OpenCTI Web-Hook Flaw Enables Full System Compromise
Summary
| OEM | Filigran |
| Severity | Critical |
| CVSS Score | 9.1 |
| CVEs | CVE-2025-24977 |
| Actively Exploited | No |
| Exploited in Wild | No |
| Advisory Version | 1.0 |
Overview
A critical vulnerability (CVE-2025-24977) in the OpenCTI Platform allows authenticated users with specific permissions to execute arbitrary commands on the host infrastructure, leading to potential full system compromise.
| Vulnerability Name | CVE ID | Product Affected | Severity | Fixed Version |
| Webhook Remote Code Execution vulnerability | CVE-2025-24977 | OpenCTI | Critical | 6.4.11 |
Technical Summary
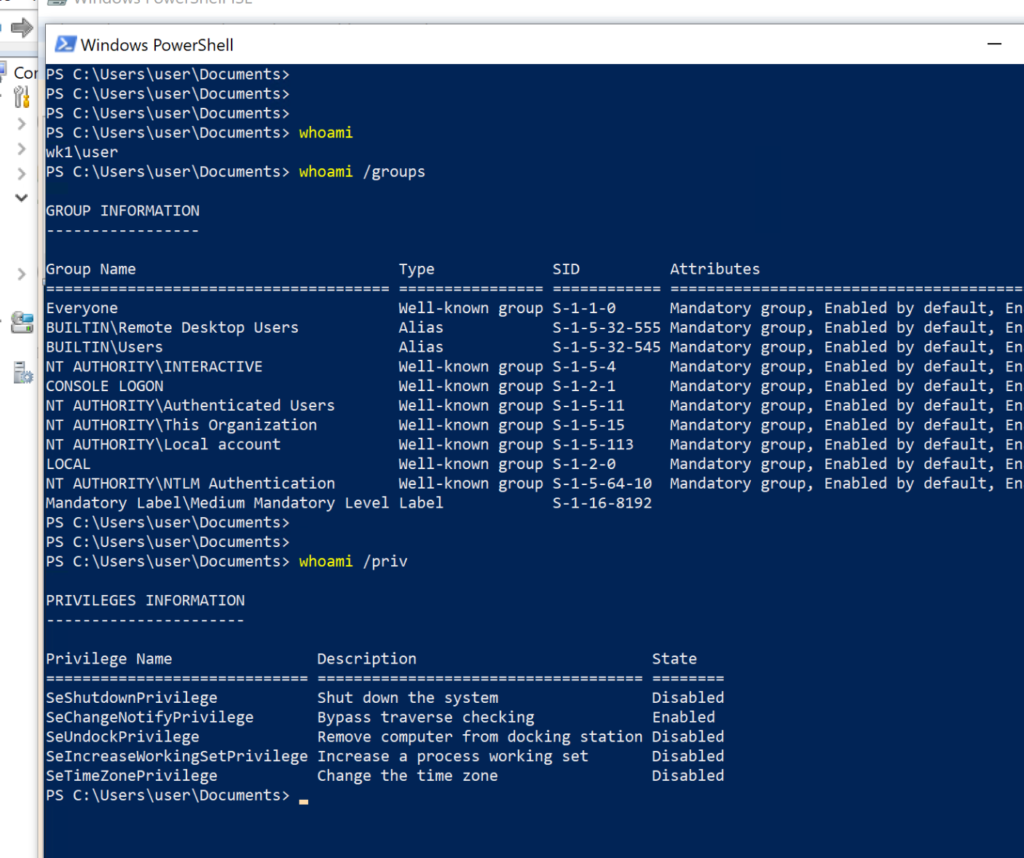
The vulnerability resides in OpenCTI’s webhook templating system, which is built on JavaScript. Users with elevated privileges can inject malicious JavaScript into web-hook templates.
Although the platform implements a basic sandbox to prevent the use of external modules, this protection can be bypassed, allowing attackers to gain command execution within the host container.
Due to common deployment practices using Docker or Kubernetes, where environment variables are used to pass sensitive data (eg: credentials, tokens), exploitation of this flaw may expose critical secrets and permit root-level access, leading to full infrastructure takeover.
| CVE ID | System Affected | Vulnerability Details | Impact |
| CVE-2025-24977 | OpenCTI (≤ v6.4.10) | The webhook feature allows JavaScript-based message customization. Users with manage customizations permission can craft malicious JavaScript in templates to bypass restrictions and execute OS-level commands. Since OpenCTI is often containerized, attackers can gain root access and extract sensitive environment variables passed to the container. | Root shell access in the container, exposure of sensitive secrets, full system compromise, lateral movement within infrastructure. |
Remediation:
- Upgrade: Immediately update to OpenCTI version 6.4.11 or later.
- Restrict user permissions: Especially the manage customizations capability — limit access to trusted personnel only.
- Review and audit: Existing webhook configurations for signs of misuse, unauthorized scripts, or suspicious behavior.
- Implement container hardening practices: Reduce risk of secret exposure by:
- Avoiding storage of secrets in environment variables when possible.
- Using dedicated secret management tools.
- Running containers with least privilege and limiting runtime capabilities.
The misuse can grant the attacker a root shell inside a container, exposing internal server-side secrets and potentially compromising the entire infrastructure.
Conclusion:
CVE-2025-24977 presents a highly exploitable attack vector within the OpenCTI platform and must be treated as an urgent priority for remediation.
The combination of remote code execution, privileged access and secret exposure in containerized environments makes it especially dangerous.
Organizations leveraging OpenCTI should upgrade to the latest version without delay, review their deployment security posture, and enforce strict access control around webhook customization capabilities.
References: