Cleo Releases Patch for Critical Vulnerabilities Exploited in the Wild
Summary
OEM | Cleo |
Severity | Critical |
CVSS score | 9.8 |
CVE | CVE-2024-55956, CVE-2024-50623 |
Exploited in Wild | Yes |
Patch/Remediation Available | Yes |
Advisory Version | 1.0 |
Overview
The Clop ransomware group has exploited critical vulnerabilities in Cleo’s Managed File Transfer (MFT) solutions, specifically targeting Cleo Harmony, VLTrader, and LexiCom. These vulnerabilities, identified as CVE-2024-50623 and CVE-2024-55956, allow unauthenticated attackers to execute arbitrary code on affected systems, leading to potential data breaches and system compromises.
Vulnerability Name | CVE ID | Product Affected | Severity | CVSS Score | Fixed Version |
Unauthenticated Command Execution | CVE-2024-55956 | Cleo products | Critical | 9.8 | 5.8.0.24 or latest |
Unrestricted File Upload/Download Vulnerability | CVE-2024-50623 | Cleo products | Critical | 9.8 | 5.8.0.24 or latest |
Technical Summary
CVE ID | System Affected | Vulnerability Details | Impact |
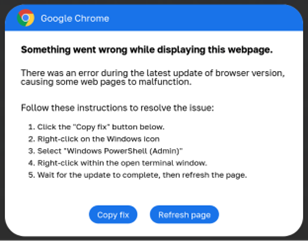
CVE-2024-55956 | Cleo Harmony, VLTrader, LexiCom | This flaw enables unauthenticated users to import and execute arbitrary Bash or PowerShell commands on the host system by leveraging the default settings of the Autorun directory. Attackers can write a ZIP file containing a malicious XML file describing a new host. The malicious XML file contained a Mailbox action associated with the new host, which when run would execute an arbitrary OS command. | Execution of arbitrary commands, resulting in full system compromise. |
CVE-2024-50623 | Cleo Harmony, VLTrader, LexiCom | This vulnerability permits unauthenticated attackers to upload and download files without restrictions via the ‘/Synchronization’ endpoint. By uploading malicious files, attackers can achieve remote code execution. The exploitation involves writing malicious code to specific files, such as “webserverAjaxSwingconftemplatesdefault-pagebody-footerVL.html”, which is then leveraged to execute an attacker-controlled payload, potentially in the form of a webshell. | Unauthorized file manipulation and potential system compromise. |
Remediations
- Update Cleo Harmony, VLTrader, and LexiCom to the updated version 5.8.0.24 or latest one.
Recommendations
- It is strongly advised to move any internet-exposed Cleo systems behind a firewall until patches are applied to prevent unauthorized exploitation.
- Disable autorun files in Cleo software by clearing the “Autorun Directory” field under “Options” to limit the attack surface; this doesn’t resolve the file-write vulnerability.
- Implement monitoring for signs of the “Cleopatra” backdoor and other malicious activities associated with Clop ransomware.
- Conduct a thorough audit of your systems to identify any malicious files or abnormal system behavior associated with Cleo software. This includes checking logs, directories, and network traffic for unusual activities related to the known exploit chain.
- If you have an EDR solution, block the attacker IPs associated with the exploit to prevent further external communication with compromised systems.
- Ensure regular backups of critical data are performed and stored securely offline to facilitate recovery in case of any ransomware attack.
IOCs
These are the attacker IP addresses embedded in the encoded PowerShell
IP Address IOCs | File IOCs |
176.123.5[.]126 | 60282967-dc91-40ef-a34c-38e992509c2c.xml |
5.149.249[.]226 | healthchecktemplate.txt |
185.181.230[.]103 | healthcheck.txt |
209.127.12[.]38 | |
181.214.147[.]164 | |
192.119.99[.]42 |
References
- https://support.cleo.com/hc/en-us/articles/28408134019735-Cleo-Product-Security-Update-CVE-2024-55956
- https://support.cleo.com/hc/en-us/articles/27140294267799-Cleo-Product-Security-Advisory-CVE-2024-50623
- https://attackerkb.com/topics/geR0H8dgrE/cve-2024-55956/rapid7-analysis
- https://www.huntress.com/blog/threat-advisory-oh-no-cleo-cleo-software-actively-being-exploited-in-the-wild