SAP npm Packages Targeted with Malware ‘Supply Chain Risk’-Patch Now
Supply chain attack
Continue ReadingAttackers Targeted SSH keys, Cloud Tokens & API secrets in CI/CD Pipelines; Highlights Securing CI/CD Pipelines
Malicious code rode alongside legitimate scans, targeting SSH keys, cloud tokens and API secrets in CI/CD pipelines. Security researcher Paul McCarty was the first to warn publicly that Trivy version 0.69.4 had been backdoored, with malicious container images and GitHub releases published to users.
Attack module on Trivy
When it comes to workflow it has been observed that more then 10,000 GitHub workflow files rely on trivy-action. Attackers can leverage this pipeline and pull versions during the attack window which are affected and carry sensitive credentials exfiltrated.
Attackers compromised the GitHub Action by modifying its code and retroactively updating version tags to reference a malicious commit. This permitted data used in CI/CD workflows to be printed in GitHub Actions build logs and finally leaking credentials.
A self-propagating npm worm compromised 47 packages, extending the blast radius into the broader JavaScript ecosystem.
Aqua Security disclosed in a GitHub Discussion that the incident stemmed from incomplete containment of an earlier March 1 breach involving a hackerbot-claw bot.
TeamPCP preserved normal scan functionality to avoid triggering CI/CD failures as detection now will require cryptographic verification of commit signatures .
For defenders, traditional CI/CD monitoring, which watches for build failures or unexpected output, can no longer catch supply-chain compromises that deliberately maintain normal behavior.
Organizations relying on Trivy or similar open-source security tools are facing attacks from the very scanners meant to protect their pipelines can become the attack vector. Only cryptographic provenance checks can distinguish legitimate releases from poisoned ones.
As per security researchers once inside a pipeline, the malicious script scanned memory regions of the GitHub Actions Runner.
Github Compromise
The attack appears to have been accomplished via the compromise of the cx-plugins-releases (GitHub ID 225848595) service account, as that is the identity involved in publishing the malicious tags.
Credentials exfiltrated during the initial incident were used last week in a new supply chain attack that targeted not only the Trivy package but also trivy-action and setup-trivy, Trivy’s maintainers have confirmed in a March 21 advisory.
Key Findings b Wiz Research
“The payload attempts execution via npx, bunx, pnpx, or yarn dlx. This covers major JavaScript package managers,” Wiz researchers Rami McCarthy, James Haughom, and Benjamin Read said. “The retrieved package contains a comprehensive credential stealer.
Harvested credentials are then encrypted, using the keys as elsewhere in this campaign, and exfiltrated to ‘checkmarx[.]zone/vsx’ as tpcp.tar.gz.”
Conclusion: Aqua Security urged affected users to “treat all pipeline secrets as compromised and rotate immediately.”
Organizations that ran any version of trivy-action, setup-trivy, or Trivy v0.69.4 during the attack window should audit their CI/CD logs for unexpected network connections to scan.aquasecurtiy[.]org and check whether any tpcp-docs repositories were created under their GitHub accounts.
With three major tag-hijacking incidents in 12 months, Wiz security researcher Rami McCarthy recommended that organizations “pin GitHub Actions to full SHA hashes, not version tags.”
MUT-8694: Threat Actors Exploiting Developer Trust in Open-Source Libraries
Overview
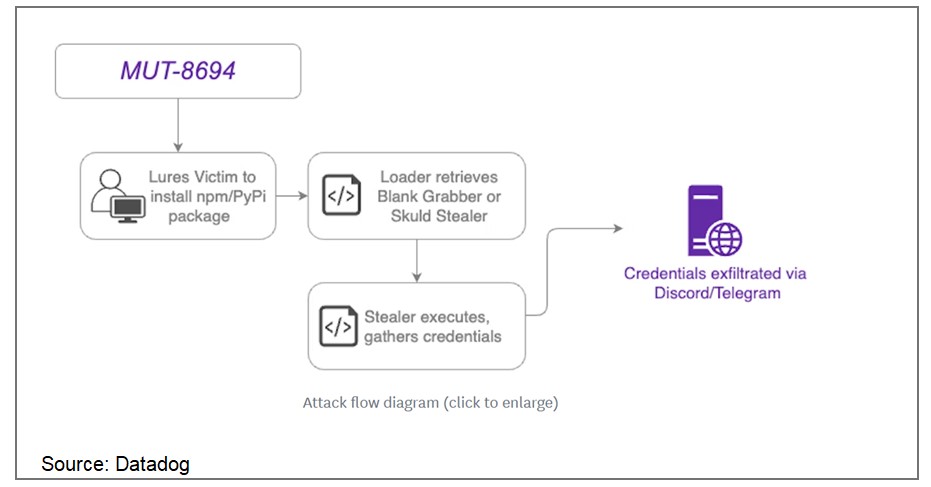
In November 2024, a supply chain attack designated as MUT-8694 was identified, targeting developers relying on npm and PyPI package repositories. This campaign exploits trust in open-source ecosystems, utilizing typosquatting to distribute malicious packages. The malware predominantly affects Windows users, delivering advanced infostealer payloads.
MUT-8694 Campaign Details
The threat actors behind MUT-8694 use malicious packages that mimic legitimate libraries to infiltrate developer environments. The campaign employs techniques such as:
Source: Datadog
Key Findings
One identified package, larpexodus (version 0.1), executed a PowerShell command to download and run a Windows PE32 binary from github[.]com/holdthaw/main/CBLines.exe. Analysis revealed the binary was an infostealer malware, Blank Grabber, compiled from an open-source project hosted on GitHub. Further inspection of the repository exposed another stealer, Skuld Stealer, indicating the involvement of multiple commodity malware samples.
Capabilities of Malware
The deployed malware variants include advanced features that allow:
Affected Packages
Some known malicious packages include:
Remediation:
To mitigate the risks associated with this attack, users should:
General Recommendations:
References:
Recent Comments