Critical Fortinet Vulnerability in FortiCloud SSO Authentication Bypass
FortiCloud Single Sign-On (SSO)
Continue ReadingFortiCloud Single Sign-On (SSO)
Continue ReadingA large-scale phishing campaign has targeted nearly 12,000 GitHub repositories with phony security alerts, reported BleepingComputers.
The alerts, opened as issues on the repositories, inform users of unauthorized login attempts and provide links to change their passwords, review active sessions, or set up MFA.
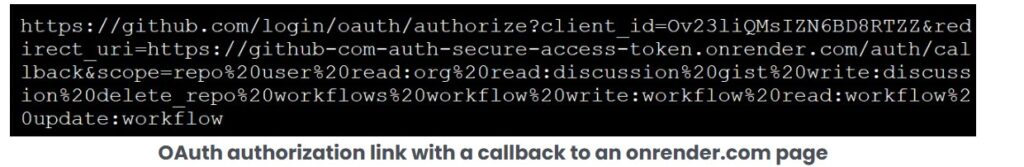
If a user clicks any of these links, they’ll be taken to a GitHub authorization page for an OAuth app that will grant the attacker control of the account.
The campaign is ongoing, though GitHub appears to be responding to the attacks.
Users were directed to all links within the message to a GitHub authorization page for a malicious OAuth application called “gitsecurityapp.” If authorized, the app grants attackers full control over the user’s account and repositories, including the ability to delete repositories, modify workflows, and read or write organization data.
This consistent messaging across all affected repositories aims to create a sense of urgency and panic, prompting developers to take immediate action.
The fraudulent alert directs users to update their passwords, review active sessions, and enable two-factor authentication. However, these links lead to a GitHub authorization page for a malicious OAuth app named “gitsecurityapp.”
Upon authorization, an access token is generated and sent to various web pages hosted on onrender.com, granting the attacker full control.
(Image courtesy: Bleeping Computers)
The attack, which was first detected on March 16, remains active, though GitHub appears to be removing affected repositories.
Pointers Developers to take key inputs from this incident.
Last week, a supply chain attack on the tj-actions/changed-files GitHub Action caused malicious code to write CI/CD secrets to the workflow logs for 23,000 repositories.
If those logs had been public, then the attacker would have been able to steal the secrets.
The tj-actions developers cannot pinpoint exactly how the attackers compromised a GitHub personal access token (PAT) used by a bot to perform malicious code changes as per threat researchers.
Key pointers for User saftey:
Wiz suggests that potentially impacted projects run this GitHub query to check for references to reviewdog/action-setup@v1 in repositories.
If double-encoded base64 payloads are found in workflow logs, this should be taken as a confirmation their secrets were leaked.
Developers should immediately remove all references to affected actions across branches, delete workflow logs, and rotate any potentially exposed secrets.
(Sourece: Bleeping computers)
GitLab releases fixes for vulnerabilities in patch releases. There are two types of patch releases: scheduled releases, and ad-hoc critical patches for high-severity vulnerabilities.
Summary
| OEM | Gitlab |
| Severity | High |
| CVEs | CVE-2024-5655, CVE-2024-6385, CVE-2024-6678, CVE-2024-8970, CVE-2025-0194, CVE-2024-6324, CVE-2024-12431, CVE-2024-13041 |
| Exploited in Wild | No |
| Patch/Remediation Available | Yes |
| Advisory Version | 1.0 |
Overview
The vulnerabilities could potentially impact unauthorized access, data manipulation, and service disruption. These have been disclosed through GitLab’s HackerOne bug bounty program. Latest Versions 17.7.1, 17.6.3, and 17.5.5 are now available for immediate download and upgrade to address these issues.
| Vulnerability Name | CVE ID | Product Affected | Severity |
| Import Functionality Vulnerabilities | CVE-2024-6385 | GitLab CE/EE | Critical |
| Import Functionality Vulnerabilities | CVE-2024-5655 | GitLab CE/EE | High |
| Import Functionality Vulnerabilities | CVE-2024-6678 | GitLab CE/EE | High |
| Import Functionality Vulnerabilities | CVE-2024-8970 | GitLab CE/EE | High |
| Access Token Exposure in Logs | CVE-2025-0194 | GitLab CE/EE | Medium |
| Cyclic Reference of Epics Leading to DoS | CVE-2024-6324 | GitLab CE/EE | Medium |
| Unauthorized Manipulation of Issue Status | CVE-2024-12431 | GitLab CE/EE | Medium |
| Instance SAML Bypass | CVE-2024-13041 | GitLab CE/EE | Medium |
Technical Summary
This update addresses several significant vulnerabilities identified in GitLab CE/EE:
| CVE ID | System Affected | Vulnerability Details | Impact |
| CVE-2024-6385 | GitLab CE/EE | Vulnerability in import functionality allowing potential exploitation | Allows attackers to exploit the system. |
| CVE-2024-5655 | |||
| CVE-2024-6678 | |||
| CVE-2024-8970 | |||
| CVE-2025-0194 | GitLab CE/EE | Possible exposure of access tokens in logs under certain conditions. | Potential unauthorized access to sensitive resources. |
| CVE-2024-6324 | GitLab CE/EE | Cyclic references between epics could lead to resource exhaustion, causing a Denial of Service (DoS). | Service disruption due to resource exhaustion. |
| CVE-2024-12431 | GitLab CE/EE | Unauthorized users could manipulate issue statuses in public projects, potentially disrupting workflows. | Workflow disruption and compromised data integrity. |
| CVE-2024-13041 | GitLab CE/EE | Flaw in instance SAML configuration allowing bypass of external provider settings. | Unauthorized access to internal projects or groups. |
Key Changes to Import Functionality:
Remediation:
Conclusion:
The vulnerabilities addressed in this patch release highlight the importance of timely updates and proactive security measures. GitLab’s redesign of its import functionality and the prompt patch release demonstrate a commitment to user security. Upgrading to the latest patched versions and adhering to the recommended actions is critical to maintaining a secure environment.
References:

Image
New CheckPoint research discovered a new remote access trojan and information stealer used by Iranian state-sponsored actors to conduct reconnaissance of compromised endpoints and execute malicious commands.
Continue Reading
Recent Comments