Insider Threat Target for Hacking Campaigns Turns Risky for Organization’s
Insider Threat Target for Hacking Campaigns Turns Risky for Organization’s
Continue ReadingInsider Threat Target for Hacking Campaigns Turns Risky for Organization’s
Continue ReadingAPT28 attack executes when victims open malicious documents in Microsoft Office:
Continue ReadingCisco Patched Zero-Day RCE Exploited by China-Linked APT in Secure Email Gateways
Continue ReadingCloud exposure led to breach by hackers
Continue ReadingSecuring IoT Devices
Continue ReadingSummary : VMware fixed four vulnerabilities in VMware ESXi, Workstation, Fusion and VMware Tools that were exploited as zero-days during the Pwn2Own Berlin 2025 hacking contest in May 2025.
| OEM | Broadcom |
| Severity | Critical |
| CVSS Score | 9.3 |
| CVEs | CVE-2025-41236, CVE-2025-41237, CVE-2025-41238, CVE-2025-41239 |
| Actively Exploited | No |
| Exploited in Wild | No |
| Advisory Version | 1.0 |
Overview
These vulnerabilities, now tracked as CVE-2025-41236, CVE-2025-41237, CVE-2025-41238 and CVE-2025-41239, could allow attackers with local administrative privileges on a virtual machine to execute arbitrary code on the host system or leak sensitive memory content.
VMware has released critical patches for affected products, including ESXi 7/8, Workstation Pro 17.x, Fusion 13.x and VMware Tools.
| Vulnerability Name | CVE ID | Product Affected | Severity | Fixed Version |
| VMXNET3 Integer Overflow | CVE-2025-41236 | ESXi, Workstation, Fusion | Critical (CVSS 9.3) | ESXi80U3f-24784735, ESXi70U3w-24784741, ESXi80U2e24789317, Workstation 17.6.4, Fusion 13.6.4 |
| VMCI Integer Underflow | CVE-2025-41237 | ESXi, Workstation, Fusion | Critical (CVSS 9.3) | Same as above |
| PVSCSI Heap Overflow | CVE-2025-41238 | ESXi, Workstation, Fusion | Critical (CVSS 9.3) | Same as above |
| vSockets Info Disclosure | CVE-2025-41239 | ESXi, Workstation, Fusion, VMware Tools | High (CVSS 7.1) | VMware Tools 13.0.1.0, same ESXi/Workstation/Fusion versions |
Technical Summary
These vulnerabilities impact key virtualization components, potentially enabling virtual machine breakout or data leakage from the host system.
The exploitation requires local admin privileges on the guest VM and varies in impact depending on the platform (ESXi, Workstation, or Fusion).
| CVE ID | System Affected | Vulnerability Details | Impact |
| CVE-2025-41236 | ESXi 7/8, Workstation 17.x, Fusion 13.x | Integer overflow in VMXNET3 adapter allows arbitrary code execution on the host via specially crafted network packets from a guest VM. | Host code execution from guest VM |
| CVE-2025-41237 | Same as above | Integer underflow in VMCI component can lead to out-of-bounds write and code execution in the VMX process on the host. | VM breakout; Host compromise (Workstation/Fusion) |
| CVE-2025-41238 | Same as above | Heap overflow in the PVSCSI controller allows out-of-bounds write more severe on Workstation/Fusion than ESXi due to sandbox restrictions. | Host compromise (desktop platforms); limited on ESXi |
| CVE-2025-41239 | ESXi 7/8, Workstation 17.x, Fusion 13.x, VMware Tools | Use of uninitialized memory in vSockets allows information disclosure to attackers with local VM admin rights. | Memory leak from host to guest |
Remediation:
Users and administrators are strongly advised to immediately apply the following patches to mitigate the vulnerabilities:
Conclusion:
These vulnerabilities pose a serious threat to virtualization security, especially in environments using VMware Workstation and Fusion. A successful exploit could enable attackers to escape the virtual machine and compromise the host system.
Administrators should prioritize patching to avoid exposure and reduce the risk of virtual infrastructure compromise. Regular audits of virtual networking components and least-privilege access controls within guest VMs are also recommended.
References:
Kibana is a robust tool for data visualization and exploration that can be used to search, examine, and track data that is stored in Elasticsearch. A vital part of many organizations’ data analysis procedures, it offers real-time insights through interactive dashboards.
Elastic released security updates to address a critical vulnerability, tracked as CVE-2025-25012 (CVSS score of 9.9), impacting the Kibana data visualization dashboard software for Elasticsearch.
| OEM | Elastic |
| Severity | Critical |
| CVSS | 9.9 |
| CVEs | CVE-2025-25012 |
| Exploited in Wild | No |
| Patch/Remediation Available | Yes |
| Advisory Version | 1.0 |
Overview
A critical security vulnerability (CVE-2025-25012) has been identified in Kibana, affecting versions 8.15.0 to 8.17.2. The flaw allows attackers to execute arbitrary code, potentially compromising affected systems. Elastic has released a patch in Kibana version 8.17.3to address this issue, and users are strongly advised to update immediately.
| Vulnerability Name | CVE ID | Product Affected | Severity |
| Arbitrary code execution Vulnerability | CVE-2025-25012 | Elastic | Critical |
Technical Summary
This vulnerability arises from improper handling of JavaScript object prototypes in Kibana’s file upload and HTTP request processing functionalities.
Attackers can exploit this flaw to inject malicious payloads, modify application behavior, and execute arbitrary code. The vulnerability is classified under CWE-1321 (Improper Control of Prototype-Based Attribute Modifications) and aligns with the MITRE ATT&CK framework under tactic T1059 (Command and Scripting Interpreter).
Affected Versions and Exploitation Conditions:
| CVE ID | System Affected | Vulnerability Details | Impact |
| CVE-2025-25012 | Kibana 8.15.0 – 8.17.2 | Prototype pollution via crafted file uploads and HTTP requests, allowing manipulation of JavaScript object properties and security controls. | Remote Code Execution, Unauthorized Data Access, Lateral Movement |
Remediation:
Conclusion:
Organizations utilizing Kibana should take urgent action to patch CVE-2025-25012 by upgrading to version 8.17.3.
The vulnerability is highly severe, particularly for environments using Kibana for security monitoring, as attackers could exploit this flaw to disable alerts and manipulate detection pipelines. If patching is not immediately possible, temporary mitigations should be applied to reduce the risk of exploitation. Ensuring real-time vulnerability monitoring and implementing strict access controls are also recommended to safeguard against similar threats in the future.
References:
Image
Overview
Cybersecurity researchers at Check Point Research (CPR) have discovered a sophisticated macOS malware called Banshee Stealer, putting over 100 million macOS users globally at risk. The malware, designed to exfiltrate sensitive user data, demonstrates advanced evasion techniques, posing a significant threat to users and organizations relying on macOS.
Key Threat Details:
Malware Capabilities:
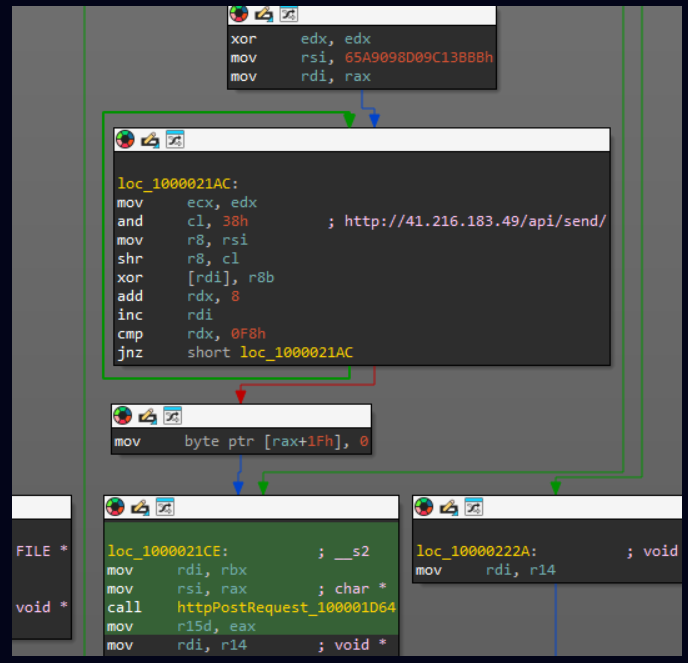
C&C decryption Source: Cybersecurity News
Evasion Tactics:
Distribution Mechanisms:

Repository releases source: Cybersecurity News
Recent Developments:
Impact:
Indicators of Compromise (IOCs):
The IOCs listed below are associated with the threat. For the full list of IOCs, please refer to the link .
| IP Address and Domain | File Hash |
| 41.216.183[.]49 | 00c68fb8bcb44581f15cb4f888b4dec8cd6d528cacb287dc1bdeeb34299b8c93 |
| Alden[.]io | 1dcf3b607d2c9e181643dd6bf1fd85e39d3dc4f95b6992e5a435d0d900333416 |
| api7[.]cfd | 3bcd41e8da4cf68bb38d9ef97789ec069d393306a5d1ea5846f0c4dc0d5beaab |
| Authorisev[.]site | b978c70331fc81804dea11bf0b334aa324d94a2540a285ba266dd5bbfbcbc114 |
Recommendations:
To mitigate the risks associated with Banshee Stealer, consider implementing the following proactive measures:
Conclusion:
The rise of the Banshee malware exemplifies the increasing sophistication of threats targeting macOS. Users and organizations must adopt layered security defenses, maintain vigilance, and prioritize awareness to mitigate the risks of advanced malware like Banshee. By leveraging updated tools and practices, you can safeguard critical systems and data from evolving cyber threats.
References:
Race Condition Vulnerability in OpenSSH (CVE-2024-6387): PoC Exploit Released
OpenSSH is a suite of networking utilities based on the Secure Shell (SSH) protocol. It is extensively used for secure remote login, remote server management and administration, and file transfers via SCP and SFTP. OpenSSH server process ‘sshd’ is affected by a signal handler race condition allowing unauthenticated remote code execution with root privileges on glibc-based Linux systems.
Summary
| Application | OpenSSH |
| Severity | High |
| CVSS | 8.1 |
| CVEs | CVE-2024-6387 |
| Exploited in Wild | Yes |
| Patch/Remediation Available | Yes |
| Advisory Version | 1.0 |
Overview
CVE-2024-6387, a high-severity vulnerability in OpenSSH’s server (sshd), has been identified and is currently being exploited in the wild. Known as “regreSSHion,” this flaw involves a sophisticated race condition during the authentication phase, allowing unauthenticated remote attackers to execute arbitrary code with root privileges.
A proof-of-concept (PoC) exploit for this critical vulnerability has been released, further raising concerns.
The vulnerability affects millions of OpenSSH servers globally, with older versions particularly at risk. Rated with a CVSS score of 8.1, the flaw poses a significant security threat. Over 14 million OpenSSH server instances exposed to the Internet have been identified as potentially vulnerable, with around 700,000 instances facing external internet threats.
| Vulnerability Name | CVE ID | Product Affected | Severity | Fixed Version |
| Race Condition vulnerability | CVE-2024-6387 | OpenSSH (8.5p1–9.8p1) | High | OpenSSH 9.8p2 or later |
Technical Summary
CVE-2024-6387, also known as “regreSSHion,” is a critical vulnerability in OpenSSH’s server (sshd) caused by a signal handler race condition. This issue arises when the SIGALRM handler, triggered during a failed login attempt exceeding LoginGraceTime, invokes non-async-signal-safe functions like syslog(). The Vulnerability allows unauthenticated remote attackers to execute arbitrary code with root privileges, primarily affecting glibc-based Linux systems.
Exploitation is technically complex but feasible and has been demonstrated in controlled environments on 32-bit systems. OpenBSD systems are unaffected due to their different signal-handling mechanisms.
| CVE ID | System Affected | Vulnerability Details | Impact |
| CVE-2024-6387 | OpenSSH v8.5p1 through 9.8p1 on glibc-based Linux systems | Signal handler race condition in sshd’s SIGALRM, triggered during login timeout (LoginGraceTime). | Remote Code Execution (Root Privileges) |
Impact:
This Vulnerability if exploited could lead to complete system takeover.
Remediation:
Indicators of Compromise (IOCs):
| IP Address / Hostname | File Hash |
| 209.141.53[.]247 | 0df799f05c6d97e2b7d4b26c8e7246f7 |
| 108.174.58[.]28 | 11cc5f00b466d4f9be4e0a46f2eb51ae |
| 195.85.205[.]47 | 1f452448cea986aedc88ba50d48691f7 |
| 62.72.191[.]203 | 207eb58423234306edaecb3ec89935d8 |
| botbot.ddosvps.cc |
Below are some IOCs associated with the threat. For a complete list of IOCs, refer to the AlienVault Pulse for CVE-2024-6387
Conclusion:
The public release of a PoC exploit for CVE-2024-6387 marks a critical moment for organizations relying on OpenSSH. While exploitation requires significant effort, the potential impact of a successful attack—complete system compromise and privilege escalation—is severe.
Swift patching and the adoption of layered security measures are imperative to mitigate the risks.
Organizations must act promptly to safeguard their systems and monitor for signs of active exploitation. By staying informed and proactive, businesses can minimize the potential fallout from this serious vulnerability.
References:
New CheckPoint research discovered a new remote access trojan and information stealer used by Iranian state-sponsored actors to conduct reconnaissance of compromised endpoints and execute malicious commands.
Continue Reading
Recent Comments