Privilege Escalation in Notepad++ v8.8.1 Installer via Binary Planting with Public PoC Available
Security Advisory: A high-severity privilege escalation vulnerability has been discovered in the Notepad++ v8.8.1 and prior installer, which allows local attackers to gain SYSTEM-level privileges through uncontrolled executable search paths (binary planting).
The installer searches for executable dependencies in the current working directory without verification, allowing attackers to place malicious executables that will be loaded with SYSTEM privileges during installation.
| OEM | Notepad++ |
| Severity | High |
| CVSS Score | 7.3 |
| CVEs | CVE-2025-49144 |
| POC Available | Yes |
| Actively Exploited | No |
| Exploited in Wild | No |
| Advisory Version | 1.0 |
Overview
Exploitation requires minimal user interaction and a public Proof of Concept (PoC) is available. The issue is resolved in version v8.8.2.
| Vulnerability Name | CVE ID | Product Affected | Severity | Fixed Version |
| Privilege Escalation Vulnerability | CVE-2025-49144 | Notepad++ | High | v8.8.2 |
Technical Summary
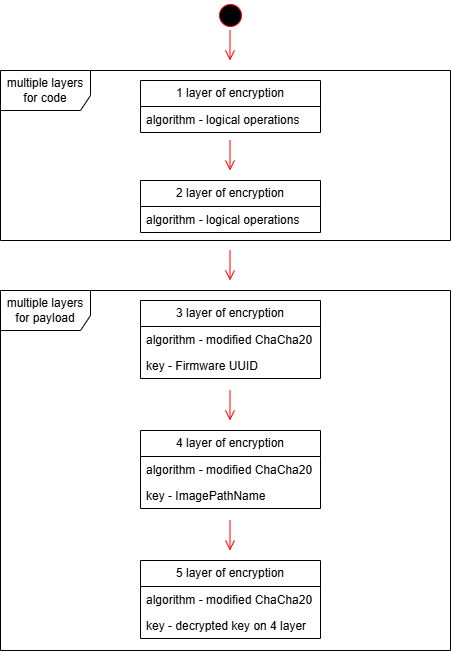
The Notepad++ installer improperly searches for executable dependencies in the current directory without verifying their authenticity.
This insecure behavior allows attackers to place a malicious executable (e.g. regsvr32.exe) in the same directory as the installer. Upon execution the malicious file is loaded with SYSTEM-level privileges, granting full control over the machine.
In real world scenario, an attacker could use social engineering or clickjacking to trick users into downloading both the legitimate installer and a malicious executable to the same directory (typically Downloads folder – which is known as Vulnerable directory). Upon running the installer, the attack executes automatically with SYSTEM privileges.
| CVE ID | System Affected | Vulnerability Details | Impact |
| CVE-2025-49144 | Notepad++ v8.8.1 and prior. | The installer invokes executables without absolute path (e.g. regsvr32), allowing a malicious binary in the same directory to be executed with elevated privileges. | SYSTEM privilege escalation and full machine control |
Proof of Concept (PoC):
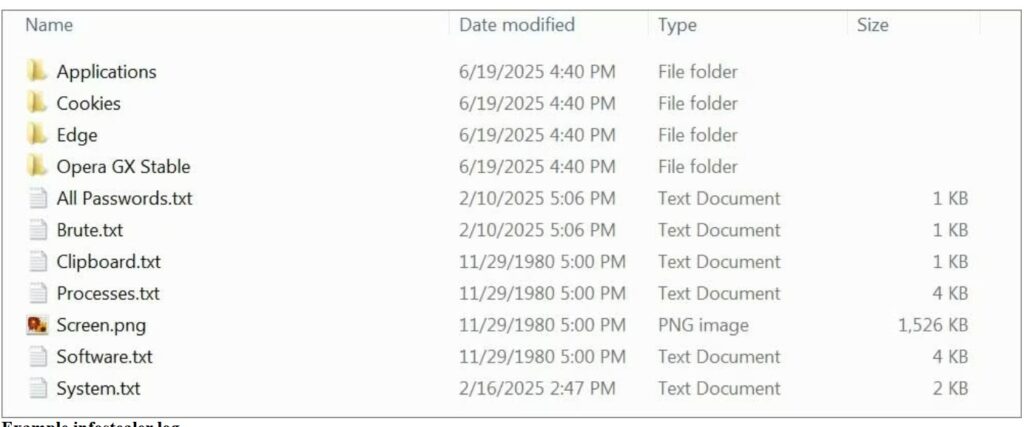
- Execution Flow: Attacker places a fake regsvr32.exe in the same directory as the Notepad++ installer.
- Trigger: When the user runs the installer, it loads the attacker’s file with SYSTEM privileges.
- Evidence:
- Process Monitor logs confirm that the installer is searching for executables in the local directory.
- A video demonstration confirms successful SYSTEM-level access via reverse shell.
- Public PoC materials are hosted and shared, confirming reproducibility
Remediation:
- Immediate Action: Upgrade to Notepad++ v8.8.2 or later which explicitly sets absolute paths when invoking executables like regsvr32.
Recommendations:
- Configuration Check: Avoid executing installers from user-writable locations like the Downloads folder. Ensure installers are run from isolated, trusted directories.
- Best Practice: Adopt Microsoft’s secure library and binary loading practices.
- Environment Hardening: Implement endpoint detection for binary planting, restrict execution in commonly targeted directories.
Conclusion:
CVE-2025-49144 is a critical privilege escalation vulnerability with a working public PoC. It leverages a fundamental flaw in the Notepad++ installer’s handling of executable paths.
Given the low barrier to exploit and high impact, especially in environments where Notepad++ is widely used, immediate remediation is strongly advised. The presence of similar flaws in past versions highlights the persistent risk of insecure software packaging.
This is a critical security vulnerability requiring immediate attention. While Microsoft classifies some binary planting issues as “Defense-in-Depth,” the severity of gaining SYSTEM privileges with minimal user interaction warrants priority remediation.
References: