Attackers May Exploit SQL Injection Vulnerability in Drupal’s Database
Key Highlights from Drupal Core SQL Injection Vulnerability: CVE-2026-9082
Severity: Highly Critical
CVSSv3: 6.5 : Medium
- CVE-2026-9082 is a highly critical SQL injection vulnerability in Drupal core’s database abstraction API
- Can be exploited by unauthenticated attackers on sites using PostgreSQL.
- No exploitation has been observed in the wild, but a detection PoC was published on the same day as the advisory and the patch diff was shared publicly within hours.
- Patches are available across six supported Drupal branches, including two exceptional releases for end-of-life versions.
Critical SQL injection Vulnerability in Drupal core Affects sites running PostgreSQL
As per Tenable, this vulnerability only affects Drupal sites using PostgreSQL as their database backend. Sites running MySQL, MariaDB, or SQLite are not affected. The vulnerable code resides in Drupal’s PostgreSQL EntityQuery condition handler, which is only invoked on PostgreSQL configurations. No in-exploitation in the wild reported.
Threat Mitigation: Drupal Core SQL Injection Vulnerability
This means older versions of Drupal — specifically Drupal 8.9 and 9.5 — are no longer officially supported and will not receive normal security update packages anymore because they have reached end-of-life (EOL).
- Drupal has still released special emergency “hotfix” files for:
- Drupal 9.5.11
- Drupal 8.9.20
These hotfixes help protect vulnerable websites from the reported security issue. The update also includes security fixes from third-party components used inside Drupal, including:
- Symfony
- Twig
Even if organizations are not using PostgreSQL databases, Drupal still recommends updating because other security vulnerabilities are also fixed in these releases.
Affected Environments by CVE-2026-9082
The vulnerability only affects certain versions of Drupal when the website uses a PostgreSQL database.
In simple terms:
- Vulnerable versions:
- Drupal 8.9.0 to 11.3.9
- Affected only if:
- The site uses PostgreSQL as its database backend
The issue exists in the PostgreSQL-specific code used by Drupal to process database queries.
Websites using: MySQL, MariaDB and SQLite are not affected by this particular vulnerability because they use different database handling code.
Additionally: Drupal 7 is completely unaffected by this issue.
A list of Tenable plugins for this vulnerability can be found on the individual CVE page for CVE-2026-9082 as they’re released. This link will display all available plugins for this vulnerability, including upcoming plugins in our Plugins Pipeline.
Drupal estimates that under 5% of installations run on PostgreSQL. Across the hundreds of thousands of public Drupal sites, that still leaves thousands of internet-reachable targets, concentrated in the segments where Drupal adoption is strongest.
Drupal Patches:
Drupal released fixes across all six supported branches on May 20: 10.4.10, 10.5.10, 10.6.9, 11.1.10, 11.2.12, and 11.3.10. The security team also published exceptional patches for the end-of-life 8.9 and 9.5 branches, given the severity and the volume of legacy installations.
The advisory recommends upgrading to the patched release matching the current branch (11.3.x to 11.3.10, 11.2.x to 11.2.12, 11.1.x or 11.0.x to 11.1.10, 10.6.x to 10.6.9, 10.5.x to 10.5.10, 10.4.x or earlier to 10.4.10). Drupal 8 and 9 sites should treat the exceptional patches as a stopgap rather than a long-term position, because other unpatched issues remain in those branches.
Defenders should verify patch status directly with their hosting provider rather than assume any specific platform-level fix is in place.
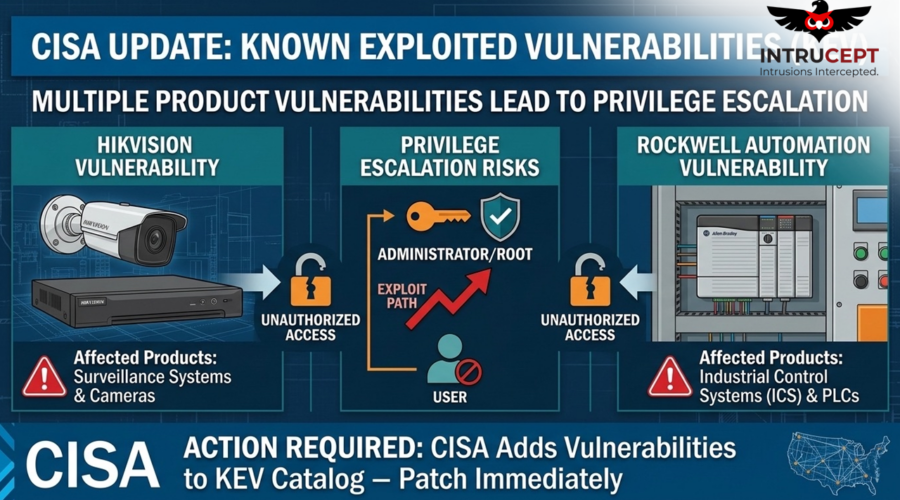
CISA Adds CVE-2026-9082 in its KEV Catalogue
The vulnerability was officially added to CISA’s Known Exploited Vulnerabilities (KEV) catalog on May 22, 2026, indicating confirmed exploitation activity.
Federal agencies and organizations are required to remediate the issue by May 27, 2026, under Binding Operational Directive (BOD) 22-01.
Conclusion: Because of improper input validation, attackers can insert harmful SQL commands into input fields such a application. If unchecked or not sanitized on time, user input before sending it to the database, attackers may manipulate backend database operations potentially bypassing authentication controls. This may lead to accessing sensitive database information and modify or delete data.
If patching is not applicable or not matching with application, organizations should consider temporarily turning off affected services until mitigation measures are in place. The active exploitation of CVE-2026-9082 underscores the ongoing risk posed by SQL injection vulnerabilities in widely used platforms such as Drupal.