New Malware Framework Highlight Attackers Tactics; Gain Browser Access
New malware TencShell, a previously undocumented, Go-based implant derived from the open-source Rshell C2 framework targets manufacturing based enterprises. The malware’s activity appeared in traffic associated with a third-party user connected to the customer environment. The malware framework is based on screen control, browser artifact access and User Account Control (UAC) bypass that highlights how attackers are increasingly adapting open-source tools for real-world intrusions. Their attack pattern reveal careful design that can blend into normal enterprise traffic.
The tactics was revealed in April 2026, when Cato CTRL identified and blocked an attempted intrusion against a global manufacturing customer involving TencShell.
The malware has been previously undocumented, Go-based implant derived from the open-source Rshell C2 framework.
The activity appeared in traffic associated with a third-party user connected to the customer environment.
Malware attack chain
The attack chain used a first-stage dropper, Donut shellcode, a masqueraded .woff web-font resource, memory injection, and web-like C2 communication.
Activity noticed an suspected China-linked based on the apparent Rshell lineage, Tencent-themed API impersonation, and infrastructure patterns, While this pattern is relevant to our suspected China-linked assessment, it is not sufficient on its own for attribution.
If successful, TencShell could have given the attacker remote command execution, in-memory payload execution, proxying, pivoting, system profiling, and a path to deploy additional tooling. We blocked the attempt before the attacker could establish durable remote control.
Command & control framework
A C2 framework deployed through third-party access can turn a trusted business connection into an attacker-controlled bridge.
According to Cato CTRL, TencShell is a customized, Go-based implant derived from the open-source Rshell in C2 framework.
Security analysts suspect the malware has ties to Chinese threat actors, largely due to its infrastructure patterns and its clever impersonation of Tencent API services, which are designed to camouflage malicious communication.
If TencShell had installed successfully, the attacker could potentially execute commands, inspect files, steal credentials or session material, stage additional tools, proxy traffic through the endpoint, and move toward internal systems that are not directly exposed to the internet.
Business Risk for manufacturers posed by the Malware
From the standpoint of manufacturers across the globe, the business risk extends beyond. If any endpoint connected is compromised to a regional site can further expose supplier relationships, production workflows, intellectual property, customer data, logistics processes and business continuity.
The C2 framework gives the attacker the control needed to decide what comes next.
What can attackers do from operational standpoint
To evade endpoint defenses, attackers can execute inline binaries, load dynamic link libraries and run .NET assemblies directly from memory.
The framework also enables operators to establish SOCKS5 proxies, allowing them to tunnel traffic and pivot deeper into segmented internal systems.
TencShell is derived from Rshell, an open-source Go-based C2 framework designed for cross-platform offensive security use. The original Rshell project includes remote command execution, file and process management, terminal access, in-memory payload execution, multiple C2 transports, and an MCP server. The version we observed was customized and repackaged for this operation, with communication and delivery changes that made it more suitable for the attacker’s campaign.
Embedded Go source paths in TencShell exposed the Reacon project structure and the threat actor user, as shown in Figure 1.
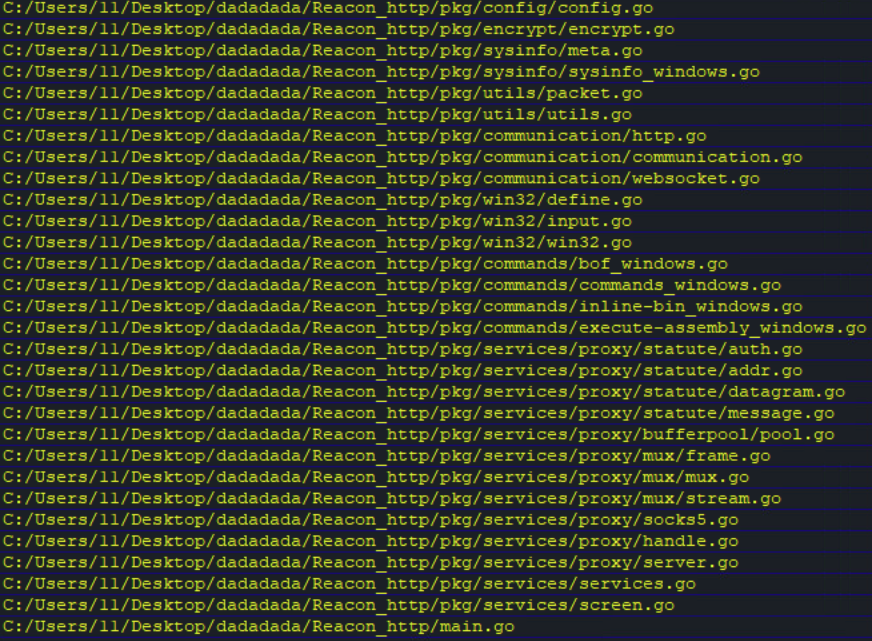
Figure 1. TencShell Go paths revealing the threat actor’s REACON project
Conclusion: The framework for Malware classification system (MCS) if adopted to analyze malware behavior dynamically using a concept of information theory and a machine learning technique will be useful for manufacturing organizations.
Any proposed framework will extracts behavioral patterns from execution reports of malware in terms of its features and generates a data repository. The specific aim of any proposed framework detects the family of unknown malware samples after training of a classifier from malware data repository.
Security researchers have the opinion, attackers no longer need custom malware development pipelines to conduct sophisticated intrusions. Adaptable open-source tooling is often enough for implementation and TencShell appears to have been customized from Rshell into a practical post-exploitation implant with web-like C2 communication. This assited the attacker to adapt available offensive tooling and attempted to blend the activity into normal enterprise traffic.
Sources: https://www.catonetworks.com/blog/cato-ctrl-suspected-china-linked-threat-actor-targets-global-manufacturer/











Recent Comments