Corporate Employees Targeted by Vidar Malware
The purpose of Vidar malware is to infiltrate systems and deploy a payload to extract sensitive data.
Continue ReadingThe purpose of Vidar malware is to infiltrate systems and deploy a payload to extract sensitive data.
Continue ReadingAs per researchers hackers are actively exploiting a critical unrestricted-file-upload vulnerability in SAP NetWeaver Visual Composer. Regarding this urgent patch has been released by SAP to fix CVE-2025-31324, a zero-day vulnerability in SAP NetWeaver Visual Composer.
Critical SAP NetWeaver Zero-day Vulnerability Exploited in the Wild
The vulnerability in SAP NetWeaver Visual Composer that may have allowed unauthenticated and unauthorized code execution in certain Java Servlets.
Several cybersecurity companies have reported active exploitation in the wild.
Summary
| OEM | SAP |
| Severity | Critical |
| CVSS Score | 10.0 |
| CVEs | CVE-2025-31324 |
| POC Available | No |
| Actively Exploited | Yes |
| Exploited in Wild | Yes |
| Advisory Version | 1.0 |
Overview
This vulnerability enables remote uploading and execution of malicious files by unauthenticated attackers, potentially compromising the entire system.
It is highly advised to implement patching or mitigation measures right away in order to guard against possible espionage, sabotage, data theft, and operational disruption.
| Vulnerability Name | CVE ID | Product Affected | Severity | CVSS Score |
| Missing Authorization in Metadata Uploader | CVE-2025-31324 | SAP | Critical | 10.0 |
Technical Summary
The vulnerability stems from a missing authorization check in the Metadata Uploader component of SAP NetWeaver Visual Composer.
Attackers can exploit this by sending crafted unauthenticated POST requests to the development server/meta data uploader endpoint, allowing them to upload arbitrary JSP webshell files.
Once uploaded, attackers can interact with these shells via simple GET requests to execute arbitrary commands, resulting in remote code execution (RCE) with <sid>adm operating system privileges — effectively giving full control over SAP systems.
| CVE ID | System Affected | Vulnerability Details | Impact |
| CVE-2025-31324 | SAP NetWeaver Visual Composer (VCFRAMEWORK 7.50) | Missing authorization check at /developmentserver/metadatauploader enables unauthenticated malicious file uploads. Webshells planted can be used to execute OS-level commands, deploy additional malware, and move laterally across the network. | Full system compromise including: – Remote Command Execution – Privilege Escalation – Data Exfiltration – Ransomware Deployment – Potential Espionage/Sabotage/Fraud |
Key Exploitation Details:
Risk Factors:
Remediation:
Recommendations:
Scan for suspicious JSP files (e.g., helper.jsp, cache.jsp) in these directories:
Conclusion:
Given the criticality and active exploitation of CVE-2025-31324, organizations running SAP NetWeaver Visual Composer should prioritize patching and mitigation efforts. The potential for full system compromise, ransomware attacks, and data exfiltration represents a severe business risk. Immediate action is strongly advised to secure SAP environments and prevent exploitation.
References:
MUT-8694: Threat Actors Exploiting Developer Trust in Open-Source Libraries
Overview
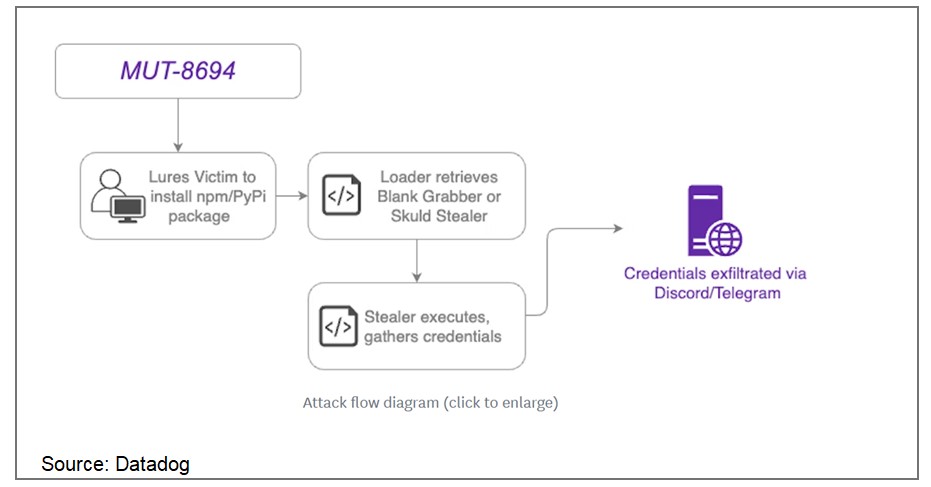
In November 2024, a supply chain attack designated as MUT-8694 was identified, targeting developers relying on npm and PyPI package repositories. This campaign exploits trust in open-source ecosystems, utilizing typosquatting to distribute malicious packages. The malware predominantly affects Windows users, delivering advanced infostealer payloads.
MUT-8694 Campaign Details
The threat actors behind MUT-8694 use malicious packages that mimic legitimate libraries to infiltrate developer environments. The campaign employs techniques such as:
Source: Datadog
Key Findings
One identified package, larpexodus (version 0.1), executed a PowerShell command to download and run a Windows PE32 binary from github[.]com/holdthaw/main/CBLines.exe. Analysis revealed the binary was an infostealer malware, Blank Grabber, compiled from an open-source project hosted on GitHub. Further inspection of the repository exposed another stealer, Skuld Stealer, indicating the involvement of multiple commodity malware samples.
Capabilities of Malware
The deployed malware variants include advanced features that allow:
Affected Packages
Some known malicious packages include:
Remediation:
To mitigate the risks associated with this attack, users should:
General Recommendations:
References:
Recent Comments