Python Regression & Email Header- Ubuntu Security Updates Patch Now
Summary: USN-8018-1 fixed vulnerabilities in python3. That update introduced regressions. The patches for CVE-2025-15366 and CVE-2025-15367 caused behavior regressions in IMAP and POP3 handling, which upstream chose to avoid by not backporting them.
| OEM | Python |
| Severity | Medium |
| CVSS Score | 6.5 |
| CVEs | CVE-2026-0865, CVE-2025-15366, CVE-2025-15367 |
| POC Available | No |
| Actively Exploited | No |
| Exploited in Wild | No |
| Advisory Version | 1.0 |
Overview
Python is a widely used high-level programming language that powers many enterprise applications, automation frameworks, DevOps pipelines, web platforms and email-processing services. Many Linux distributions – Ubuntu provide Python runtime packages as core system components.
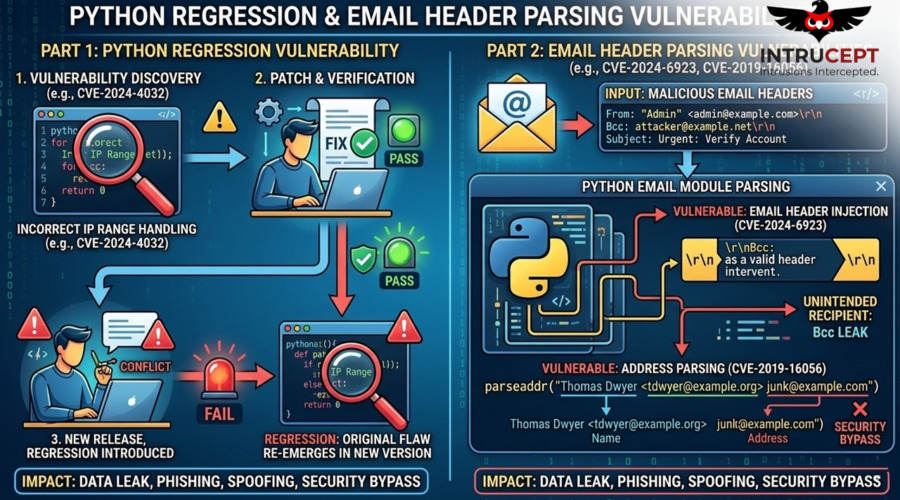
Ubuntu released USN-8018-2 to address regressions introduced in the previous security update USN-8018-1. The earlier update attempted to fix vulnerabilities related to email header parsing and input validation but unintentionally introduced compatibility issues affecting IMAP, POP3, and WSGI header processing.
The new advisory prioritizes the fix for CVE-2026-0865, while also addressing issues related to CVE-2025-15366 and CVE-2025-15367.
| Vulnerability Name | CVE ID | Product Affected | Severity | CVSS Score | Fixed Version |
| WSGI Header Parsing Regression Vulnerability | CVE-2026-0865 | Python | Medium | 6.5 | Updated Python packages |
| Email Header Injection Vulnerability | CVE-2025-15366 | Python | Medium | 5.9 | Updated Python packages |
| Improper Email Header Parsing Vulnerability | CVE-2025-15367 | Python | Medium | 5.9 | Updated Python packages |
Technical Summary
These vulnerabilities affect multiple Python versions distributed within Ubuntu systems.
The original security update introduced patches intended to address email header parsing vulnerabilities. However, those fixes resulted in unintended behavioural regressions.
The CVE-2026-0865 patch incorrectly rejected horizontal tab characters in WSGI headers, potentially causing web applications relying on Python frameworks to malfunction.
Additionally, patches for CVE-2025-15366 and CVE-2025-15367 affected IMAP and POP3 email processing behavior, which allow upstream developers to avoid backporting those changes due to compatibility concerns.
Ubuntu released updated packages to resolve these regressions while maintaining protection against the underlying vulnerabilities.
| CVE ID | System Affected | Vulnerability Details | Impact |
| CVE-2026-0865 | Python (multiple Ubuntu packages) | Incorrect rejection of horizontal tabs in WSGI headers after patch | Web application compatibility issues |
| CVE-2025-15366 | Python email parsing library | Improper parsing allowing email header injection | Email spoofing or message manipulation |
| CVE-2025-15367 | Python email processing modules | Improper validation of message headers | Header manipulation in email processing |
Affected Packages
The following Python packages are affected –
python3.4 python3.5 python3.6 python3.7 python3.8
python3.10 python3.12 python3.13 python3.14
Remediation:
Apply the latest Ubuntu security updates immediately-
Fixed Package Versions
| Ubuntu Release | Fixed Package Version |
| Ubuntu 25.10 | python3.13 – 3.13.7-1ubuntu0.4 / python3.14 – 3.14.0-1ubuntu0.3 |
| Ubuntu 24.04 LTS | python3.12 – 3.12.3-1ubuntu0.12 |
| Ubuntu 22.04 LTS | python3.10 – 3.10.12-1 22.04.15 |
| Ubuntu 20.04 LTS | python3.8 – 3.8.10-0ubuntu1 20.04.18 |
| Ubuntu 18.04 LTS | Updated ESM packages |
| Ubuntu 16.04 LTS | Updated ESM packages |
| Ubuntu 14.04 LTS | Updated ESM packages |
If immediate patching is not possible, apply the following temporary mitigations-
- Restrict access to email-processing services where Python handles inbound messages.
- Validate and sanitize email headers within application logic.
- Monitor logs for abnormal IMAP/POP3 parsing errors.
- Test Python-based web applications to detect WSGI header parsing issues.
You can follow the recommendations below as a best practice-
- Maintain regular patch management for system packages.
- Monitor Python runtime libraries for security advisories.
- Implement secure email validation mechanisms within applications.
- Use application security testing tools to detect input-validation weaknesses.
- Monitor logs for abnormal email header patterns or parsing failures.
Conclusion:
The vulnerabilities addressed in USN-8018-2 highlight the risks associated with improper email header parsing and regression issues in widely used programming libraries such as Python. The primary concern, CVE-2026-0865, affects WSGI header handling and could disrupt web applications, while CVE-2025-15366 and CVE-2025-15367 relate to email header parsing weaknesses.
Organizations using Python-based applications or email processing services should prioritize updating affected Ubuntu packages to ensure both security and application stability.
References:

Recent Comments