Cyber Campaign by Hacker’s on Microsoft teams invites to execute “device code phishing” attacks
Microsoft Teams have been on top of prime targets by threat actors and this time a Cyber campaign by Storm-2372 a hacking group targeted Microsoft Teams, a platform where collaboration and meeting is most sought after while inviting for meeting and executing “device code phishing” attacks.
The cyber campaign targets governments, NGOs, IT services, defense, telecommunications, health, education, and energy sectors across Europe, North America, Africa, and the Middle East. Microsoft Threat Intelligence team has rounded up and hardened the Teams environment, with countermeasures and controls across identity, endpoints, and network layers.
“It should come as no surprise that if they can build a persona for social engineering, they will take advantage of the same resources as legitimate organizations, including custom domains and branding, especially if it can lend credibility to impersonating internal help desk, admin, or IT support,” Microsoft explains.
Prime Target of Hackers
The attack pattern reveal type of social engineering campaign, which often combines a traditional email spam campaign with Microsoft Teams-based manipulation.
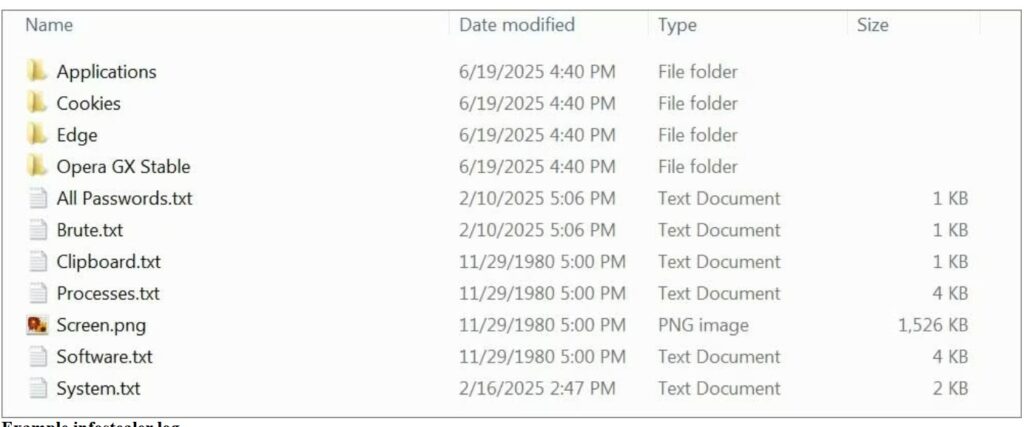
The primary target of hackers is to use convincing pretexts to compromise targets through chat messaging or phone calls. But for actual compromise and initial access on Teams, hackers will need to deliver information-stealing malware, which leads to credential theft, extortion, and ransomware.
As Microsoft Team is popular it is also a carrier of Malware which are mostly information stealing. Microsoft noted the rise in email bombing (sending large volumes of emails) to create a sense of urgency.
Not one but many hacking groups have previously targeted Microsoft teams of which Russian hackers from Midnight Blizzard have been imitating security and tech support teams. The hackers urging targets to “verify their identities under the pretext of protecting their accounts by entering authentication codes.”
Microsoft noted the rise in email bombing (sending large volumes of emails) to create a sense of urgency. These emails prompt recipients to authenticate using the provided device code on Microsoft’s legitimate login page.
The threat actor targets the victim, allows him to complete authentication then intercepts the access and refresh tokens generated during the process.

(Image courtesy: Cybersecuritynews.com)
Threat Mitigation strategies:
- Any suspicious activity if detected, revoke user refresh tokens using revokeSignInSessions.
- Important to Enforce MFA and block risky sign-ins based on user behavior.
- FIDO tokens or passkeys instead of SMS-based MFA must be adopted
- Integrate streamlined monitoring and response with on-premises directories .
The attackers’ intent was to convince users to download the remote monitoring and management (RMM) tool, AnyDesk, which would give them initial access to the target environment with the ultimate aim of deploying ransomware.