitiously connected to by insiders. Firmware vulnerabilities also leave them open to remote takeover.
Its easy for attackers to manipulate device behavior by overwriting configuration files or system binaries, by an attacker can manipulate the device’s behavior. subsequently gain unauthorized access and use the KVM as a pivot point to compromise any target machine connected to it.
“These are not exotic zero-days requiring months of reverse engineering,” Eclypsium researchers Paul Asadoorian and Reynaldo Vasquez Garcia wrote. “These are fundamental security controls that any networked device should implement. Input validation. Authentication. Cryptographic verification. Rate limiting. We are looking at the same class of failures that plagued early IoT devices a decade ago, but now on a device class that provides the equivalent of physical access to everything it connects to.”
Analysis:
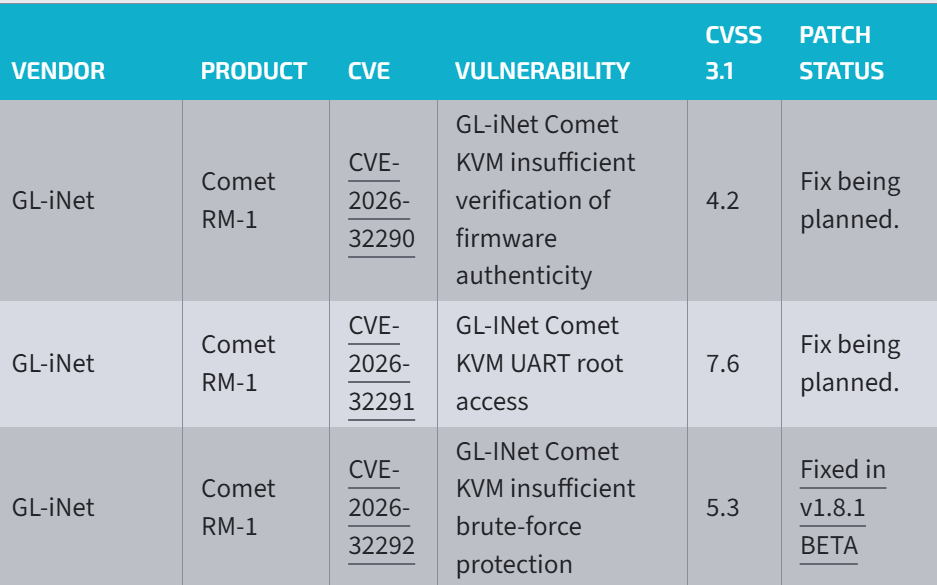
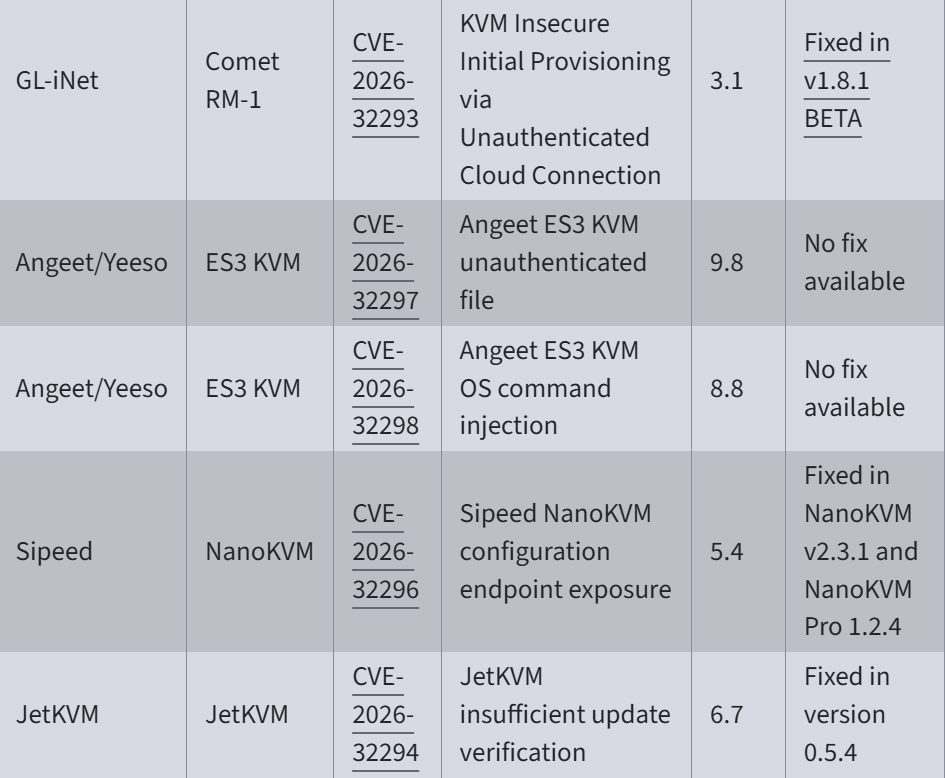
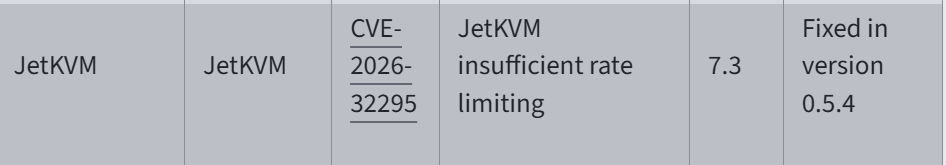
The vulnerabilities are catalogued as CVE-2026-32290, CVE-2026-32291, CVE-2026-32292, CVE-2026-32293, CVE-2026-32294, CVE-2026-32295, CVE-2026-32296, CVE-2026-32297 and CVE-2026-32298, with CVSS scores ranging from 3.1 to 9.8 and some fixes already in place (for example, JetKVM updates and NanoKVM versions) while others remain unpatched.
The analysis notes that an attacker could inject keystrokes, boot from removable media to bypass protections, circumvent lock screens, or remain undetected by OS-level security software, given the devices’ remote BIOS/UEFI access.
Threat Mitigation
Mitigations include enforcing MFA where supported, isolating KVM devices on a dedicated management VLAN, restricting internet access, monitoring traffic, and keeping firmware up-to-date, according to Eclypsium.
This vulnerability alone dictates the term immediate network isolation of any deployed Angeet ES3 device.
Requirement of Robust firmware validation and strong access controls
For robust Firmware validation, testing is must but here testing do not imply checking if the coding is working or not. Instead it is a systematic process of assessing whether firmware meets the defined specifications and quality standards.
We have BI and Data Analytics to redefined outcomes of testing and are measured, with key performance indicators (KPIs) drawn from vast amounts of operation data stored in testing logs and real-time deployment environments.









Recent Comments