Zero-Day Threat in Chrome’s Loader Component (CVE-2025-4664) – CISA Flags Urgent Risk
Summary : A zero-day vulnerability (CVE-2025-4664) in Google Chrome’s Loader component has been actively exploited in the wild.
| OEM | |
| Severity | Medium |
| CVSS Score | 4.3 |
| CVEs | CVE-2025-4664 |
| Actively Exploited | Yes |
| Exploited in Wild | Yes |
| Advisory Version | 1.0 |
Overview
This flaw allows attackers to bypass security policies, leak cross-origin data, and potentially execute unauthorized code. CISA has added this vulnerability to its Known Exploited Vulnerabilities (KEV) catalog, urging immediate patching.
| Vulnerability Name | CVE ID | Product Affected | Severity | Fixed Version |
| Insufficient Policy Enforcement vulnerability | CVE-2025-4664 | Google Chrome | Medium | 136.0.7103.113/.114 (Win/Mac), 136.0.7103.113 (Linux) |
Technical Summary
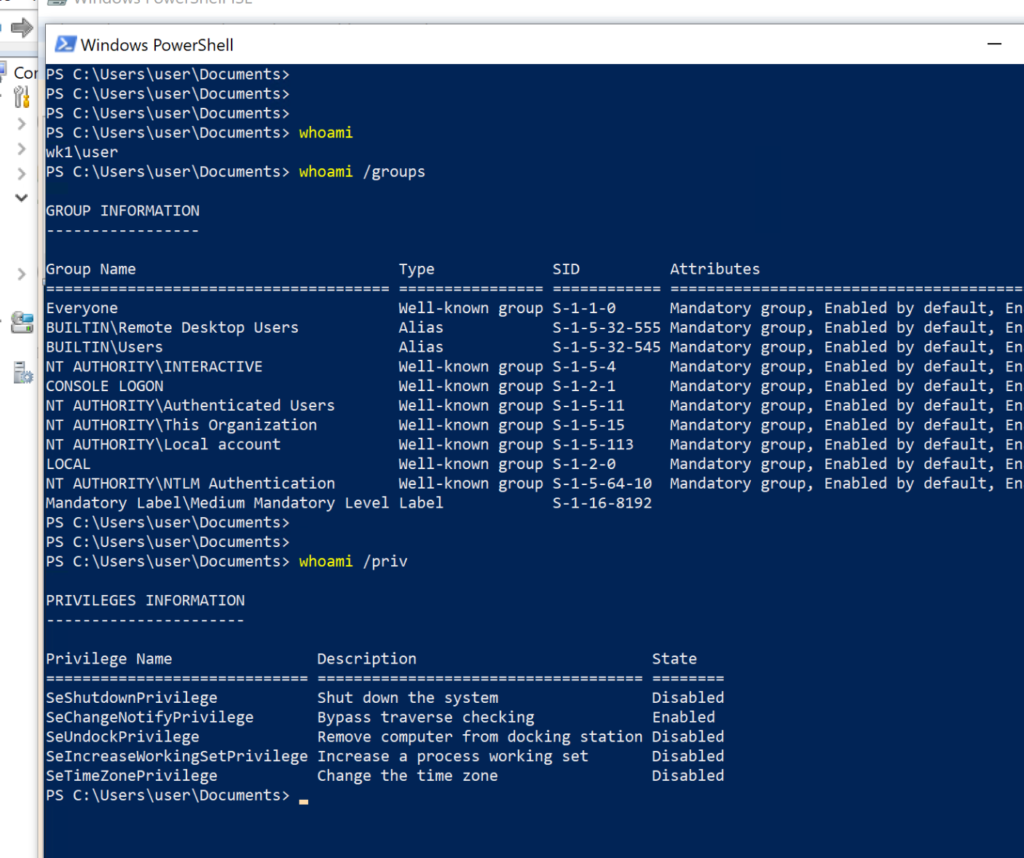
CVE-2025-4664 is a zero-day vulnerability found in the Chrome Loader component due to insufficient policy enforcement.
It enables remote attackers to bypass browser security controls using crafted HTML content, possibly leaking cross-origin data or achieving sandbox escape. The bug has been actively exploited in the wild.
A second high-severity flaw, CVE-2025-4609, was also addressed in this update, involving an incorrect handle in the Mojo IPC layer, which can lead to memory corruption or privilege escalation.
| CVE ID | System Affected | Vulnerability Details | Impact |
| CVE-2025-4664 | Chrome (Windows, Mac, Linux) | Insufficient policy enforcement in Loader enables cross-origin data leaks via crafted HTML. | Data leakage, sandbox escape, potential code execution |
Remediation:
- Update Chrome: Google has released security updates to address these vulnerabilities. Users and administrators must apply the latest Chrome versions:
- Windows/macOS: Chrome 136.0.7103.113 /136.0.7103.114 or later
- Linux: Chrome 136.0.7103.113 or later
Conclusion:
The active exploitation of CVE-2025-4664 highlights the urgent need for rapid security response and patch management. With acknowledgment from CISA and public disclosure by @slonser_, this zero-day poses a real and present threat to users of Chrome and other Chromium-based browsers.
Organizations should take immediate action to patch affected systems and monitor for signs of compromise.
Regular browser updates and proactive vulnerability management are essential to mitigating such critical security risks.
References: