SAP npm Packages Targeted with Malware ‘Supply Chain Risk’-Patch Now
Supply chain attack
Continue ReadingCVE-2026-33626 vulnerbility in LLMDeploy
Continue ReadingCodex Enabled GitHub Token Theft
Continue ReadingAttackers Targeted SSH keys, Cloud Tokens & API secrets in CI/CD Pipelines; Highlights Securing CI/CD Pipelines
Malicious code rode alongside legitimate scans, targeting SSH keys, cloud tokens and API secrets in CI/CD pipelines. Security researcher Paul McCarty was the first to warn publicly that Trivy version 0.69.4 had been backdoored, with malicious container images and GitHub releases published to users.
Attack module on Trivy
When it comes to workflow it has been observed that more then 10,000 GitHub workflow files rely on trivy-action. Attackers can leverage this pipeline and pull versions during the attack window which are affected and carry sensitive credentials exfiltrated.
Attackers compromised the GitHub Action by modifying its code and retroactively updating version tags to reference a malicious commit. This permitted data used in CI/CD workflows to be printed in GitHub Actions build logs and finally leaking credentials.
A self-propagating npm worm compromised 47 packages, extending the blast radius into the broader JavaScript ecosystem.
Aqua Security disclosed in a GitHub Discussion that the incident stemmed from incomplete containment of an earlier March 1 breach involving a hackerbot-claw bot.
TeamPCP preserved normal scan functionality to avoid triggering CI/CD failures as detection now will require cryptographic verification of commit signatures .
For defenders, traditional CI/CD monitoring, which watches for build failures or unexpected output, can no longer catch supply-chain compromises that deliberately maintain normal behavior.
Organizations relying on Trivy or similar open-source security tools are facing attacks from the very scanners meant to protect their pipelines can become the attack vector. Only cryptographic provenance checks can distinguish legitimate releases from poisoned ones.
As per security researchers once inside a pipeline, the malicious script scanned memory regions of the GitHub Actions Runner.
Github Compromise
The attack appears to have been accomplished via the compromise of the cx-plugins-releases (GitHub ID 225848595) service account, as that is the identity involved in publishing the malicious tags.
Credentials exfiltrated during the initial incident were used last week in a new supply chain attack that targeted not only the Trivy package but also trivy-action and setup-trivy, Trivy’s maintainers have confirmed in a March 21 advisory.
Key Findings b Wiz Research
“The payload attempts execution via npx, bunx, pnpx, or yarn dlx. This covers major JavaScript package managers,” Wiz researchers Rami McCarthy, James Haughom, and Benjamin Read said. “The retrieved package contains a comprehensive credential stealer.
Harvested credentials are then encrypted, using the keys as elsewhere in this campaign, and exfiltrated to ‘checkmarx[.]zone/vsx’ as tpcp.tar.gz.”
Conclusion: Aqua Security urged affected users to “treat all pipeline secrets as compromised and rotate immediately.”
Organizations that ran any version of trivy-action, setup-trivy, or Trivy v0.69.4 during the attack window should audit their CI/CD logs for unexpected network connections to scan.aquasecurtiy[.]org and check whether any tpcp-docs repositories were created under their GitHub accounts.
With three major tag-hijacking incidents in 12 months, Wiz security researcher Rami McCarthy recommended that organizations “pin GitHub Actions to full SHA hashes, not version tags.”
Summary : YARA is an open-source pattern matching engine widely used by malware researchers, SOC teams, and threat intelligence platforms to identify and classify malware using detection rules. It plays a critical role in malware analysis pipelines, endpoint detection systems, and threat hunting operations.
Kamil Frankowicz discovered that a number of YARA’s functions generated memory exceptions when processing specially crafted rules or files. A remote attacker could possibly use these issues to cause YARA to crash, resulting in a denial of service.
| OEM | Virus Total / YARA Project (Tool) |
| Severity | Critical |
| CVSS Score | 9.1 |
| CVEs | CVE-2021-3402, CVE-2021-45429, CVE-2019-19648, CVE-2018-19974, 2018-19975, 2018-19976 |
| POC Available | No |
| Actively Exploited | No |
| Exploited in Wild | No |
| Advisory Version | 1.0 |
Overview
Ubuntu has released a security advisory addressing multiple vulnerabilities in YARA that could allow attackers to cause denial-of-service conditions, disclose sensitive information, or potentially execute arbitrary code when processing specially crafted files or rules.
These vulnerabilities affect Ubuntu 16.04 LTS, 18.04 LTS, and 20.04 LTS depending on the specific issue. Organizations using YARA in security monitoring systems, malware sandboxes, or automated threat detection workflows should apply the security updates immediately.
| Vulnerability Name | CVE ID | Product Affected | Severity | CVSS Score | Fixed Version |
| Mach-O Parser Overflow Read Vulnerability | CVE-2021-3402 | YARA | Critical | 9.1 | Updated Ubuntu packages |
| Mach-O File Parsing Out-of-Bounds Access | CVE-2019-19648 | YARA | High | 7.8 | Updated Ubuntu packages |
Technical Summary
The most critical vulnerability CVE-2021-3402 exists in the macho.c implementation used by YARA to parse Mach-O files.
The flaw allows specially crafted Mach-O files to trigger overflow reads, which could result in denial of service or potential information disclosure. Given its high CVSS score, this issue represents the most severe risk addressed in this advisory.
Another high-severity vulnerability CVE-2019-19648 affects the macho_parse_file() function. When parsing specially crafted Mach-O files, the function may trigger out-of-bounds memory access, potentially leading to application crashes or execution of malicious code in certain scenarios.
Because YARA is frequently integrated into malware analysis platforms and automated threat detection pipelines, successful exploitation could disrupt security monitoring operations or compromise malware analysis environments.
| CVE ID | System Affected | Vulnerability Details | Impact |
| CVE-2021-3402 | YARA (Ubuntu 20.04) | Overflow read vulnerability in Mach-O parsing implementation | DoS, potential information disclosure |
| CVE-2019-19648 | YARA (Ubuntu 20.04) | Out-of-bound memory access during Mach-O file parsing | DoS or possible code execution |
Additional Vulnerabilities
The advisory also includes several medium-severity vulnerabilities affecting YARA components.
| CVE ID | Vulnerability Details | Impact |
| CVE-2021-45429 | Buffer overflow in yr_set_configuration() when parsing crafted rules | Denial of Service |
| CVE-2018-19976 | YARA virtual machine sandbox escape | Possible code execution |
| CVE-2018-19975 | VM sandbox escape vulnerability | Possible code execution |
| CVE-2018-19974 | Virtual machine security bypass | Possible code execution |
Potential Consequences
Remediation
Upgrade affected packages immediately to the patched versions provided by Ubuntu are mentioning below-
Released patches
| Ubuntu Release | Package | Fixed Version |
| Ubuntu 20.04 LTS | libyara3 | 3.9.0-1ubuntu0.1 esm1 |
| yara | 3.9.0-1ubuntu0.1 esm1 | |
| Ubuntu 18.04 LTS | libyara3 | 3.7.1-1ubuntu2+esm1 |
| yara | 3.7.1-1ubuntu2+esm1 | |
| Ubuntu 16.04 LTS | libyara3 | 3.4.0+dfsg-2ubuntu0.1 esm1 |
| python-yara | 3.4.0+dfsg-2ubuntu0.1 esm1 | |
| python3-yara | 3.4.0+dfsg-2ubuntu0.1 esm1 | |
| yara | 3.4.0+dfsg-2ubuntu0.1 esm1 |
If immediate patching is not possible, apply the following temporary mitigations –
You can follow the recommendations below as the best practice.
Conclusion:
Multiple vulnerabilities in YARA could allow attackers to disrupt malware detection processes or compromise analysis environments. The critical vulnerability CVE-2021-3402 and high-severity vulnerability CVE-2019-19648 pose the greatest risk and should be prioritized for remediation.
Organizations using YARA in SOC operations, malware analysis pipelines, or threat intelligence systems should apply the latest Ubuntu security updates immediately to maintain reliable threat detection capabilities.
References:
Shai-Hulud malware campaign, npm Packages
Continue ReadingRed Hat, has been allegedly been hit by a breach and this has been posted by Crimson Collective hackers group on Telegram. The cyber criminals claim they’ve snatched private GitHub repositories, which include sensitive data about approximately 800 customers’ networks.
Key points from the RedHat Breach
“Source code and consulting engagement reports (CERs), if leaked, can help attackers analyze internal company infrastructure and software running on that infrastructure. This makes it significantly easier and faster to identify vulnerable attack vectors for potential attackers, “ said Aras Nazarovas, information security researcher at Cybernews.
RedHat confirmed the attack
According to the attackers, they found authentication keys, full database URIs, and other private information in the Red Hat code and CERs, which they allegedly used to gain access to downstream customer infrastructure.
On Telegram, the hacker group published a complete directory listing of stolen GitHub repositories, along with a list of customer reports from the period 2020-2025.
Red Hat has confirmed the security incident relating to its GitLab instance, but declined to comment on the attackers’ specific claims regarding the GitHub repositories and customer reports. The company emphasizes that there is no reason to believe that the security issue affects other Red Hat services or products. Red Hat says it is very confident in the integrity of its software supply chain.
The CER list includes organizations from various sectors, including major international names such as Bank of America, T-Mobile, AT&T, Fidelity, and Walmart.
Extortion Demands by Hackers
The data breach on RedHat was also an attempt to contact Red Hat and get through with extortion demands. The cybercriminals received a response asking them to submit a vulnerability report to the security team.
The ticket created by cyber criminals was reportedly forwarded repeatedly to various individuals, including employees of Red Hat’s legal and security departments.
Microsoft finds that a fake ChatGPT Desktop App Delivering PipeMagic Backdoor,a part of sophisticated malware framework. The PipeMagic campaign represents a dangerous evolution in the global cybercrime landscape. The malicious campaign, powered by a new backdoor called PipeMagic, targets multiple industries including IT, finance, and real estate. The PipeMagic attack is centered around CVE-2025-29824, a critical Windows Common Log File System (CLFS) vulnerability
The PipeMagic campaign a malware to technical threat exploiting trust globally
As per Microsoft cybercriminals are disguising malware as widely popular ChatGPT Desktop Application to launch ransomware attacks across the globe.
PipeMagic’s evolution from malware to technical threat exploiting trust globally
The malware allows hackers to escalate privileges once inside a system, by leveraging the immense popularity of ChatGPT, attackers have successfully weaponized user trust.
Microsoft has linked the operation to Storm-2460, a financially motivated cybercrime group known for deploying ransomware through stealthy backdoors.
PipeMagic is a malware first detected in December 2022 while investigating a malicious campaign involving RansomExx. The victims were industrial companies in Southeast Asia. To penetrate the infrastructure, the attackers exploited the CVE-2017-0144 vulnerability.
The backdoor’s loader was a trojanized version of Rufus, a utility for formatting USB drives. PipeMagic supported two modes of operation – as a full-fledged backdoor providing remote access, and as a network gateway – and enabled the execution of a wide range of commands.
Pipemagic’s technique of attack
PipeMagic also reflects a growing trend where attackers combine fileless malware techniques with modular frameworks.
By running directly in memory, it avoids detection from traditional signature-based tools. The modular design means it can expand its functionality much like commercial software — essentially transforming cybercrime into a scalable business model.
Another key point is the use of cloud infrastructure for command-and-control. By hosting their servers on Azure, the hackers blend into normal enterprise traffic, making malicious communications far less suspicious. This tactic underscores the need for behavioral monitoring instead of relying solely on blacklists.
Microsoft attributes PipeMagic to a financially motivated group known as Storm-2460. This is a warning sign for future attacks in the broader cybersecurity landscape.
PipeMagic’s modus operandi could be an inspiration for future malware families and its modular framework could fuel a wave of ransomware-as-a-service operations. That possibility raises the stakes not just for enterprises but also for small businesses and even government institutions.
The first stage of the PipeMagic infection execution begins with a malicious in-memory dropper disguised as the open-source for chat GPT application project. The threat actor uses a modified version of the GitHub project that includes malicious code to decrypt and launch an embedded payload in memory.
The embedded payload is the PipeMagic malware, a modular backdoor that communicates with its C2 server over TCP. Once active, PipeMagic receives payload modules through a named pipe and its C2 server.
The malware self-updates by storing these modules in memory using a series of doubly linked lists.
These lists serve distinct purposes for staging, execution, and communication, enabling the threat actor to interact and manage capabilities of backdoor throughout its lifecycle.
By offloading network communication and backdoor tasks to discrete modules, PipeMagic maintains a modular, stealthy, and highly extensible architecture, making detection and analysis significantly challenging.
Microsoft Threat Intelligence encountered PipeMagic as part of research on an attack chain involving the exploitation of CVE-2025-29824, an elevation of privilege vulnerability in Windows Common Log File System (CLFS).
Security advisory: Patch Now! Critical Command Injection in GitHub Action tj-actions/branch-names Affects 5,000+ public repositories.
Summary:
A critical vulnerability has been identified in the tj-actions/branch-names’ GitHub Action workflow which allows arbitrary command execution in downstream workflows. This issue arises due to inconsistent input sanitization and unescaped output, enabling malicious actors to exploit specially crafted branch names or tags.
| Severity | Critical |
| CVSS Score | 9.1 |
| CVEs | CVE-2025-54416 |
| POC Available | Yes |
| Actively Exploited | No |
| Exploited in Wild | No |
| Advisory Version | 1.0 |
Overview
This issue arises due to inconsistent input sanitization and unescaped output, enabling malicious actors to exploit specially crafted branch names or tags. While internal sanitization mechanisms have been implemented, the action outputs remain vulnerable, exposing consuming workflows to significant security risks. This is fixed in version 9.0.0
The flaw allows attackers to run any command during GitHub Actions workflows by creating specially crafted branch names or tags.
| Vulnerability Name | CVE ID | Product Affected | Severity | Fixed Version |
| Command Injection in branch-names GitHub Action | CVE-2025-54416 | tj-actions/branch-names GitHub Action <v8.2.1 | 9.1 | v9.0.0 or later |
Technical Summary
This Vulnerability puts many CI/CD pipelines at serious risk, including the possibility of stealing secrets or injecting malicious code into releases.
The vulnerability exists due to unsafe usage of the eval command in the action’s script. Although some escaping was done using printf “%q”, developers later used eval printf “%s” to unescaped values, which reintroduced command injection risks.
Any branch name containing malicious shell code can trigger execution during workflows.
The vulnerability affects GitHub Action workflows that use tj-actions/branch-names. It allows attackers to inject and execute arbitrary shell commands by creating a branch with malicious content. The issue is caused by the unsafe use of eval when handling branch names and tags in output generation.
| CVE ID | System Affected | Vulnerability Details | Impact |
| CVE-2025-54416 | GitHub repositories using tj-actions/branch-names < v8.2.1 | Unsafe use of eval leads to command injection | Attacker can run arbitrary commands, steal secrets, alter source code, or compromise workflows |
Proof of Concept (POC)

Remediation:
Conclusion:
This command injection flaw is extremely dangerous due to its simplicity and the number of projects it affects. GitHub Actions workflows that use branch names or tags from pull requests are especially at risk. Attackers don’t need access to the code just the ability to open a pull request.
All developers and security teams should act now by updating to the latest version and reviewing usage of GitHub Actions in their workflows.
References:
Data Breach with 30 exposed Datasets & contained approx 10 to 3.5 billion records making it one of the largest data breach.
According to a report security researchers from Cybernews found about a Data breach that leaked important data or passwords that was mostly generated by various cybercriminals using info stealing malware. They exposed data was made to look like a breach but these login credentials were gathered from social media, corporate platforms, VPNs etc via infostealer.
Now cybercriminals have unprecedented access to personal credentials and these credentials be used for account takeover, identity theft and targeted phishing activities.
The concern is the structure and recency of these datasets as they are not old breaches being recycled. This is fresh, weaponizable intelligence at scale”, added researchers.
The data sets contains a mix of details from stealer malware, credential stuffing sets and repackaged leaks. There is no way to compare these datasets, but likely to contain at least some duplicated information. This makes it hard to determine how many people were affected by the data breach.
What are Data sets & how deadly can be Infostealer as a malware?
Datasets are basically structure collection of data collected over the years or so and organized as case specific models
In 2024 datasets containing billions of passwords have previously found their way on the internet. Last year, researchers came across what they called the Mother of All Breaches, which contained more than 26 billion records.
The data breach that happened had data in sets, following a particular pattern, containing an URL followed by a username and password. To those unaware, this is exactly how infostealing malware collects information and sends it to threat actors.
The exposed data came from platforms widely used round the world starting from Google, Apple, Github, Telegram & Facebook. So data was first collected over a period of time, further made into data sets and grouped together.
Info stealers are malware programs that are designed to silently steal usernames and passwords Basically designed to swipe of credentials from people’s devices and send them to threat actors for further them for sale on dark web forums.
An infostealer is malware that attempts to steal credentials, cryptocurrency wallets, and other data from an infected device. Over the years, infostealers have become a massive problem, leading to breaches worldwide. No device is spare from infostealer’s impact including Windows and Macs, and when executed, will gather all the credentials it can find stored on a device and save them in what is called a “log.”
If a organization or individual is infected with an infostealer and have hundreds of credentials saved in their browser, the infostealer will steal them all and store them in the log. These logs are then uploaded to the threat actor, where the credentials can be used for further attacks or sold on cybercrime marketplaces.
An infostealer log is generally an archive containing numerous text files and other stolen data.
Fig1:
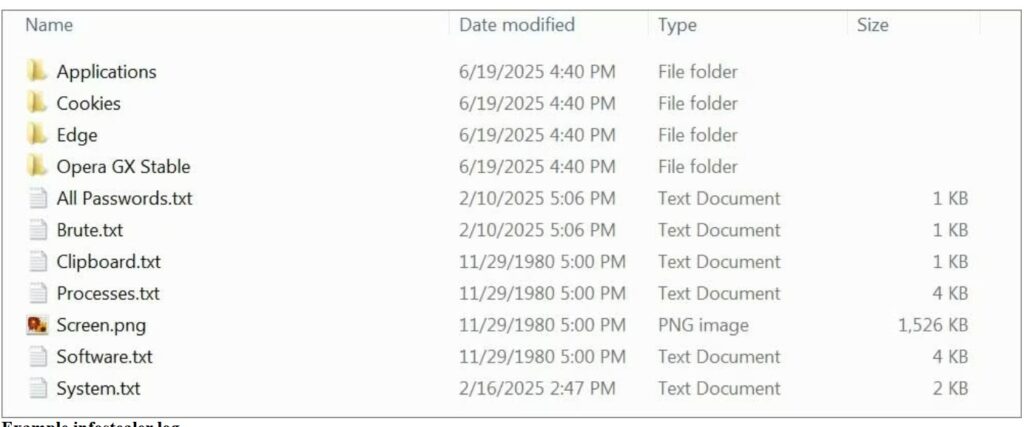
(Image courtesy: Bleeping computers)
A devastating data breach is a nightmare for customers and affected organizations, but breaches can have a positive side also. Each incident is a learning opportunity. It’s easier to defend critical data when we understand the mistakes made by others and the tactics used by attackers.
How to be secure & keep your Data safe
If users are in midst of data breach or may find that their data is not safe as an infostealer might be there in your systems or devices then scan your device with an antivirus program. Once done then change password or your newly entered credentials could be stolen again. The system is clean so password hygiene can be maintained time to time.
At times even unique passwords won’t help you stay protected if you are hacked, fall for a phishing attack, or install malware. Its better not to change all credentials in one go instead having a cyber security hygiene in routine is better as an option.
Intru360
For organizations to stop and detect any intrusion by attackers prefer to have Intru360 in your list of cyber security go to products from Intruceptlabs.
Intru360 gives security analysts and SOC managers a clear view across the organization, helping them fully understand the extent and context of an attack. It also simplifies workflows by automatically handling alerts, allowing for faster detection of both known and unknown threats.
Globally every year cyberattacks are growing and mutating each month. Organizations have their Intelligent intrusion network detection systems in place analyze and detect anomalous traffic to face these threats.
Do visit our website for more information.
Recent Comments