ISAC’s Joint Advisory as Cyber & Physical Risks Increase in MiddleEast Conflict; Major Hacking Groups are Threat to Critical Infrastructure
ISAC’s Joint Advisory
Continue ReadingAPT28 attack executes when victims open malicious documents in Microsoft Office:
Continue ReadingAI-Driven Attacks Become More Autonomous
Continue ReadingCyber Security Trends 2026; Cloud Environments, Identity systems & Third-Party Tools Key Area’s of Threat
Continue ReadingSurge in Cyber Security Spending; Focus on Cloud Security & AI in 2026
Continue ReadingBISO Analytics from Intrucept ‘A Unified platform to map Business risk with Cyber Risk
Continue ReadingUK unveiled the Cyber Security and Resilience Bill that aligns with NIS2 but with changes to get better clarity on cyberattacks on the UK’s most critical sectors and send actionable advice to cyber defenders. In 2025 alone we have witnessed series of damaging cyber incidents that exposed vulnerabilities in UK’s critical infrastructure, made it worrisome and DSIT study estimated that cyberattacks cost the UK economy about $19.4 billion (£14.7 billion) each year or about 0.5% of the GDP.
The current bill has five major changes which reflects UK’s effort at modernizing the framework originally set out in the NIS Directive. Since its announcement during the King’s Speech on 17 July 2024, there has been much anticipation over the contents of the Cyber Security and Resilience Bill (“CS&R Bill“) and in particular the extent to which it will bring the UK into alignment with its European counterpart, the NIS2 directive.
As UK unveiled the Cyber Security and Resilience Bill, last week it made mandatory for organizations in healthcare, energy, water, transport and digital services to meet required security standards and report significant cyber incidents within 24 hours.
Further the bill has stated that govt. has right to imposing turnover-based penalties and granting ministers emergency powers to intervene during major cyber incidents. In its current form, the bill has fallen out of date and are insufficient to tackle the cyber threats reflected in recent months cyber attacked across verticals in UK and Europe.
Key 5 changes in UK cybersecurity regulation arising from the Bill
1. Data center operators will now fall within scope of the NIS Regulations
At present, the NIS Regulations cover two types of covered entities—”operators of essential services” (“OESs,” including the main types of critical infrastructure, such as energy, transport, and water providers) and “digital service providers” (“DSPs,” specifically cloud computing, online search engines, and online marketplaces).
The Bill will expand the scope of the OES designation to cover providers of data center services that offer a rated IT load of more than 10 megawatts, and are provided “on an enterprise basis.” The Bill’s definition of “data centre service” broadly follows the equivalent definition in NIS2 but is more detailed; in essence, it covers the provision of data center space and supporting infrastructure (e.g., utilities and security infrastructure).
The Bill will also expand the scope of the NIS Regulations to cover:
2. Govt. reserves right to impose more specific security requirements
In present the cybersecurity bill the NIS Regulations require OESs to report to competent authorities any incident that “has a significant impact on the continuity of the essential service which that OES provides” to its competent authorities, taking into account factors such as the number of affected users, the duration of the incident, and the geographical area affected.
The Bill will expand the types of incidents that are reportable, in some cases extending to incidents that have had or are likely to have a “significant impact” in the UK.
In addition, the Bill will impose an obligation on OESs, DSPs, and managed service providers to notify customers that are likely to be “adversely affected” by the incident, taking into account the level of any disruption, any impact on that customer’s data, and any impact on their other systems
3. Supply chain security for OESs will be issued by creating a new category of “critical suppliers”
The cybersecurity Bill would permit competent authorities responsible for overseeing OESs and DSPs to designate—subject to a consultation process—“critical suppliers,” i.e., individuals or organizations that rely on network and information systems to provide goods or services to an OES or DSP, for whom an incident would have the potential to cause disruption to the provision of an essential service that is likely to have a “significant impact on the economy or day-to-day functioning of society” in the UK.
As drafted, the Bill does not impose specific obligations on critical suppliers.
4. Increased fines and enhanced powers for competent authorities
The Bill empowers competent authorities to share information related to incidents among themselves, with law enforcement, with GCHQ, and with OESs, DSPs, managed service providers, and critical suppliers where necessary and may include foreign competent authorities.
The Bill would also amend the NIS Regulations to set out in more detail the powers of competent authorities to demand information from covered providers, carry out inspections and take enforcement action.
5. More empowering role for Govt in UK for cybersecurity regulation in the future
Parts 3 and 4 of the Bill establish a framework for the UK Government to set both the broad strategic direction for competent authorities’ oversight and enforcement of cybersecurity, and to impose more granular obligations on covered providers.
By empowering the bill states that any issue codes of practice, setting out more detail on the measures covered providers could take to comply with their obligations under the NIS Regulations. This also means the Government requires to maintain a statement of its strategic priorities in relation to cybersecurity. This includes a framework for imposing obligations on providers for national security purposes.
The cyber security bill in alignment to NIS2 if enacted, it will represent the most comprehensive update to the UK’s cybersecurity legal framework in years, with far-reaching implications for businesses operating in the UK market. The current cybersecurity landscape and cyber threat increases the bill’s significance to national security and the UK government’s stated priority, it is likely to receive expedited consideration.
Key provisions the cyber security bill has adapted keeping the scope of work for managed service providers, incident reporting and regulated entities
The Bill would expand the scope of the UK NIS to cover certain managed service providers and critical suppliers and the scope of covered operators of essential services (OESs) to include data center operators and load control providers. The Bill would create a new classification of “managed service providers,” with specific obligations (e.g., registration requirements) for “relevant managed service providers” (RMSPs).
The Bill would also create a category of “critical suppliers.” Regulatory authorities would designate critical suppliers under certain circumstances, specifically where an entity uses network or information systems to supply goods or services to an OES and an incident disrupting the entity could significantly impact the UK.
The Bill would both expand existing OES incident reporting requirements and create separate regulatory and customer notice obligations for data center operators, relevant digital service providers (RDSPs) and RMSPs.
The Bill would require that after an OES incident, the OES notify not only the relevant sectoral regulator but also the NCSC. The scope of reportable OES incidents would be broadened to include those that affect the operation or security of the IT systems relied on to provide the essential service.
Separately the Bill would add a subsector for “data infrastructure” that includes certain data center operators. These data center operators would be subject to unique reporting requirements. The Bill would also add “large load controllers” to the existing electricity subsector. This includes electrical load controllers with potential electrical control of at least 300 MW.
Conclusion:
Many of these concepts align, at least in part, with the EU NIS 2. NIS 2 also regulates managed service providers, critical entities and data centers, although it lacks a category specifically for large load control services.
Growing cyber attacks in recent months that incurred losses for organization’s like Marks & Spenser, Jaguar Land rover which cost millions to recover from losses, the corporates have welcomed the move to strengthen legislation and regulatory powers to help drive up the level of defense and resilience across critical national infrastructure.
The UK government’s planned National Cyber Strategy refresh will articulate a vision – and agreed collective action in partnership with businesses, devolved governments, regulators.
The new bill will secure UK more against cyber threats and lower disruption rates to local services and businesses including faster response against emerging threats.
(Sources: UK cybersecurity bill brings tougher rules for critical infrastructure | CSO Online)
Data Breach with 30 exposed Datasets & contained approx 10 to 3.5 billion records making it one of the largest data breach.
According to a report security researchers from Cybernews found about a Data breach that leaked important data or passwords that was mostly generated by various cybercriminals using info stealing malware. They exposed data was made to look like a breach but these login credentials were gathered from social media, corporate platforms, VPNs etc via infostealer.
Now cybercriminals have unprecedented access to personal credentials and these credentials be used for account takeover, identity theft and targeted phishing activities.
The concern is the structure and recency of these datasets as they are not old breaches being recycled. This is fresh, weaponizable intelligence at scale”, added researchers.
The data sets contains a mix of details from stealer malware, credential stuffing sets and repackaged leaks. There is no way to compare these datasets, but likely to contain at least some duplicated information. This makes it hard to determine how many people were affected by the data breach.
What are Data sets & how deadly can be Infostealer as a malware?
Datasets are basically structure collection of data collected over the years or so and organized as case specific models
In 2024 datasets containing billions of passwords have previously found their way on the internet. Last year, researchers came across what they called the Mother of All Breaches, which contained more than 26 billion records.
The data breach that happened had data in sets, following a particular pattern, containing an URL followed by a username and password. To those unaware, this is exactly how infostealing malware collects information and sends it to threat actors.
The exposed data came from platforms widely used round the world starting from Google, Apple, Github, Telegram & Facebook. So data was first collected over a period of time, further made into data sets and grouped together.
Info stealers are malware programs that are designed to silently steal usernames and passwords Basically designed to swipe of credentials from people’s devices and send them to threat actors for further them for sale on dark web forums.
An infostealer is malware that attempts to steal credentials, cryptocurrency wallets, and other data from an infected device. Over the years, infostealers have become a massive problem, leading to breaches worldwide. No device is spare from infostealer’s impact including Windows and Macs, and when executed, will gather all the credentials it can find stored on a device and save them in what is called a “log.”
If a organization or individual is infected with an infostealer and have hundreds of credentials saved in their browser, the infostealer will steal them all and store them in the log. These logs are then uploaded to the threat actor, where the credentials can be used for further attacks or sold on cybercrime marketplaces.
An infostealer log is generally an archive containing numerous text files and other stolen data.
Fig1:
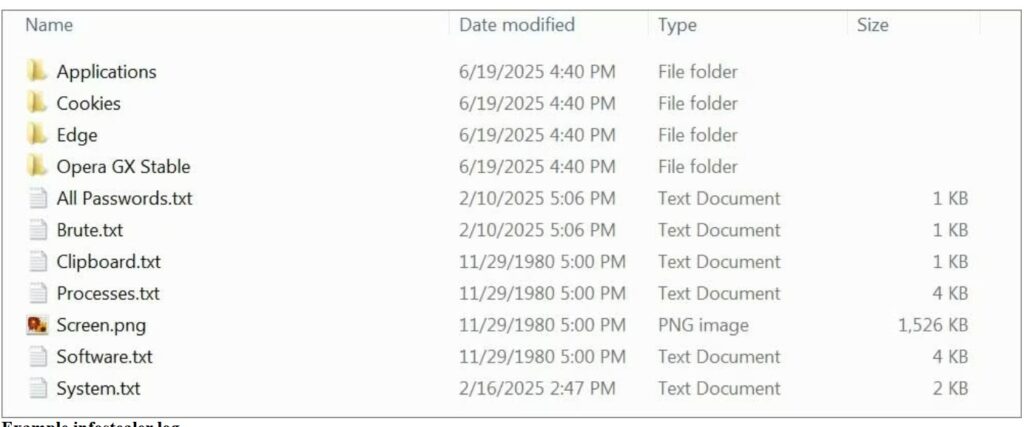
(Image courtesy: Bleeping computers)
A devastating data breach is a nightmare for customers and affected organizations, but breaches can have a positive side also. Each incident is a learning opportunity. It’s easier to defend critical data when we understand the mistakes made by others and the tactics used by attackers.
How to be secure & keep your Data safe
If users are in midst of data breach or may find that their data is not safe as an infostealer might be there in your systems or devices then scan your device with an antivirus program. Once done then change password or your newly entered credentials could be stolen again. The system is clean so password hygiene can be maintained time to time.
At times even unique passwords won’t help you stay protected if you are hacked, fall for a phishing attack, or install malware. Its better not to change all credentials in one go instead having a cyber security hygiene in routine is better as an option.
Intru360
For organizations to stop and detect any intrusion by attackers prefer to have Intru360 in your list of cyber security go to products from Intruceptlabs.
Intru360 gives security analysts and SOC managers a clear view across the organization, helping them fully understand the extent and context of an attack. It also simplifies workflows by automatically handling alerts, allowing for faster detection of both known and unknown threats.
Globally every year cyberattacks are growing and mutating each month. Organizations have their Intelligent intrusion network detection systems in place analyze and detect anomalous traffic to face these threats.
Do visit our website for more information.
Increasing cyberattacks on Industry 4.0
Continue Reading