New PureLogs Malware Variant Hijacks MSBuild.exe to Hide Malicious Processes
FortiGuard Labs recently identified a phishing campaign distributing a PureLogs variant designed to collect sensitive data from the victim’s device. The analysis provides an in-depth examination of the campaign, including the phishing emails and the mechanisms by which the JavaScript file operates on the victim’s device
This campaign uses deceptive emails disguised as purchase orders, a tactic commonly used to trick recipients into opening malicious attachments.
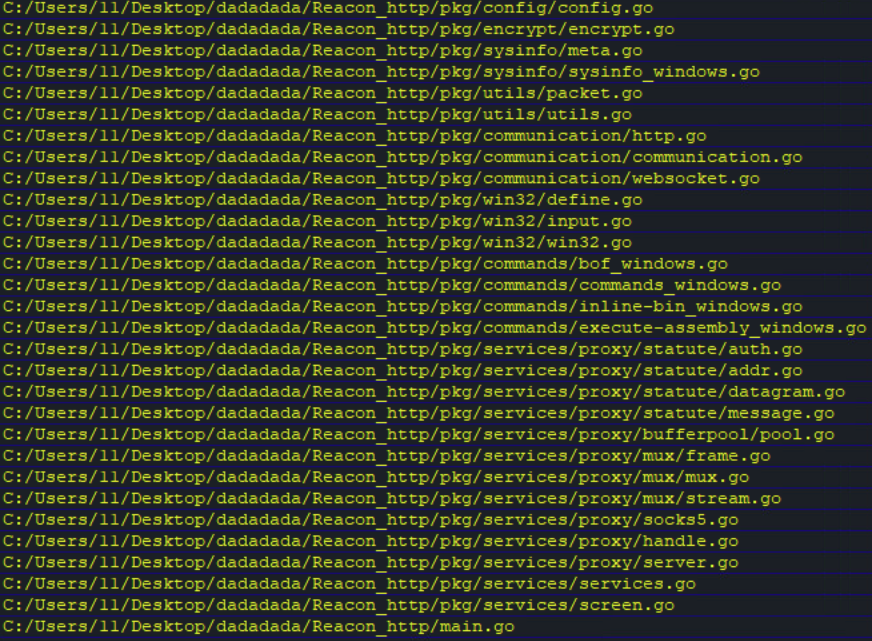
Infection Chain
Figure 1 illustrates the infection chain of this phishing email campaign.

(Fortinet)
Step-by-Step Attack Flow of the PureLogs Campaign
This campaign employs a sophisticated multi-stage attack chain that begins with a phishing email delivering a malicious JavaScript file.
The JavaScript decrypts and launches a PowerShell script, which then uses process hollowing to inject a .NET downloader into the legitimate Windows process MsBuild.exe. The downloader communicates with a remote C2 server to fetch and execute additional plugin modules, enabling flexible post-compromise operations.
The attack leverages multiple encryption layers, fileless execution, and process hollowing techniques, making it highly evasive and difficult for traditional signature-based security solutions to detect.
Organizations are advised to strengthen email filtering, restrict unnecessary script execution, and monitor for suspicious PowerShell activity and process hollowing behavior.
The use of multiple encryption layers, fileless execution, and process hollowing techniques makes this campaign highly evasive and difficult for traditional signature-based security solutions to detect. Organizations are advised to enforce email filtering, disable unnecessary script execution, and monitor for anomalous PowerShell activity and process hollowing.
PureLogs Attack scenario
The attack begins with a fake purchase order email. Fortinet observed an attached archive named PO 2026-P0803.rar, which carried a malicious JavaScript file called kpankocrs.js.
When the victim opens the script, it decrypts PowerShell code and writes it to a randomly named .ps1 file in the C:\Temp folder. The script then runs PowerShell with flags that bypass execution policy, hide the window, and avoid loading a user profile.
From there, the PowerShell stage decodes and decrypts more content. It loads .NET modules directly in memory, which helps the campaign reduce obvious files on disk and avoid simpler signature-based detection.
MsBuild.exe Is Useful to Attackers
MsBuild.exe is a legitimate Microsoft build utility commonly used to compile and build applications. Because it is a trusted Windows component frequently seen in enterprise environments, attackers often abuse it to disguise malicious activity under the appearance of normal system operations.
In this campaign, the threat actors leveraged the hardcoded path C:\Windows\Microsoft.NET\Framework\v4.0.30319\MsBuild.exe as the target for process hollowing. According to Fortinet’s analysis, the PowerShell stage creates a suspended MsBuild.exe process and injects malicious .NET code into it before execution resumes.
The abuse of legitimate Windows binaries like MsBuild.exe allows attackers to blend into normal system activity, making detection significantly harder if organizations are not actively monitoring process behavior, parent-child relationships, and suspicious network communications.
Process Hollowing Helps PureLogs Evade Detection
Process hollowing is a stealth-focused process injection technique that allows malware to operate from within a legitimate process. The attacker launches a trusted application in a suspended state, replaces its memory with malicious code, and then resumes execution.
MITRE ATT&CK identifies process hollowing as a common defense evasion technique used to bypass traditional security controls. Fortinet observed several APIs associated with this activity, including CreateProcessA, ZwUnmapViewOfSection, WriteProcessMemory, SetThreadContext, and ResumeThread.
As a result, security tools may only detect a seemingly legitimate MsBuild.exe process, while the malicious payload executes silently within it. This deceptive behavior complicates both automated detection and manual incident analysis.
Information PureLogs Steals
PureLogs is a .NET-based information stealer designed to harvest sensitive system and user data from infected devices. Once deployed through the downloader module, the malware collects, compresses, encrypts, and exfiltrates data to its command-and-control (C2) infrastructure.
The malware gathers extensive host information, including screenshots, antivirus details, operating system data, processor information, usernames, screen resolution, memory size, clipboard contents, and system timestamps.