High-Severity SMB Server Flaws (CVE-2024-56626 & CVE-2024-56627) in Linux Kernel
High-Severity SMB Server Flaws (CVE-2024-56626 & CVE-2024-56627) in Linux Kernel
Jordy Zomer, a Security researcher have recently discovered two critical vulnerabilities in KSMBD, the in-kernel SMB server for Linux. These vulnerabilities, CVE-2024-56626 and CVE-2024-56627, could allow attackers to gain control of vulnerable systems.
SUMMARY
| OEM | Linux |
| Severity | High |
| CVSS | 7.8 |
| CVEs | CVE-2024-56626, CVE-2024-56627 |
| Exploited in Wild | No |
| Publicly POC Available | Yes |
| Patch/Remediation Available | Yes |
| Advisory Version | 1.0 |
These vulnerabilities affect Linux kernel versions greater than 5.15 and have been addressed in version 6.13-rc2. Proof-of-concept (PoC) exploits have been publicly released, emphasizing the critical nature of these issues.
| Vulnerability Name | CVE ID | Product Affected | Severity | Affected Version |
| Out-of-bounds write vulnerability in ksmbd. | CVE-2024-56626 | Linux | High | Linux kernel versions greater than 5.15 |
| Out-of-bounds read vulnerability in ksmbd. | CVE-2024-56627 | Linux | High | Linux kernel versions greater than 5.15 |
Technical Summary
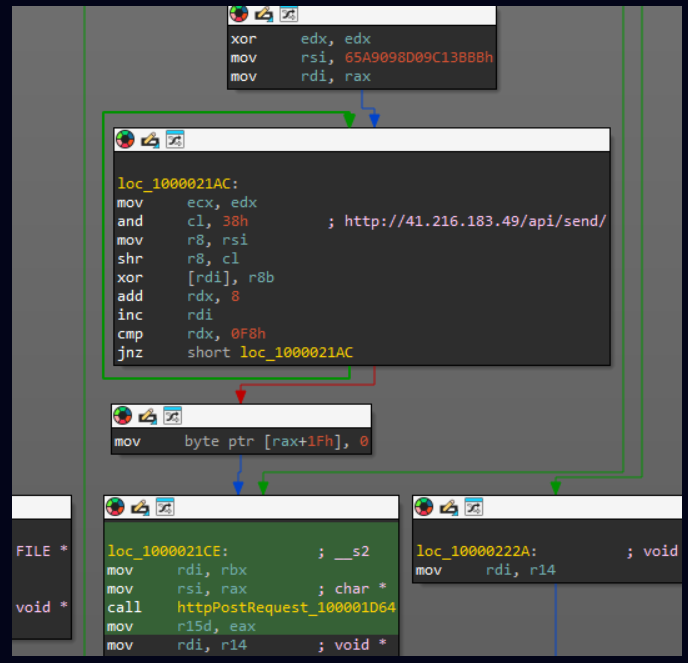
| CVE ID | System Affected | Vulnerability Details | Impact |
| CVE-2024-56626 | Linux Kernel | A vulnerability in ksmbd’s ksmbd_vfs_stream_write allowed negative offsets from clients, causing out-of-bounds writes and potential memory corruption. It was triggered when using vfs objects = streams_xattr in ksmbd.conf. The issue has been fixed in recent kernel updates. | Attackers can execute arbitrary code with kernel privileges |
| CVE-2024-56627 | Linux Kernel | A vulnerability in ksmbd’s ksmbd_vfs_stream_write allowed negative client offsets, enabling out-of-bounds writes and potential memory corruption. This issue occurred when the vfs objects = streams_xattr parameter was set in ksmbd.conf and has been resolved in recent kernel updates. | Attackers can read sensitive kernel memory, leading to information disclosure |
Remediation:
- Update: Ensure that the appropriate patches or updates are applied to the relevant versions
listed below
| Version | Fixes and Releases |
| kernel version > 5.15 | kernel version 6.13-rc2 |
Conclusion:
The discovery of CVE-2024-56626 and CVE-2024-56627 highlights critical security flaws in the Linux kernel’s SMB server implementation. Given the availability of proof-of-concept exploits, immediate action is essential to protect systems from potential exploitation. Regularly updating systems and applying security patches are vital practices to maintain a secure environment.
References:
















Recent Comments