Open Source Developers are Targeted in an active Social Engineering Campaign via Slack
Threat Actors impersonating as Linux Foundation leader in an active social engineering campaign targeting open source developers via Slack.
Now, a fresh Open Source Security Foundation (OpenSSF) advisory warns unknown attackers are using a similar approach to target other open source developers.
The human connection has been leveraged to target software.
The attackers interacted via Slack or social media platform LinkedIn, posing as company owners/representatives, job recruiters, or podcast hosts, and tried to lure developers into downloading malware mimicking as a videoconferencing software update, a type of phishing campaign.
Key facts
- Attackers impersonated a Linux Foundation leader in Slack to target open source developers.
- Victims were tricked into entering credentials and installing a malicious “Google certificate.”
- The phishing campaign used AI-themed lures and legitimate services like Google Sites to appear credible.
- Attack techniques varied by operating system, enabling interception of encrypted traffic on both macOS and Windows.
- Security experts urge developers to verify identities and avoid installing unsolicited certificates or running unknown scripts.
Crafting of attack via social engineering
First step, attackers began with a scheming social engineering ploy
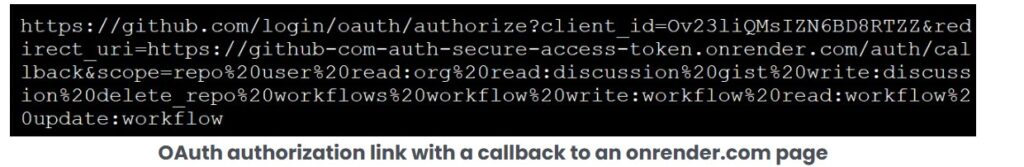
They joined Slack workspaces linked to the Linux Foundation’s TODO Group and then imitated a trusted community figure and sent direct messages to developers which looked like any legitimate invite – complete with a Google Sites link, fake email address and exclusive “access key” – to test a purported AI tool for predicting open source contribution acceptance.
Second step, once a victim clicked, they landed on a phishing page impersonating a Slack workspace invitation, prompting them to enter their email and a verification code. Instructions came in form to install what was described as a “Google certificate” from attackers side.
This was basically a malicious root certificate that allowed attackers the ability to intercept and read encrypted traffic – a devastating breach of privacy and security.
The attack module is sophisticated did not end there.
Consecutively on macOS, a script silently downloaded and executed a binary called “gapi,” potentially opening the door to full system compromise.
Windows users faced a browser-based certificate installation, equally effective at undermining secure communications. The attackers’ use of trusted infrastructure such as Google Sites allowed them to evade basic security checks and blend in with legitimate traffic.
Changing attack scenario in social engineering
Now open sources developers have become prime targets, with recent campaigns also hitting maintainers of projects like Fastify, Lodash, and Node.js.
Posing as the Linux Foundation leader, the attacker described how an AI tool can analyze open source project dynamics and predict which code contributions .
The attack was first brought to public attention on April 7, 2026, posted to the OpenSSF Siren mailing list by Christopher “CRob” Robinson, Chief Technology Officer and Chief Security Architect at the Open Source Security Foundation (OpenSSF).
Focus Shift from code repositories to human connections
Attackers now confidently targeting not only code repositories and networks that expanded over trust, but exploiting the personal trust networks that underpin open source collaboration. The expansion of open source ecosystem reminds to be more vigilant as attackers are evolving tactics and developers must now defend code and connections both.
The OpenSSF advisory :
The OpenSSF urges heightened vigilance: always verify identities through separate channels, never install certificates from untrusted sources, and treat unexpected security prompts with skepticism. If compromise is suspected, immediate network isolation and credential rotation are critical.
Sources: Social engineering attacks on open source developers are escalating – Help Net Security




Recent Comments