Microsoft Defender Vulnerability Leveraged in 0-Day Attacks; Patches Rolled Out
Microsoft has released security updates to fix two vulnerabilities in Microsoft Defender that attackers were already exploiting in real-world zero-day attacks. This exploitation was confirmed by CISA, which has added the security flaws to its known exploited vulnerability(KEV) catalogue.
As per Microsoft, they addressed the two security defects in Microsoft Defender Antimalware Platform version 4.18.26040.7. According to the company, systems with Microsoft Defender disabled are not exploitable, even though Defender’s files remain on disk.
CVE-2026-41091, vulnerability affects older versions of the Microsoft Malware Protection Engine used by Microsoft antivirus and anti-malware products.
(CVE-2026-45498,) affects systems running the Microsoft Defender Antimalware Platform 4.18.26030.3011 and earlier.
| CVE ID | Affected Product | Vulnerability Description | Potential Impact | Severity Rating |
|---|---|---|---|---|
| CVE-2026-41091 | Microsoft Malware Protection Engine | Vulnerability affecting older versions of the Microsoft antivirus and anti-malware scanning engine | Privilege escalation allowing attackers to gain SYSTEM-level access | 🔴 Critical |
| CVE-2026-45498 | Microsoft Defender Antimalware Platform 4.18.26030.3011 and earlier | Vulnerability affecting Microsoft Defender and related endpoint protection platforms | Security risk impacting endpoint protection systems and enterprise security tools | 🟠 High |
CVE-2026-41091 vulnerability affects:
- The flaw allows attackers to trick the antivirus engine into accessing files incorrectly.
- By exploiting this weakness, attackers can gain SYSTEM-level privileges, which is the highest level of access on a Windows system.
- With this access, attackers could potentially take full control of the affected device.
CVE-2026-45498 vulnerability affects:
Attackers can exploit the flaw to make affected Windows systems stop responding or crash. This creates a Denial-of-Service (DoS) condition, where the device or security service becomes unavailable temporarily.
As a result, users may experience:
- System slowdowns or freezes
- Security services stopping unexpectedly
CISA Adds the vulnerability in its KEV
For Malware attacks the vulnerability fits well and attackers are in advantageous position. In first to prevent detection if the system relies only on Microsoft endpoint protection and second to gain full control over the system.
On Wednesday, the United States Cybersecurity and Infrastructure Security Agency (CISA), added the two vulnerabilities, tracked as CVE-2026-41091 and CVE-2026-45498, to its Known Exploited Vulnerabilities (KEV) catalog, signaling that exploitation was detected in the wild.
Privilege Escalation Flaw:
The vulnerability CVE-2026-41091 is a Privilege Escalation (PE) flaw affecting mpengine.dll, a core component of the Microsoft Malware Protection Engine used by Microsoft Defender and other Microsoft security products.
mpengine.dll (Microsoft Malware Protection Engine) is responsible for:
- Malware scanning
- Threat detection
- File inspection
- Cleaning and remediation operations
- The vulnerability arises from an improper link resolution before file access issue, commonly referred to as a link following vulnerability.
- During scanning or file operations, the engine may improperly handle symbolic links, junctions, or reparse points before validating the target file path.
- An attacker can exploit this behavior by crafting malicious file links that redirect privileged operations to unintended system locations.
“This type of vulnerability is a frequent attack vector for malicious cyber actors and poses significant risks to the federal enterprise,” the U.S. cybersecurity agency warned.
“Apply mitigations per vendor instructions, follow applicable BOD 22-01 guidance for cloud services, or discontinue use of the product if mitigations are unavailable.”
On Tuesday, also shared mitigations for YellowKey, a recently disclosed Windows BitLocker zero-day flaw that allows attackers to access protected drives.
CISA gave federal agencies until June 3 to ensure mitigation measures are in place.
Threat Mitigation advice from Microsoft:
“For enterprise deployments as well as end users,” Microsoft said, “the default configuration in Microsoft antimalware software helps ensure that malware definitions and the Microsoft Malware Protection Engine are kept up to date automatically,” and as such no action is required as the update that is now rolling out will get applied without user input.
Most Windows systems using Microsoft Defender are configured to update automatically. What happens if automatic updates are enabled, users usually do not need to manually install the security fix.
It is assumed Microsoft Defender should automatically download and apply the updated malware protection engine and required security update in the background.
One can ensure that all the latest updates are installed and configures device protection against the recently disclosed vulnerabilities.
The April 2026 vulnerabilities identified in Defender:
Few months back we have witnessed how a zero-day vulnerability in Microsoft Defender, dubbed “RedSun,” allowed an unprivileged user to escalate privileges to full SYSTEM-level access on fully patched Windows 10, Windows 11, and Windows Server 2019 and later systems.
RedSun was the second zero-day exploit published within a two-week span in April 2026 by the security researcher known as “Chaotic Eclipse”
For threat mitigation it was advised that security teams should closely watch for suspicious activity involving Microsoft Defender until Microsoft releases an official fix. Attackers may try to misuse certain Windows files and Defender processes to gain higher access or modify protected system files.
RakshaOne from Intrucept helps simplify workflows by automatically handling alerts, allowing for faster detection of both known and unknown threats.
SIEM Helps Detect Exploitation
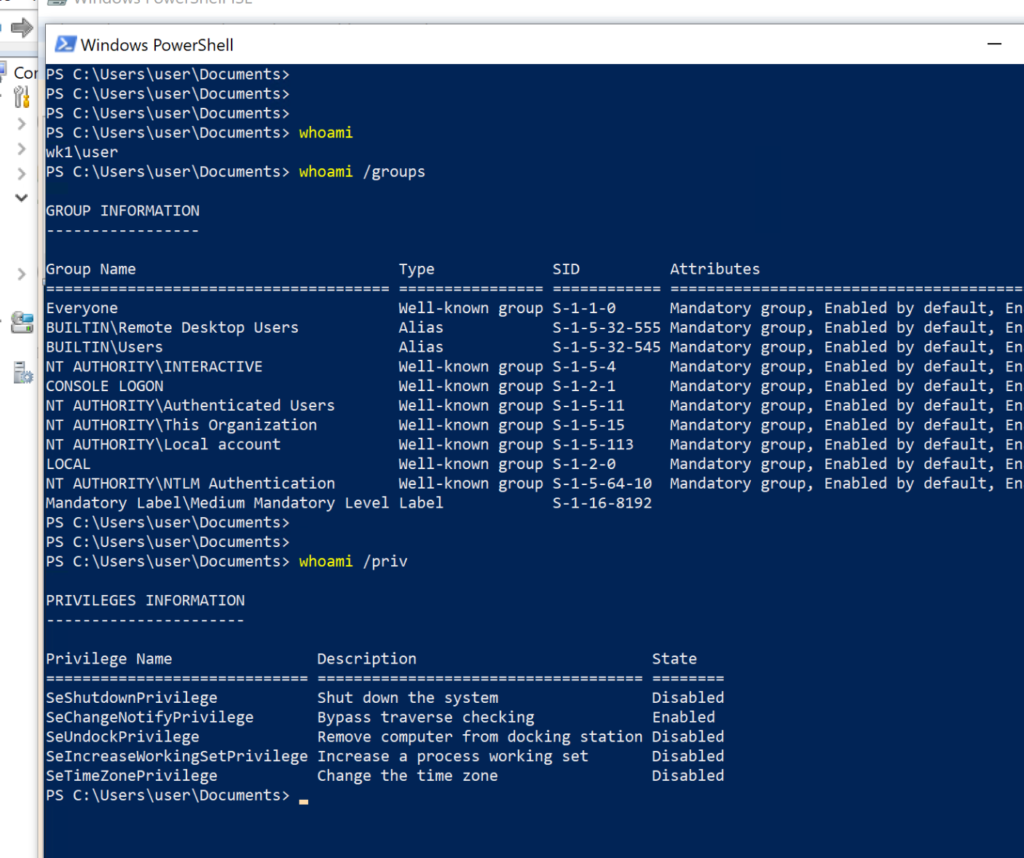
Privilege Escalation Detection (CVE-2026-41091)
The SIEM can correlate:
- Suspicious file write activity
- Abnormal SYSTEM privilege assignments
- Unexpected execution of privileged processes
- Defender engine (
mpengine.dll) anomalies - Unauthorized access attempts to protected system directories
DoS & Security Service Monitoring (CVE-2026-45498)
The SIEM can detect:
- Unexpected Microsoft Defender crashes
- Antimalware service restarts
- Endpoint protection failures
- Repeated system instability events
- Disabled or unavailable Defender services
This helps security teams identify attempts to disrupt endpoint protection mechanisms
Sources: Security Update Guide – Microsoft Security Response Center
Sources:










Recent Comments