Apple iOS & iPadOS Patch 0-Days Vulnerabilities, Exploited in Targeted Attacks
Apple iOS & iPadOS Patch Zero-Days Vulnerabilities, Exploited in Targeted Attacks
Continue ReadingApple iOS & iPadOS Patch Zero-Days Vulnerabilities, Exploited in Targeted Attacks
Continue ReadingSummary: Apple released iOS 26.1 and iPadOS 26, addressed multiple security vulnerabilities across core system components including WebKit, Kernel, Accessibility, Apple Neural Engine, CloudKit etc.
| OEM | Apple |
| Severity | High |
| CVEs | CVE-2025-43438, CVE-2025-43429, CVE-2025-43442, CVE-2025-43455, CVE-2025-43398 & others |
| POC Available | No |
| Actively Exploited | No |
| Exploited in Wild | No |
| Advisory Version | 1.0 |
Overview:
These vulnerabilities could enable malicious apps to escape sandboxes, access sensitive user data, execute arbitrary code via web content, monitor keystrokes or disable theft protection mechanisms. Affected devices include iPhone 11 & later and iPad models from 3rd gen onward etc. Immediate update is strongly recommended to prevent any breaches, system crashes.
| Vulnerability Name | CVE ID | Product Affected | Fixed Version |
| WebKit Use-After-Free (Safari Crash/RCE) | CVE-2025-43438 | iOS, iPadOS | iOS/iPadOS 26.1 |
| WebKit Buffer Overflow (RCE Risk) | CVE-2025-43429 | iOS, iPadOS | iOS/iPadOS 26.1 |
| App Installed Detection via Accessibility | CVE-2025-43442 | iOS, iPadOS | iOS/iPadOS 26.1 |
| Sensitive Screenshot in Embedded Views | CVE-2025-43455 | iOS, iPadOS | iOS/iPadOS 26.1 |
| Kernel Memory Corruption / DoS | CVE-2025-43398 | iOS, iPadOS | iOS/iPadOS 26.1 |
Technical Summary:
The iOS/iPadOS 26.1 update fixes major security issues in sandbox protection, memory handling, privacy settings, and the WebKit browser engine. These critical vulnerabilities could allow apps or websites to access restricted data or execute malicious code. Key impact issues mentioned below.
| CVE ID | Component Affected | Vulnerability Details | Impact |
| CVE-2025-43438 | WebKit | Use-after-free in Safari triggers crash or code execution via malicious web content | Remote Code Execution, System Compromise |
| CVE-2025-43429 | WebKit | Buffer overflow in content processing allows arbitrary code execution | Remote Code Execution, Service Compromise |
| CVE-2025-43442 | Accessibility | Permissions flaw allows apps to detect installed apps (fingerprinting) | Privacy Violation, User Tracking |
| CVE-2025-43455 | Apple Account | Malicious apps can screenshot sensitive embedded UI (login views) | Credential, PII Exposure |
| CVE-2025-43398 | Kernel | Memory mishandling leads to system termination or kernel corruption | Denial of Service, Potential Privilege Escalation |
Additionally, there are multiple high & medium vulnerabilities have been disclosed that enable sandbox escapes, data leaks, and web-based attacks with significant impact potential. Here are some cves in the below table
| Vulnerability Name | CVE ID | Affected Component |
| Sandbox Escape via Assets | CVE-2025-43407 | Assets |
| Sandbox Escape via CloudKit Symlink | CVE-2025-43448 | CloudKit |
| Stolen Device Protection Bypass | CVE-2025-43422 | Stolen Device Protection |
| Cross-Origin Data Exfiltration | CVE-2025-43480 | WebKit |
| Keystroke Monitoring via WebKit | CVE-2025-43495 | WebKit |
| Apple Neural Engine Kernel Corruption | CVE-2025-43447, CVE-2025-43462 | Apple Neural Engine |
| Canvas Cross-Origin Image Theft | CVE-2025-43392 | WebKit Canvas |
| Contacts Data Leak in Logs | CVE-2025-43426 | Contacts |
| Lock Screen Content Leak | CVE-2025-43350 | Control Center |
| Address Bar Spoofing | CVE-2025-43493 | Safari |
| UI Spoofing in Safari | CVE-2025-43503 | Safari |
Recommendations:
Update all eligible devices immediately (Settings > General > Software Update products) to the following fixed versions as soon as possible and check the updated version from the Apple security website.
Patches are available and should be applied immediately.
For environments where immediate patching is not immediately feasible, you can also follow the recommendations below.
Conclusion:
The iOS/iPadOS 26.1 update fixes several security vulnerabilities that could affect user privacy, device stability, and system protection.
Organizations and Individual using Apple devices must prioritize deployment of this update to mitigate risks of data exfiltration, spyware and other attack vectors. Timely patching remains the most effective control against zero-day exploitation on new vulnerabilities in digital ecosystems.
References:
Security Advisory : Apple has released critical security patches to address a newly discovered zero-day vulnerability, CVE-2025-43300, that was found to be actively exploited in targeted attacks.
To protect users, Apple has issued patches in iOS 18.6.2, iPadOS 18.6.2, iPadOS 17.7.10 and the latest macOS versions.
| OEM | Apple |
| Severity | High |
| CVSS Score | 8.8 |
| CVEs | CVE-2025-43300 |
| POC Available | No |
| Actively Exploited | Yes |
| Exploited in Wild | Yes |
| Advisory Version | 1.0 |
Overview The vulnerability resides in Apple’s ImageIO framework, which is used for handling image files across iOS, iPadOS, and macOS platforms. According to Apple, the flaw may have been used in sophisticated, targeted attacks, although exact details have not been disclosed.
The vulnerability affects a wide range of devices, including iPhones starting from the XS, multiple iPad models and Macs running macOS Ventura, Sonoma and Sequoia. This marks the seventh zero-day exploited in the wild that Apple has addressed in 2025, underscoring the increasing frequency and severity of threats targeting Apple users.
| Vulnerability Name | CVE ID | Product Affected | Severity | Fixed Version |
| An out-of-bounds write issue | CVE-2025-43300 | iPhone, iPad, macOS | High | iOS 18.6.2, iPadOS 18.6.2, iPadOS 17.7.10, macOS 13.7.8, macOS 14.7.8, macOS 15.6.1 |
Technical Summary
The vulnerability, CVE-2025-43300, is classified as an out-of-bounds write issue within the ImageIO framework.
It can be exploited when a specially crafted image file is processed, causing memory corruption that could allow an attacker to execute arbitrary code on the affected device.
This makes it a critical security flaw, particularly because the attack vector image files are common and often considered low risk. Apple has mitigated vulnerability by improving bounds by checking in the affected code.
The exploitation of this bug in the wild indicates a high level of sophistication, likely by advanced persistent threat actors targeting specific individuals. The technical nature of the bug aligns with a broader trend in which attackers exploit flaws in media-handling components to achieve remote code execution. As such, this patch not only fixes a critical issue but also highlights the need for continued vigilance and timely system updates.
| CVE ID | System Affected | Vulnerability Details | Impact |
| CVE-2025-43300 | iPhones, iPads, Macs. | Critical out-of-bounds write vulnerability in Apple’s ImageIO framework that allows remote code execution by processing a malicious image. It has been actively exploited in highly targeted attacks on iOS, iPadOS, and macOS devices, prompting urgent patches. | Remote code execution via malicious image zero-click attack surface |
Apple has so far fixed a total of seven zero-day vulnerabilities in 2025 that were actively exploited in real-world attacks, including CVE-2025-43300, reflecting an ongoing effort to patch critical security flaws across iOS, iPadOS, and macOS platforms.
Remediation:
Update your Apple devices immediately to the latest patched versions:
Conclusion:
Apple has urgently patched seven critical zero-day vulnerabilities in 2025, including CVE-2025-43300, that were actively exploited in targeted attacks.
Users are strongly advised to update their devices immediately to stay protected against these serious threats.
In addition, CISA has added CVE-2025-43300 to its Known Exploited Vulnerabilities (KEV) Catalog under BOD 22-01, requiring federal agencies to remediate the flaw within specified timelines.
While the directive is mandatory for federal agencies, CISA strongly urges all organizations to prioritize remediation of KEV-listed vulnerabilities to reduce their exposure to active threats.
References:
Data Breach with 30 exposed Datasets & contained approx 10 to 3.5 billion records making it one of the largest data breach.
According to a report security researchers from Cybernews found about a Data breach that leaked important data or passwords that was mostly generated by various cybercriminals using info stealing malware. They exposed data was made to look like a breach but these login credentials were gathered from social media, corporate platforms, VPNs etc via infostealer.
Now cybercriminals have unprecedented access to personal credentials and these credentials be used for account takeover, identity theft and targeted phishing activities.
The concern is the structure and recency of these datasets as they are not old breaches being recycled. This is fresh, weaponizable intelligence at scale”, added researchers.
The data sets contains a mix of details from stealer malware, credential stuffing sets and repackaged leaks. There is no way to compare these datasets, but likely to contain at least some duplicated information. This makes it hard to determine how many people were affected by the data breach.
What are Data sets & how deadly can be Infostealer as a malware?
Datasets are basically structure collection of data collected over the years or so and organized as case specific models
In 2024 datasets containing billions of passwords have previously found their way on the internet. Last year, researchers came across what they called the Mother of All Breaches, which contained more than 26 billion records.
The data breach that happened had data in sets, following a particular pattern, containing an URL followed by a username and password. To those unaware, this is exactly how infostealing malware collects information and sends it to threat actors.
The exposed data came from platforms widely used round the world starting from Google, Apple, Github, Telegram & Facebook. So data was first collected over a period of time, further made into data sets and grouped together.
Info stealers are malware programs that are designed to silently steal usernames and passwords Basically designed to swipe of credentials from people’s devices and send them to threat actors for further them for sale on dark web forums.
An infostealer is malware that attempts to steal credentials, cryptocurrency wallets, and other data from an infected device. Over the years, infostealers have become a massive problem, leading to breaches worldwide. No device is spare from infostealer’s impact including Windows and Macs, and when executed, will gather all the credentials it can find stored on a device and save them in what is called a “log.”
If a organization or individual is infected with an infostealer and have hundreds of credentials saved in their browser, the infostealer will steal them all and store them in the log. These logs are then uploaded to the threat actor, where the credentials can be used for further attacks or sold on cybercrime marketplaces.
An infostealer log is generally an archive containing numerous text files and other stolen data.
Fig1:
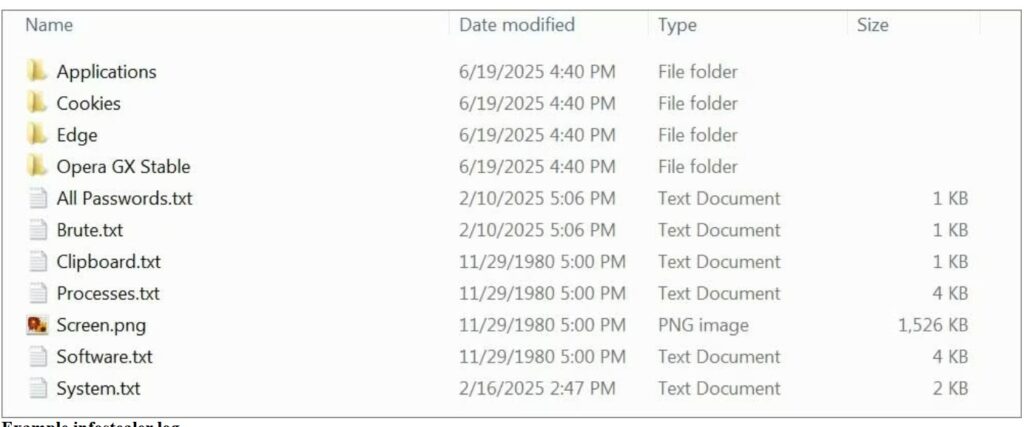
(Image courtesy: Bleeping computers)
A devastating data breach is a nightmare for customers and affected organizations, but breaches can have a positive side also. Each incident is a learning opportunity. It’s easier to defend critical data when we understand the mistakes made by others and the tactics used by attackers.
How to be secure & keep your Data safe
If users are in midst of data breach or may find that their data is not safe as an infostealer might be there in your systems or devices then scan your device with an antivirus program. Once done then change password or your newly entered credentials could be stolen again. The system is clean so password hygiene can be maintained time to time.
At times even unique passwords won’t help you stay protected if you are hacked, fall for a phishing attack, or install malware. Its better not to change all credentials in one go instead having a cyber security hygiene in routine is better as an option.
Intru360
For organizations to stop and detect any intrusion by attackers prefer to have Intru360 in your list of cyber security go to products from Intruceptlabs.
Intru360 gives security analysts and SOC managers a clear view across the organization, helping them fully understand the extent and context of an attack. It also simplifies workflows by automatically handling alerts, allowing for faster detection of both known and unknown threats.
Globally every year cyberattacks are growing and mutating each month. Organizations have their Intelligent intrusion network detection systems in place analyze and detect anomalous traffic to face these threats.
Do visit our website for more information.
Summary
3 Zero-Day Vulnerabilities backported & fixed in Apple Devices
Apple backported fixes for three vulnerabilities that have come under active exploitation in the wild to older models and previous versions of the operating systems.
| OEM | Apple |
| Severity | High |
| CVSS Score | 8.8 |
| CVEs | CVE-2025-24201, CVE-2025-24085, and CVE-2025-24200. |
| No. of Vulnerabilities Patched | 03 |
| Actively Exploited | Yes |
| Exploited in Wild | Yes |
| Advisory Version | 1.0 |
Overview
Apple has released an urgent security advisory concerning three zero-day vulnerabilities currently being actively exploited: CVE-2025-24200, CVE-2025-24201, and CVE-2025-24085. These vulnerabilities affect a range of Apple devices, such as iPhones, iPads, Macs, and other platforms. Users are strongly urged to update to the latest patched versions to reduce security risks.
| Vulnerability Name | CVE ID | Product Affected | Severity | CVSS Score |
| WebKit Out-of-Bounds Write Vulnerability | CVE-2025-24201 | iOS, macOS, visionOS, Safari | High | 8.8 |
| Use-After-Free Vulnerability | CVE-2025-24085 | iOS, iPasOS, macOS, watchOS, tvOS | High | 7.8 |
| Incorrect Authorization Vulnerability | CVE-2025-24200 | iOS, iPadOS | Medium | 6.1 |
Technical Summary
Apple’s latest security update patches three Zero-Day vulnerabilities that hackers were actively exploiting. These vulnerabilities could allow attackers to bypass security protections, making devices more vulnerable. One of the vulnerabilities enables remote code execution, letting attackers run malicious programs. Another flaw allows privilege escalation, giving attackers higher-level access to system functions.
| CVE ID | System Affected | Vulnerability Details | Impact |
| CVE-2025-24201 | iOS 18.3.2, iPadOS 18.3.2, macOS Sequoia 15.3.2, visionOS 2.3.2, Safari 18.3 | Out-of-bounds write issue allowing malicious websites to escape the Web Content sandbox | Remote Code Execution |
| CVE-2025-24085 | iOS 18.3, iPadOS 18.3, macOS Sequoia 15.3, watchOS 11.3, tvOS 18.3, visionOS 2.3 | Use-after-free vulnerability in CoreMedia allowing privilege escalation via malicious apps. | Privilege escalation via CoreMedia |
| CVE-2025-24200 | iOS 18.3.1, iPadOS 18.3.1, iPadOS 17.7.5 (iPhone XS and later, iPad Pro 13-inch, iPad Pro 12.9-inch, etc.) | Authorization bypass vulnerability allowing attackers to disable USB Restricted Mode on locked devices. | Security Bypass USB Restricted Mode |
Remediation:
Apply Patches Promptly: Apple has released security updates to address these vulnerabilities. Users should update their devices immediately to mitigate risks
General Recommendations:
Conclusion:
The discovery and active exploitation of these zero-day vulnerabilities underscore the increasing sophistication of cyberattacks targeting Apple’s ecosystem.
While Apple has responded swiftly with patches, users must remain vigilant by keeping their devices updated and adhering to cybersecurity best practices, such as avoiding untrusted applications and enabling Lockdown Mode where applicable.
Apple fixed all the vulnerability with improved state management.
References:
| OEM | Apple |
| Severity | High |
| CVSS | Not Assigned |
| CVEs | CVE-2025-24200 |
| Exploited in Wild | No |
| Patch/Remediation Available | Yes |
| Advisory Version | 1.0 |
Overview
Apple has issued emergency security patches to mitigate a zero-day vulnerability, CVE-2025-24200, which has been actively exploited in sophisticated attacks targeting specific individuals. The flaw allows attackers to bypass USB Restricted Mode on a locked device, potentially exposing sensitive data. Initially identified by The Citizen Lab, this vulnerability is believed to have been leveraged in real-world scenarios against high-profile targets. Apple has responded by enhancing state management in iOS 18.3.1 and iPadOS 18.3.1 to prevent exploitation.
| Vulnerability Name | CVE ID | Product Affected | Severity |
| USB Restricted Mode Bypass Vulnerability | CVE-2025-24200 | Apple | High |
Technical Summary
The vulnerability, tracked as CVE-2025-24200, affects USB Restricted Mode, a security feature introduced in 2018 to prevent data transfer over USB when a device remains locked for seven days. A flaw in the Accessibility framework allows an attacker with physical access to disable USB Restricted Mode, bypassing this protection and potentially accessing sensitive data.
Apple has mentioned “This issue has been exploited in extremely sophisticated attacks against specific individuals.” The vulnerability was discovered by Bill Marczak, a senior researcher at The Citizen Lab.
| CVE ID | System Affected | Vulnerability Details | Impact |
| CVE-2025-24200 | iPhone XS and later iPad Pro (13-inch) iPad Pro 12.9-inch (3rd generation and later) iPad Pro 11-inch (1st generation and later) iPad Air (3rd generation and later) iPad (7th generation and later) iPad mini (5th generation and later) | A flaw in the Accessibility framework allows a physical attacker to disable USB Restricted Mode, bypassing protections designed to prevent unauthorized data transfer. | Unauthorized access to sensitive data |
Remediation:
Conclusion
The CVE-2025-24200 vulnerability poses a serious risk to device security, particularly for individuals targeted in sophisticated cyberattacks. While the exploitation has been limited to specific individuals, all users of affected devices should install the latest updates immediately to mitigate potential risks. Apple remains committed to user security by addressing vulnerabilities promptly and ensuring continuous protection against emerging threats.
References:
CVE-2025-24085 is a zero-day vulnerability in Apple’s “Core Media framework” which enables malicious applications to potentially gain elevated privileges on impacted devices. It falls under the “Memory Corruption vulnerability category”, posing significant security risks such as unauthorized access to sensitive data or potential device control.
| OEM | Apple Inc |
| Severity | High |
| CVEs | CVE-2025-24085 |
| Exploited in Wild | Yes |
| Patch/Remediation Available | Yes |
| Advisory Version | 1.0 |
| Vulnerability Name | CVE ID | Product Affected | Severity | Affected Version |
| Privilege escalation vulnerability | CVE-2025-24085 | Apple | High | iPhone-XS and later, macOS Sequoia iPad-Pro (3rd generation and later), iPad Air (3rd generation and later), iPad (7th generation and later), iPad mini (5th generation and later) Apple Watch: Series 6 and later Apple TV: All models |
| CVE ID | System Affected | Vulnerability Details | Impact |
| CVE-2025-24085 | iPhone, iPad, Mac, Apple Watch, Apple TV | CVE-2025-24085 is a memory management vulnerability in Apple’s Core Media framework, responsible for processing audio and video content. The vulnerability stems from improper handling of media data, allowing attackers to execute arbitrary code with elevated privileges. It can be remotely exploited through malicious media files, creating significant security risks. | Arbitrary Code Execution, Privilege Escalation, Sensitive Data Exposure, Remote Exploitation via Media Files |
| Affected Version(s) | Fixes and Releases |
| iOS 17.2 and later | iOS 18.3 |
| iPadOS 17.2 and later | iPadOS 18.3 |
| macOS Sequoia (all previous versions) | macOS Sequoia 15.3 |
| watchOS 10.3 and later | watchOS 11.3 |
| tvOS 17.2 and later | tvOS 18.3 |
| visionOS 1.3 and later | visionOS 2.3 |
Apple has fixed this vulnerability in these software versions. Update devices immediately to mitigate the risk of exploitation.
Recent Comments