Deepfake’s pose a Challenge as Cyber-risk Increase
The Digital world is witnessing constant increase in threats from Deepfakes, a challenge for cyber leaders as cybersecurity related risk increase and digital trust.
Deepfakes being AI generated is much used by cybercriminals with intentions to bypass authenticated security protocols and appears realistic but fakes, often posing challenges to detect being generated via AI. We have three types of Deepfakes i.e. voice fakes or Audio, Deep Video maker fakes and shallow fakes or editing software like photoshop.
Growing Cyber Risk due to Deep Fakes
Due to these Deep fakes , which are quiet easier and more realistic to create, there has been deterioration of trust, propagation of misinformation that can be used widely and has potential to damage or conduct malicious exploitation across various domains across the industry verticals.
The cybersecurity industry has always came forward and explained what can be potential risk posed by Deep fakes and possible route to mitigate the risks posed by deepfakes, emphasizing the importance of interdisciplinary collaborations between industries. This will bring in proactive measures to ensure digital authenticity and trust in the face of evolving cyber frauds.
Failing to recognize a deep fake pose negative consequence both for individuals and organizational risk and this can be unable to recognize audio fakes or video fakes. The consequences can be from loss of trust to disinformation. From negative media coverage to falling prey to potential lawsuits and other legal ramifications and we cannot undermine cybersecurity related threats and phishing attacks.
There are case when Deep fakes have been ethically used but the numbers are less compare to malicious usage by cyber criminals. Synthetic media also termed as Deep fakes are created using deep learning algorithms, particularly generative adversarial networks (GANs).
These technologies can seamlessly swap faces in videos or alter audio, creating hyper-realistic but fabricated content. In creative industries, deepfakes offer capabilities such as virtual acting and voice synthesis.
Generative Adversarial Networks (GANs) consists of two neural networks: a generator and a discriminator.
- Generator: In this case the network creates synthetic data, such as images or videos from any random sound alert and mimic real data.
- Discriminator generally evaluates the generated content against real data.
Deepfakes uses deep learning algorithms to analyze and synthesize visual and audio content which are painful task to determine the real ones, posing significant challenge to ethical security concerns.
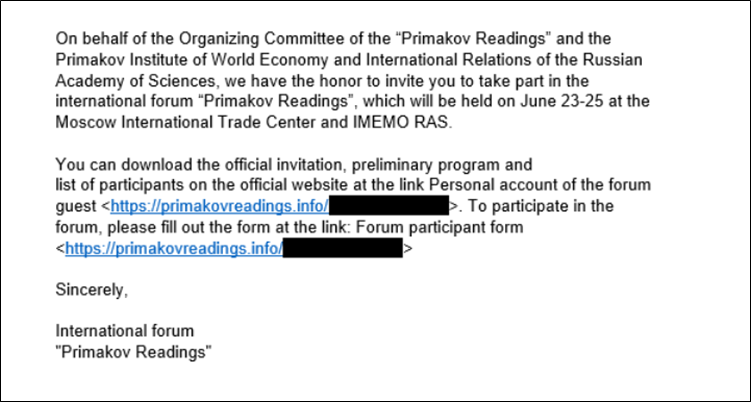
While posing threats Deep fakes also provide another gateway for cyber attack specifically Phishing attacks. Tricking victims or impersonating an individual or an entity may open doors for revealing sensitive information and threat to data security.
The audios created via Deepfake could be used to bypass voice recognition systems giving attackers access to secure systems and invading personal privacy.
Uses cases in Deepfakes to understand the reach and impact:
Scammers and Fraudsters can benefit as Deepfakes can develop audio replication and use them for malicious intent like asking financial help from individuals they encounter or voice clone as some important person and demand or extort money.
Identity Theft is often overlooked and this impacts mostly financial institutions and scammers can easily bypass such authentication by cloning voices. Scammers also may easily develop convincing replicas of government ID proofs to gain access to business information or a misuse it as a customer.
Fusing images of high profile public figures with offensive images by employing deepfake technology without their knowledge by criminals and hackers are growing each day . This kind of act can eventually lead to demanding money by cyber criminals or face consequences leading to defaming.
Conspiracy against governments or national leaders by faking their image or creating false hoax where the image or voice is used by cyber criminals often hired by opposing systems in place to disturb peace and harmony and also sound business operations.
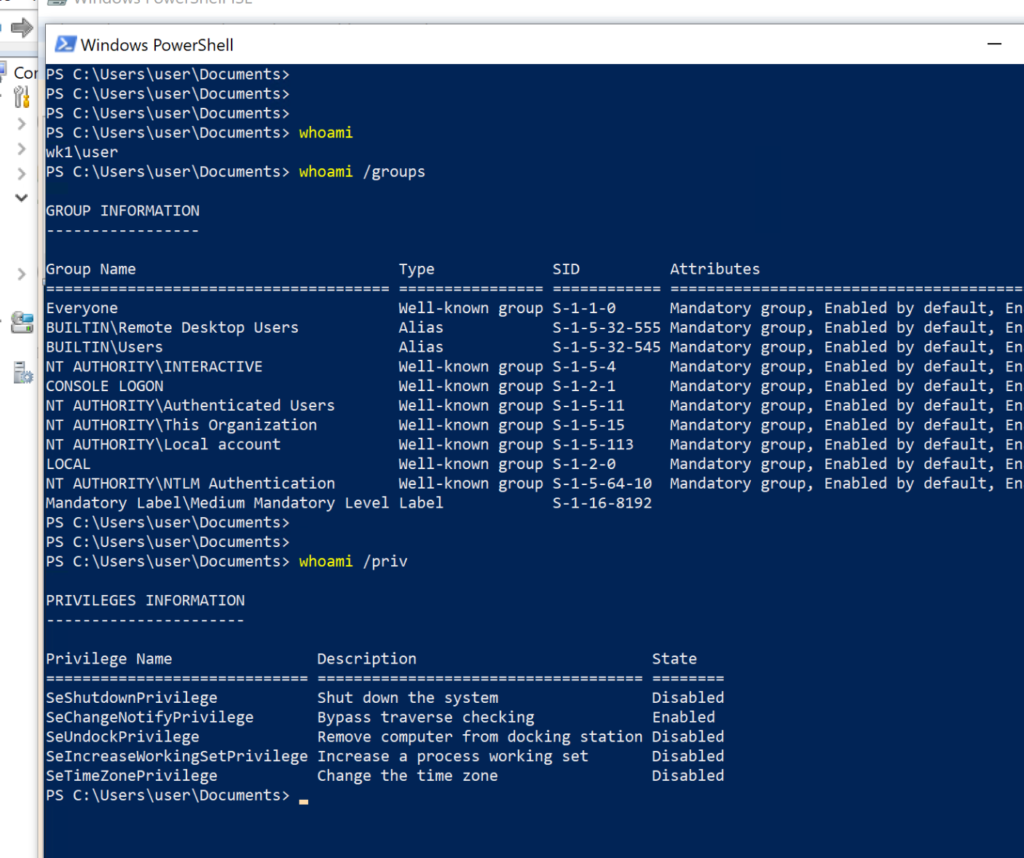
Email are the key entry point for cyberattacks and presently we see deepfake technology being used by cyber criminals to create realistic phishing emails. These emails bypass conventional security filters an area we cannot afford to neglect.
How will you detect Deep fakes?
Few technicalities are definitely there that may not be recognizable but there are few minute and hairsplitting details.
In Video fakes its often seen no movement in the eye or unnatural facial expression. The skin colour may be sightly different and in-consistent body positioning including the mismatch lip-syncing and body structure and face structure not similar as what we used to witness or accustomed viewing.
Being a grave concern from cyber security perspective its important to remain alert on new evolving technologies on Deep fakes and know their usage to defend on all frontiers both at individual and organizational level.
As Deep fakes are AI driven and rising phishing attacks that imbibe deep fakes pose a challenge where in mostly social media profile are used. The available AI-enabled computers allow cybercriminals to use chatbots no body can detect as fake.
Mitigating the Digital Threat
- Organizations or individuals require robust security measures to implement AI-based security solutions and develop improved knowledge of phishing methods in order to tackle the digital threat.
- Remaining proactive in all level of cyber security to navigate the complex challenge of Deep fakes is important, while Deep fakes defiantly poses strong technical challenge but proactive cybersecurity practices can stop cybercriminals from luring victims in their trap.
- Government bodies and tech institutions or organizations that are tech savy to have more collaborative efforts to recognize deep fakes and effectively deal with challenges.
- The various regulations and more recently the DORA (Digital Operational Resilience Act ), will help navigate these challenges as more investments in open sources security will rise by countries and organizations.
- Major investments in AI-driven detection tools are being soughed after at enterprise level, those having stronger authentication mechanisms and improved digital literacy are critical to mitigating these emerging threats.
- Investing in Email security service that offers automated protection will assist in blocking major phishing attempts
As per KPMG report, Deepfakes may be growing in sophistication and appear to be a daunting threat. However, by integrating deepfakes into the company’s cybersecurity and risk management, CISOs in assosiations with CEO, and Chief Risk Officers (CRO) – can help their companies stay one step ahead of malicious actors.
This calls for a broad understanding across the organization of the risks of deepfakes, and the need for an appropriate budget to combat this threat.
If Deepfakes can be utilized to infiltrate an organization, the same technology can also protect it. Collaborating with deepfake cybersecurity specialists helps spread knowledge and continually test and improve controls and defenses, to avoid fraud, data loss and reputational damage.
BISO Analytics:
We at Intruceptlabs have a mission and that is to protect your organization from any cyber threat keeping confidentiality and integrity intact.
We have BISO Analytics as a service to ensure business continues while you remain secured in the world of cybersecurity. BISO’s translates concepts and connects the dots between cybersecurity and business operations and functions are in synch with cyber teams.
Sources: https://kpmg.com/xx/en/our-insights/risk-and-regulation/deepfake-threats.html
AI-Driven Phishing And Deep Fakes: The Future Of Digital Fraud