Gladinet Triofox Patched Critical Unauthenticated Remote Access Vulnerability
Summary : A critical unauthenticated access vulnerability in Triofox is being actively exploited in the wild by threat actor UNC6485. Attackers exploit a Host header spoofing vulnerability to bypass authentication, create native admin accounts and chain abuse of the built-in antivirus feature to execute arbitrary code under SYSTEM privileges.
| OEM | Gladinet |
| Severity | Critical |
| CVSS Score | 9.1 |
| CVEs | CVE-2025-12480 |
| POC Available | YES |
| Actively Exploited | YES |
| Exploited in Wild | YES |
| Advisory Version | 1.0 |
Overview
Triofox is an enterprise file-sharing and remote access platform by Gladinet that enables secure file sync, sharing, and collaboration across on-premises and cloud environments. Immediate upgrade is mandatory to prevent full system compromise, ransomware and persistent remote access.
| Vulnerability Name | CVE ID | Product Affected | Severity | Fixed Version |
| Unauthenticated Access via Host Header Spoofing & Antivirus RCE Chain | CVE-2025-12480 | Triofox | Critical | v16.7.10368.56560 or later |
Technical Summary
The vulnerability in the CanRunCriticalPage() function within GladPageUILib.dll, which allows access to setup pages, if the Host header is “localhost” – without validating the request origin. Attackers spoof this header externally to initiate the setup process, create a Cluster Admin account, and gain authenticated access.
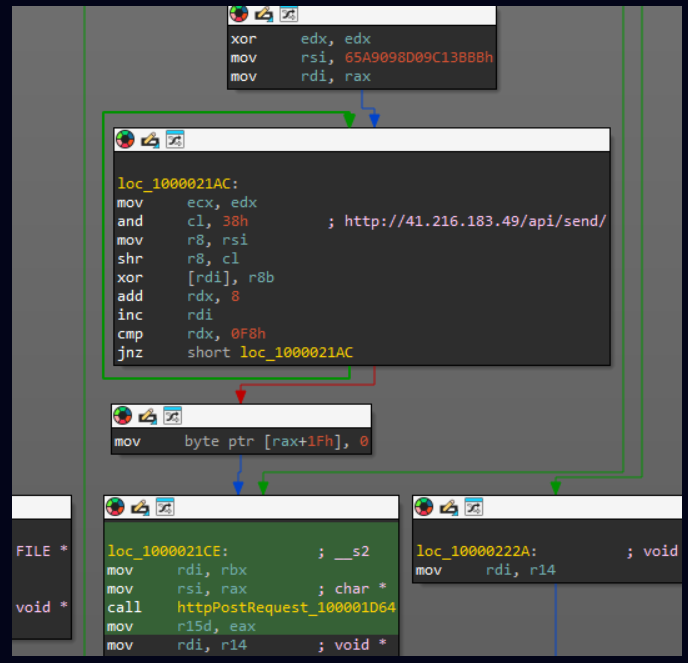
Once logged in, attackers exploit the antivirus configuration feature, which allows arbitrary executable paths. By uploading a malicious script to a shared folder and setting it as the antivirus scanner, the file executes with SYSTEM-level privileges inherited from the Triofox service.
| CVE ID | System Affected | Vulnerability Details | Impact |
| CVE-2025- 12480 | Triofox < 16.7.10368.56560 | Host header attack bypasses authentication to AdminDatabase.aspx that enables admin account creation. Chained with antivirus path abuse to run uploaded payloads as SYSTEM | Authentication Bypass, Admin Account Creation, Remote Code Execution, Full System Compromise, Persistent Access, Data Exfiltration, Lateral Movement |
Indicators of Compromise (IOCs)
Host-Based Artifacts
| Artifact | Description | SHA-256 Hash |
| C:\Windows\appcompat\SAgentInst aller_16.7.10368.56560.exe | Installer containing Zoho UEMS Agent | 43c455274d41e58132be7f66139566a941190ceba46082eb 2ad7a6a261bfd63f |
| C:\Windows\temp\sihosts.exe | Plink | 50479953865b30775056441b10fdcb984126ba4f98af4f647 56902a807b453e7 |
| C:\Windows\temp\silcon.exe | PuTTy | 16cbe40fb24ce2d422afddb5a90a5801ced32ef52c22c2fc7 7b25a90837f28ad |
| C:\Windows\temp\file.exe | AnyDesk | ac7f226bdf1c6750afa6a03da2b483eee2ef02cd9c2d6af71e a7c6a9a4eace2f |
| C:\triofox\centre_report.bat | Attacker batch script filename | N/A |
Network-Based Artifacts
| IP Address | ASN | Description |
| 85.239.63[.]37 | AS62240 – Clouvider Limited | IP address of the attacker used to initially exploit CVE-2025-12480 to create the admin account and gain access to the Triofox instance |
| 65.109.204[.]197 | AS24950 – Hetzner Online GmbH | After a dormant period, the threat actor used this IP address to login back into the Triofox instance and carry out subsequent activities |
| 84.200.80[.]252 | AS214036 – Ultahost, Inc. | IP address hosting the installer for the Zoho UEMSAgent remote access tool |
| 216.107.136[.]46 | AS396356 – LATITUDE-SH | Plink C2 |
Source: cloud.google.com
Recommendations:
Upgrade Triofox to version 16.7.10368.56560 or latest from the official Gladinet portal.
Conclusion:
This vulnerability represents a severe supply-chain risk in enterprise file-sharing platforms, enabling zero-authentication RCE through misconfigured access controls and feature abuse. With active in-the-wild exploitation by UNC6485 and rapid post-patch attacks, delayed patching significantly increases breach likelihood.
Immediate upgrade, log monitoring, and network hardening are essential to prevent ransomware deployment, data theft, and network pivoting. This incident reinforces the need for secure-by-design input validation and principle of least privilege in remote access tools.
References:




Recent Comments